Unified PKI for Enterprise and IoT: The Hybrid Operating Model
Running one PKI platform across enterprise applications and device fleets is a reconciliation problem, not a scaling problem. The five axes where enterprise and IoT PKI diverge, the three architectures that work in production, and the failure modes that don't.
Enterprise PKI and IoT PKI are usually described as the same discipline at different scale. They are not. They are two different operating models that happen to share a cryptographic primitive. Treating them as one problem that grows linearly — more certificates, more devices, same platform — is the fastest way to build a system that fails at the boundary between them.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
This is the pattern we see in assessments across mid-to-large enterprises: a working enterprise CLM handling 50K to 250K certificates for servers, load balancers, and internal services; a separate IoT programme handling device provisioning with bespoke tooling; and a strategic directive to consolidate them. The consolidation rarely produces what executives expect. Either the enterprise platform strains under device-scale volume and lifetime divergence, or the device platform imposes provisioning ceremony on workloads that should be issuing certificates in milliseconds.
The fix is not better tooling. It is recognising that unification is a reconciliation problem across five specific axes — and that architectures exist which reconcile without forcing a single issuance pipeline.
The five reconciliation axes
Every claim that "one PKI can serve enterprise and IoT" has to explain how it handles these five divergences. If a vendor cannot, the platform is either an enterprise CLM with IoT marketing or a device PKI with enterprise marketing.
1. Enrollment protocol
Enterprise endpoints are reachable, have modern TLS stacks, and can hold state. ACME (RFC 8555) assumes all three and is the de facto enterprise standard. The RFC 9773 ACME Renewal Information extension further tightens renewal feedback loops — again, assuming always-on clients.
IoT devices violate every ACME assumption. They may be behind NAT, on cellular links that drop, with 512KB of RAM that cannot hold a full ACME state machine. EST (RFC 7030) fits better: simpler, TLS-client-auth-based, designed for constrained devices. SCEP persists in legacy industrial and networking gear. CMPv2 (RFC 4210) dominates telco and 5G device identity. Matter devices use a protocol specific to the Matter commissioning flow that is neither of the above.
A unified PKI must expose multiple enrollment protocols concurrently, apply policy at the CA layer rather than at the protocol layer, and keep the certificate profiles consistent across whichever protocol issued them. The protocol choice is detailed in PKI enrollment protocols for enterprise and IoT.
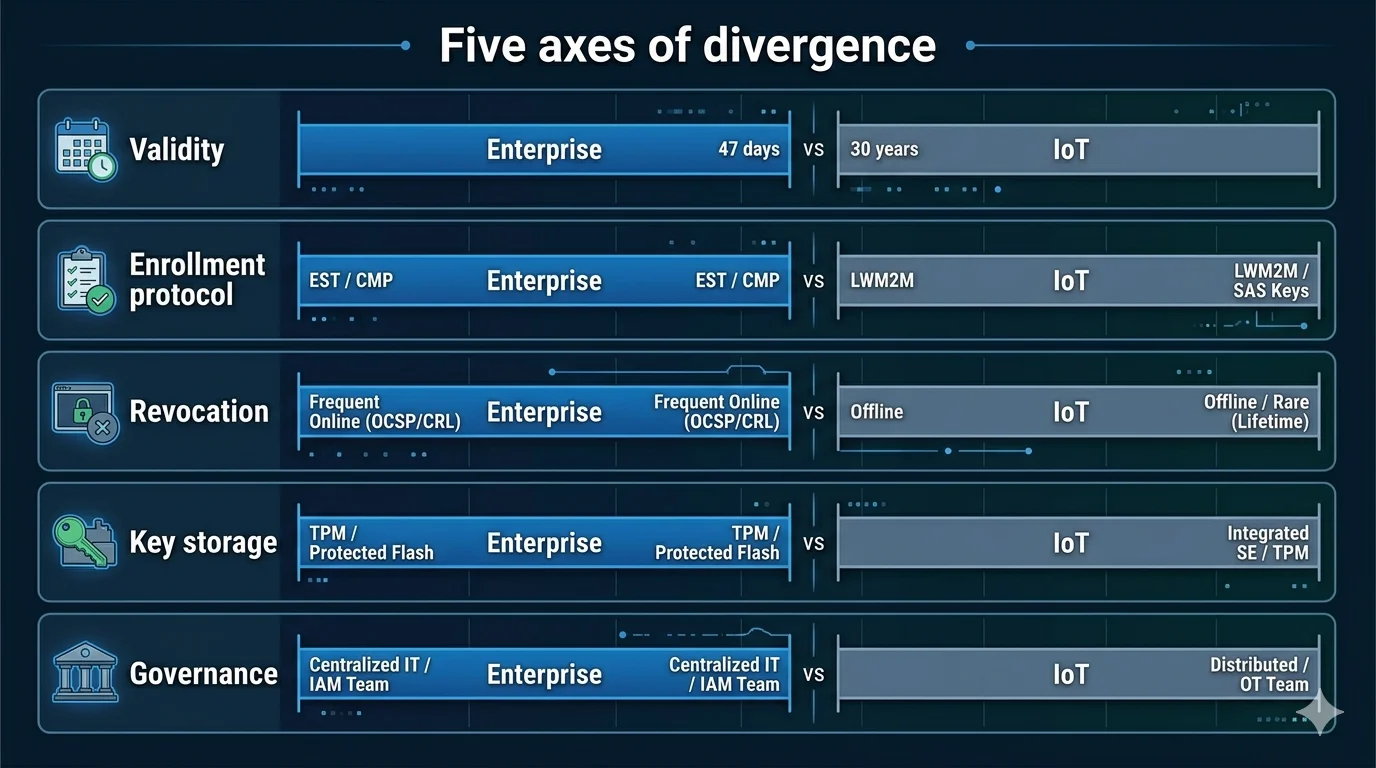
2. Certificate lifetime policy
This is the hardest axis. Enterprise TLS is moving to radically shorter lifetimes under CA/B Forum SC-081v3, which takes public TLS validity from 398 days to 200 days now (took effect in March 2026 as per CA/B Forum SC-081v3), 100 days in March 2027, and 47 days in March 2029. Internal enterprise policy often shortens further: 90-day Let's Encrypt-style rotation is already normal.
