Change Management for PKI Operations
Change management for PKI sits awkwardly inside most enterprise change management frameworks. The standard ITIL-style approach assumes a change is a discrete intervention with a bounded scope and a defined rollback. PKI changes often have wide blast radius, asynchronous propagation, and rollbacks that are difficult or impossible. The result is that certificate changes are either over-controlled (every renewal goes through the change advisory board, slowing operations to a halt) or under-controlled (changes happen invisibly, with predictable surprises).
Part of: Enterprise PKI Operating Model — the pillar page for the operations library.
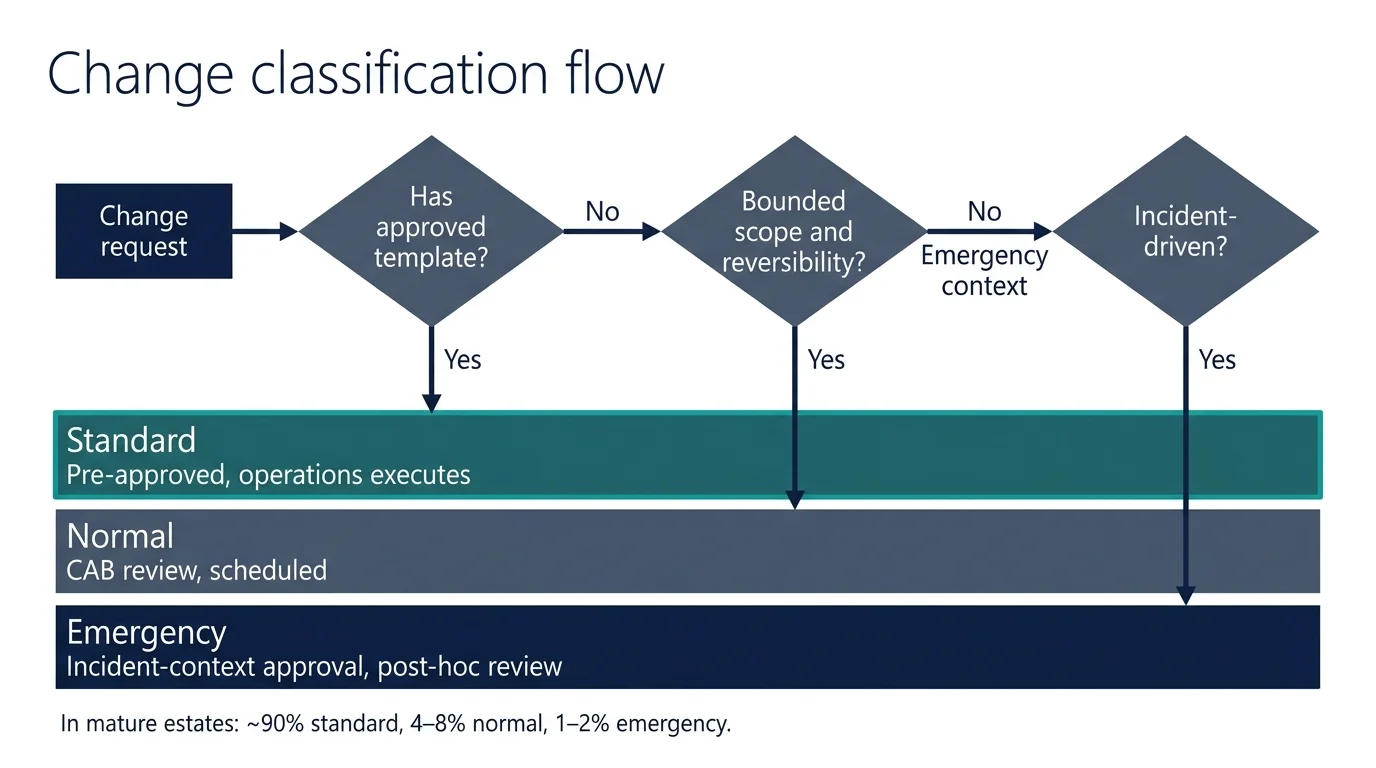
The mature operating model adapts the change management framework to the operational reality of PKI: standard changes pre-approved and automated, normal changes scheduled and reviewed at appropriate cadence, emergency changes handled at incident speed.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
The three change classifications
The standard ITIL classifications apply to PKI but require translation.