IoT cannot follow this trajectory. A Matter Device Attestation Certificate has a validity measured in decades. IEEE 802.1AR draws a distinction between the long-lived IDevID (installed at manufacture, lasts the device lifetime) and the shorter-lived LDevID (issued operationally, rotated more aggressively). An industrial sensor in a sealed enclosure for 15 years cannot be rotated every 90 days; assuming it can is how you discover the sensor is offline for six months a year.
Unified PKI policy must express "this CA issues 47-day TLS certs to web tier, 10-year IDevIDs to factory provisioning, and 1-year LDevIDs to operational device enrollment" as coherent policy rather than three unrelated CAs. See certificate lifetime policy across enterprise and IoT for the framework.
3. Revocation model
Enterprise revocation works because endpoints can fetch OCSP or CRLs, relying parties are online, and the revocation decision propagates in minutes. OCSP stapling (RFC 6066) makes this efficient at enterprise scale.
At device scale, OCSP and CRLs break in predictable ways: CRLs grow to hundreds of megabytes, OCSP responders become single points of failure, and half the device fleet is offline when a revocation is issued. The workable models are short-lived LDevIDs (the credential lifetime is itself the revocation mechanism), gateway-enforced revocation (the gateway checks, the device doesn't), and RFC 9773 ARI-driven renewal pressure where the CA signals clients to renew early before revocation.
Unified PKI must support both models concurrently and must not pretend they are the same. More on this in revocation at device scale.
4. Key storage assumption
Enterprise certificates protect keys in HSMs (network-attached Thales or Entrust, cloud KMS like AWS KMS or Azure Key Vault), or in software with OS-level protection. The assumption is that key extraction requires privileged access to infrastructure you control.
IoT key storage ranges across four distinct classes: software keys in flash (weak, cheap), TPM 2.0 (strong, increasingly common in industrial), discrete secure elements like NXP SE050 or Microchip ATECC608 ($0.50–$5 per unit), and PUF-based identity. The key never leaves the device in the hardware cases — which means the enrollment protocol must handle keys it cannot see, and policy must express "this certificate must be issued to a key attested as resident in a secure element."
A unified PKI that assumes software keys is unsuitable for regulated IoT. One that assumes HSM-backed keys is unsuitable for enterprise workloads that never needed them. See mixed key storage in a unified PKI.
5. Incident response path
When an enterprise certificate is compromised, the response is a Jira ticket, a rotation, a post-incident review. Someone is awake, reachable, and has authority.
When a device certificate is compromised — or when the entire issuing CA is compromised and every device holding a certificate under it is now untrusted — the response is a multi-month physical or OTA intervention across a fleet you may not fully control. The SolarWinds supply-chain compromise and 2018 Intel ME key exposure and subsequent vendor-trust incidents, along with the 2018 Intel ME key exposure, are reminders that device PKI compromise is a different kind of event.
A unified PKI needs an incident response plan that covers both modes. Enterprise rotation is a runbook; device CA compromise is a board-level crisis. Treating them as one incident tier is how teams underprepare for the second.
Three architectures that work in production
AxelSpire's analysis of production deployments identifies three architectures that reconcile the five axes. Each has real trade-offs. None is universally correct.