Standard changes. Pre-approved, repeatable, low-risk changes that follow a documented template. They do not require individual approval for each instance because the pattern has been approved in advance. For PKI, standard changes include:
- Certificate renewals through automated workflow for already-onboarded service classes.
- Certificate issuance for already-onboarded service classes within established policy.
- Routine trust-store updates that add CAs to the approved list (additions, not removals).
- Standard CA configuration updates (e.g., updating intermediate certificate metadata).
The defining property: the change has been done many times before, the failure modes are understood, the rollback path is documented, and the operational team has authority to execute without further approval.
Normal changes. Changes that require individual review and approval but follow established processes. For PKI, these include:
- New service onboarding to certificate automation.
- Issuance for new categories of certificate not previously approved.
- Trust-store removals (because of the wider blast radius).
- Internal CA configuration changes that affect issuance policy.
- New CA additions to the approved list.
The defining property: the change is bounded, the impact is understood, but it is sufficiently uncommon or impactful that an explicit review is appropriate.
Emergency changes. Changes that must be made urgently, typically in response to incidents. For PKI, these include:
- Replacement of a compromised certificate.
- Revocation of a certificate suspected of compromise.
- Trust-store updates in response to a CA distrust event.
- CA-level interventions during an active incident.
The defining property: waiting for the normal change-management cycle would create unacceptable risk; the change is approved in incident-response context with a documented post-hoc review.
Reasoning
- An approved template exists for this change pattern.
- Route through the standard-change framework — pre-approved, operations executes.
Verification checklist
- ☐ Confirm change matches template conditions
- ☐ Execute per documented procedure
- ☐ Active verification per template requirements
- ☐ Log execution for aggregate reporting
Why the classification matters operationally
Without explicit classification, two failure modes recur:
Over-classification of routine work. Every certificate renewal goes through change advisory board approval. With even modest certificate volume, the change advisory board becomes a bottleneck and the operations team starts working around it — either by skipping the process for low-risk changes, or by lobbying for blanket pre-approvals that don't follow the actual process. The change framework loses authority because it cannot keep up with the volume.
Under-classification of impactful work. A trust-store update is treated as routine configuration change. The change is made, services start failing across the estate, and the post-incident review discovers that the change-management process never reviewed it. The change framework loses credibility because it failed to catch the impactful changes.
The classification is the framework's mechanism for matching the level of control to the level of risk. PKI changes have to be explicitly classified.
What standard change templates look like for PKI
A standard change template documents:
The change being approved in advance. Specifically: "renewal of TLS certificates within the established issuance policy, for services in the already-onboarded service catalogue, through the combined-workflow automation, with verification by the standard renewal-verification mechanism."
The conditions under which the template applies. The template is valid only when the conditions are met. If the renewal is for a service not in the established catalogue, the template does not apply and the change becomes a normal change.
The pre-approved approver. Standard changes do not require a specific approver per instance, but they require documented authority. Typically the operations team lead has standing authority to execute changes against the approved templates.
The verification and rollback procedure. Even standard changes need verification. The template documents how successful execution is verified and what the rollback path is if verification fails.
The reporting cadence. Standard changes are not individually approved, but they are aggregated and reported to the change advisory board on a defined cadence (typically monthly). The CAB reviews aggregated execution to catch trends and outliers.
The template itself is approved through the normal change process, with a defined review cadence (typically annual) to confirm it remains appropriate.
CAB review questions — anticipated answers
These are the questions experienced CABs ask about PKI changes. Submit the template with answers already prepared to speed approval.
Generic questions
What is being changed?
TLS Certificate Renewal — Combined Workflow — Automated renewal of TLS certificates for already-onboarded service classes via the combined-workflow automation.
What is the scope of the change?
All services in the cloud-native onboarded catalogue
How is successful execution verified?