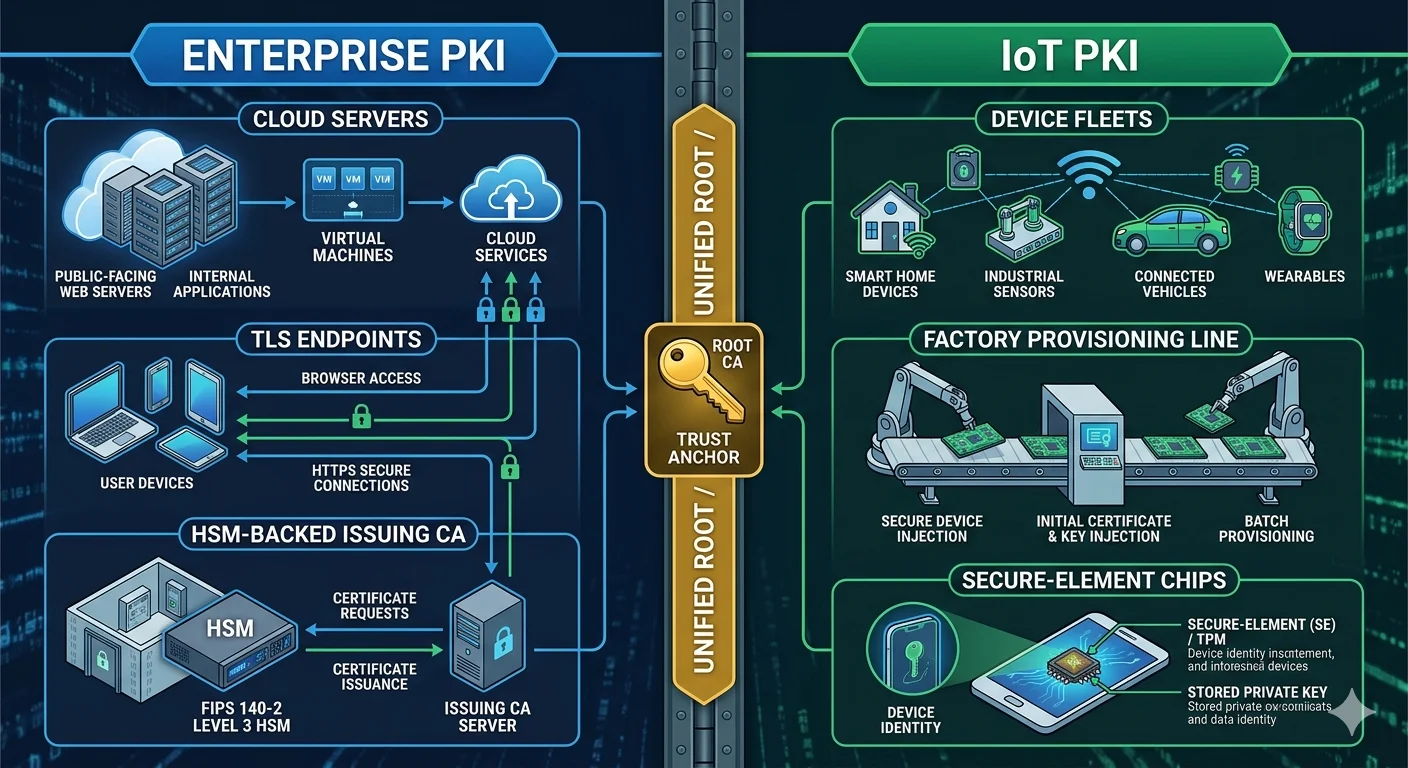
Architecture A: Single CA hierarchy with domain-specific profiles
One root, one issuing CA (or two — one per trust domain), with certificate profiles distinguishing enterprise from device issuance. The CA software understands both ACME and EST. Policy is expressed as profiles: enterprise-tls-47d, device-ldevid-1y, device-idevid-20y. One audit trail, one HSM, one operations team.
Works for: organisations with under 100K devices, homogeneous device fleets, and a PKI team with both enterprise and device experience. Comcast's xPKI architecture is a published example of this pattern — a single PKI stack issuing both Sectigo-backed enterprise certificates via xCM and libCertifier-based device certificates, with profile-based differentiation.
Breaks at: mass device scale, Matter-specific requirements (which need CSA-recognised PAAs), and any deployment where the device team and enterprise team cannot agree on shared operational procedures.
Architecture B: Federated CAs with a shared control plane
Separate CAs for enterprise and device issuance — often separate vendors, separate HSMs, separate audit trails — with a unified control plane providing policy, inventory, and orchestration across both. SPIFFE trust domain federation is one pattern for this at the workload/device edge; enterprise CLM platforms provide the enterprise side.
Works for: organisations where the device and enterprise programmes have different vendors, compliance regimes, or operational cadences but need shared visibility and policy. This is increasingly the default for organisations running Matter plus enterprise TLS — the Matter CAs are necessarily separate, federation is the only option.
Breaks at: poor control plane abstraction (if the control plane just forwards to each CA without normalising policy, it adds latency without adding value), and at inventory coherence (two CAs with different identifier schemes means the "unified" inventory is two tabs in a dashboard).
Architecture C: Split CAs with unified CLM
Enterprise CLM (Keyfactor Command, Venafi TPP, AppViewX AVX ONE, DigiCert ONE) handles enterprise certificate discovery, automation, and governance. A specialist IoT platform (Device Authority KeyScaler, Intrinsic ID, a Matter-specific provider) handles device provisioning. The CLM extends discovery into the device estate but does not issue device certificates.
Works for: organisations that want enterprise-grade governance over their certificate estate without forcing devices through enterprise enrollment pipelines. Keeps specialist device vendors responsible for device-specific problems.
Breaks at: shadow boundary — which system owns the certificate inventory, who owns the renewal decision, who gets paged when a device certificate fails. Without explicit RACI between CLM and IoT platform, this architecture produces the worst of both worlds.
More on this decision in platform consolidation vs best-of-breed.
Failure modes we see in practice
Four patterns recur across assessments. Name them so they don't become the default.
Enterprise PKI bolted onto IoT. The enterprise team extends its ACME-based CLM to devices "because it's the same protocol." The devices cannot run ACME reliably, provisioning fails in the factory, renewal fails in the field, and the team concludes that IoT PKI is harder than enterprise PKI. It is — for reasons that are not protocol choice.
IoT PKI bolted onto enterprise. The device team's provisioning CA starts being used for internal TLS "because we already have it." The device CA has lifetimes measured in years, cryptographic policy optimised for constrained devices (often ECDSA P-256, sometimes still RSA-2048), and no integration with enterprise change management. Two years later, enterprise TLS is running on 10-year certificates with no rotation story.
Two platforms, no coordination. Enterprise CLM and IoT PKI coexist, each running well in isolation. Neither knows what the other owns. A certificate issued by the IoT CA appears on an enterprise load balancer; a certificate issued by the enterprise CA ends up on a device. Inventory, audit, and incident response all break at the seam.
Matter as the forcing function. The device programme adopts Matter, which requires CSA-recognised Product Attestation Authorities and Product Attestation Intermediates. The organisation's existing IoT PKI is not CSA-recognised. Now there are three PKIs — enterprise, existing IoT, Matter — and no plan. More on the Matter-specific constraints in Matter PKI.
Platform evaluation criteria
When evaluating a PKI platform for unified enterprise-plus-IoT use, the questions that actually matter:
- Does it expose ACME, EST, SCEP, and CMPv2 concurrently, with consistent policy across all four? If it exposes only ACME, it is an enterprise platform. If it exposes only EST or SCEP, it is a device platform.
- Can it express lifetime and algorithm policy per profile rather than per CA? If you need a new CA for every lifetime class, the platform does not scale to the mixed estate.
- Does it support hardware key attestation — TPM, secure element, HSM — as a policy input? If the policy language is "issue if CSR is valid," the platform cannot enforce that a device certificate must be issued to a key in a secure element.
- What is the revocation model at device scale? If the answer is "CRL and OCSP," the platform is not designed for devices. If the answer is "short-lived certificates and ARI," the platform is not designed for long-lived device identity. The answer should be "both, configurable per profile."
- Can the control plane issue certificates across multiple CAs — including CAs run by other vendors, cloud-managed CAs, and specialist device PKIs — with policy applied centrally? This is the crypto-agility test. A platform that cannot do this will be the platform you replace in five years when the CA landscape shifts again.
- What is the audit trail across enterprise and device issuance? One system of record, one query, one export. Two disconnected audit trails fail compliance reviews.
Where 3AM fits
AxelSpire built 3AM as a protocol-abstracting control plane specifically for this problem. It sits above multiple CAs — enterprise, cloud-managed, device-specific, Matter — and applies consistent policy across ACME, EST, SCEP, and CMPv2 while preserving the separate issuance pipelines each domain requires. It does not force consolidation where consolidation breaks. It does not leave the organisation with two disconnected inventories. The pattern it implements is closest to Architecture B — federated CAs, shared control plane — because in our experience that is the architecture that survives contact with real deployments.
For evaluation, Ask Axel can walk through the five reconciliation axes against your current setup. For a structured assessment, contact AxelSpire.
Further reading within this cluster
- PKI enrollment protocols for enterprise and IoT: ACME vs EST vs SCEP vs CMPv2
- Certificate lifetime policy across enterprise and IoT
- Revocation at device scale: why CRL and OCSP fail
- Factory provisioning vs runtime enrollment
- Mixed key storage in unified PKI: HSM, TPM, secure element, software
- Governance across enterprise and device PKI
- Platform consolidation vs best-of-breed: when one platform wins