Active verification: certificate fingerprint check at the deployed endpoint; service health check via monitoring; renewal pipeline status confirmed in CLM.
What is the rollback if verification fails?
If verification fails: re-trigger renewal once. If second attempt fails: escalate to incident response. Original certificate still valid until expiry buffer is exhausted.
How often does this pattern recur?
daily — aggregate reporting will track this cadence.
Has the procedure been tested in a non-production environment?
Yes — the procedure has been exercised in non-production before approval. Test results documented and available on request.
PKI-specific questions
How does this change interact with already-issued certificates?
Already-issued certificates are unaffected by this change. The change applies only to new issuance / renewal events as they occur. No retroactive action is taken on existing certificates.
What is the propagation lag and how is it bounded?
Propagation lag depends on the deployment mechanism. For automated deployment via configuration management, propagation completes within the next config-management run cycle (typically minutes). For trust-store changes, propagation depends on the distribution mechanism — typical bound is hours to days. The verification step confirms propagation has completed at every affected location before the change is closed.
How is deployment verified end-to-end (not just at issuance)?
Verification is active and explicit: Active verification: certificate fingerprint check at the deployed endpoint; service health check via monitoring; renewal pipeline status confirmed in CLM.. The verification confirms the post-deployment state, not just the issuance event.
What is the impact on existing trust stores?
No impact on existing trust stores unless this change explicitly modifies them. If trust-store impact is involved, a separate trust-store change procedure applies (see [Trust-Store Management](/business/operations/trust-store-management/)).
What does the rollback look like for asymmetric or non-reversible aspects?
For reversible aspects: If verification fails: re-trigger renewal once. If second attempt fails: escalate to incident response. Original certificate still valid until expiry buffer is exhausted.. For non-reversible aspects (revocation propagation, certificate distribution): the rollback is replace-rather-than-revert — issuing a replacement certificate that supersedes the change rather than attempting to undo the change itself.
How does this change interact with the certificate renewal pipeline?
The change is independent of the renewal pipeline. Certificates issued under this change follow the standard renewal cycle. Where this change is itself a renewal, it operates within the established renewal buffer and verification mechanisms.
What's typical for a PKI estate
The volume distribution across change classifications, in our experience across enterprise estates:
- 90–95% of certificate changes are standard (renewals, automated issuance, trust-store additions).
- 4–8% are normal (onboarding, policy changes, trust-store removals).
- 1–2% are emergency (incident-driven).
The exact percentages vary with estate size, automation maturity, and operational practice, but the shape — heavily weighted toward standard, with a small tail of normal and a smaller tail of emergency — is consistent. Estates whose distribution differs significantly (e.g., 50% normal changes) typically have an under-developed standard-change framework forcing routine work into the normal-change process.
The CA-level change exception
CA-level changes — operations that affect the certification authority infrastructure itself — are treated separately from certificate-level changes for two reasons:
Blast radius. A CA-level change affects every certificate the CA issues. If the CA is widely used, that is potentially the entire estate. The risk profile is fundamentally different from a single-certificate change.
Audit and compliance significance. CA operations are often subject to specific regulatory or contractual controls (Certificate Practice Statements, audit requirements, key ceremony procedures). The change-management framework for CA operations has to satisfy these external requirements.
CA-level changes typically require explicit approval from the executive owner of the PKI function, the security function, and (where relevant) the compliance function. They are often classified as "major changes" or treated under separate CA-specific change procedures. The exact procedure depends on the regulatory environment.
What good change management for PKI looks like
A working change management approach for PKI has six characteristics:
Standard change templates cover the operational majority. The templates have been defined for the recurring change patterns. The operations team executes against them without per-instance approval, but with the discipline of operating within the template conditions.
Normal changes go through a process that completes within operational timeframes. The CAB or change-review function meets frequently enough that normal changes can be approved within the operational cycle they need to complete in. A weekly CAB is typical for organisations with active certificate operations; less frequent cadences create backlog.
Emergency change procedures are pre-defined. The path for emergency changes is documented before incidents happen. During an incident, the response team knows how to execute an emergency change without negotiating the procedure on the spot.
Aggregation and reporting close the loop. Standard change executions are aggregated and reported. Anomalies are surfaced. The CAB sees the aggregate even when not approving the individual instances. This is also where the PKI logging feed into change management.
Templates are reviewed and refreshed. The templates are revisited periodically. Templates that no longer apply (because the underlying technology has changed) are retired. New templates are added as new operational patterns mature into routine work.
The framework adapts to the operating model maturity. A level-2 organisation may not yet have the standard-change discipline to operate templates effectively; for them, more changes go through the normal process. A level-4 organisation has mature templates and operates most changes as standard. The change management framework reflects the operating model maturity, not a one-size-fits-all standard.
Where PKI change management breaks
Templates that drift from operational reality. The template was approved 18 months ago. The actual operational practice has evolved. Renewals are happening through a slightly different workflow than the template specifies. Technically every renewal is now an undocumented variation. The fix is template review on a defined cadence and the discipline to update them when operational practice changes.
No standard-change framework at all. Every change goes through the normal-change process. The CAB is overwhelmed; routine work is delayed; people work around the system. The fix is investing in the standard-change framework — defining templates, approving them, training the operations team to use them.
Standard changes without aggregation reporting. The standard-change framework exists, the operations team uses it, but no-one is reviewing the aggregate. Drift goes unnoticed. The fix is regular reporting to the CAB even on standard changes, with metrics that surface trends.
Emergency change procedure that requires negotiation during the incident. During the incident, the response team is asking "who needs to approve this?" and "what is the procedure?" The fix is documenting the emergency change procedure and exercising it (tabletop) before it is needed in production.
Trust-store changes treated as configuration management. Trust-store updates are deployed through configuration management without going through the change-management framework. When a trust-store change breaks services, the change-management function has no record. The fix is recognising trust-store changes as PKI changes that go through the framework even when the technical deployment is via configuration management.
Maturity progression for PKI change management
The five-level PKI operational maturity model introduced in the pillar maps onto the change management domain as follows.
Level 1 — Ad-hoc. Certificate changes happen with no consistent classification. Some go through the CAB by default; others happen invisibly because no-one thought to raise them. Emergency changes are improvised. The CAB sees a chaotic mix of trivial renewals and impactful infrastructure changes side by side.
Level 2 — Tooled. Some standard change templates exist, typically for the most common renewal patterns. Other changes default to normal-change handling, which creates a CAB backlog. Emergency procedures exist on paper but have not been exercised. Aggregated reporting on standard changes is partial or absent.
Level 3 — Operationalised. Templates exist for the recurring change patterns. The operations team knows which template applies to which change. The CAB sees aggregated reports. The classification distribution is starting to look like 70–80% standard, 15–25% normal, 1–5% emergency. Templates are reviewed annually, even if the discipline is not yet rigorous.
Level 4 — Integrated. 90%+ of changes route to the standard-change lane via approved templates. Aggregate reporting is monthly with explicit anomaly surfacing. Emergency change procedures are exercised at least annually via tabletop. Templates are refreshed on a defined cadence with clear ownership for keeping them current. The CAB has confidence in the standard-change framework and focuses its attention on the normal-change tail.
Level 5 — Intelligent. Change patterns produce operational intelligence. Anomalies in standard-change execution surface to the CAB before they become problems. New template candidates are identified by analysing the normal-change tail — patterns that are recurring in normal changes are candidates for promotion to standard. The change framework adapts continuously to the evolving operational practice.
Most enterprises sit at level 1 or 2 because the standard-change framework has not been built out for PKI specifically. Progression to level 3 takes a quarter of focused work to define templates, get them approved, and train the operations team. Progression to level 4 requires monthly aggregate-reporting discipline that organisations defer because the value is not visible until template drift causes a problem.
Further reading within this cluster
- Enterprise PKI operating model — the pillar page
- Certificate governance and the steering function
- Certificate discovery in practice
- Certificate issuance workflows
- Certificate renewal operations
- Certificate revocation operations
- Platform onboarding for certificate automation
- Trust-store management
- Operational vs security logging for PKI
- Certificate incident management
