Wildcard Certificates: Security Risks, Scope Creep & Alternatives
Wildcard certificates trade operational convenience for shared private keys, implicit future scope, and fleet-wide revocation. This page explains how wildcards behave in X.509, where the security risks show up in real environments, when narrow use is still reasonable, and how SAN or per-service certificates plus short lifetimes and ACME automation usually beat wildcard sprawl.
Wildcard Certificates: Security Risks, Scope Creep, and Alternatives
Section titled “Wildcard Certificates: Security Risks, Scope Creep, and Alternatives”TL;DR: Wildcards share one private key across many names and pre-authorise future subdomains, so compromise or revocation hits the whole surface; automation and explicit SAN or per-service certificates isolate blast radius while keeping renewals cheap.
Overview
Section titled “Overview”For executives: A single wildcard often backs payment flows, internal tools, and customer-facing sites with one key copied many places. Incidents that would have stayed local to one hostname can become domain-wide impersonation—and explaining that in a post-mortem is painful.
For security leaders: Wildcards work against least privilege: trust expands every time DNS adds a label under the wildcard, often without a certificate review. Pair that with Certificate Transparency visibility and audit questions about segmentation (PCI DSS, SOC 2), and wildcards deserve explicit risk acceptance, not default issuance. Every unmanaged wildcard is an unpriced security risk on the certificate inventory.
For engineers: *.example.com does not cover the apex or nested names such as internal.api.example.com; teams sometimes “fix” that with extra wildcards or huge SAN lists, which worsens key sprawl. Modern ACME automation removes most of the historical pain of per-host or SAN certificates, so the old “wildcard to avoid toil” shortcut is often a net loss.
Operational context: Wildcards persist because manual issuance made one cert for many hosts attractive. With automated lifecycle management, distributing distinct keys per service or an explicit SAN list is usually less work than synchronising one hot private key across heterogeneous environments—and far easier to justify after any single-host compromise.
Problem Statement
Section titled “Problem Statement”- Shared private key: Every listener using the wildcard shares the same key material; security equals the weakest place that key lives (staging, forgotten VMs, contractor laptops).
- Implicit future scope: New subdomains are covered automatically—no issuance review—so shadow IT or takeover-prone DNS can inherit valid public trust under the same cert.
- Revocation and rotation are fleet events: One compromise or policy-driven replacement can force simultaneous re-provision across many services; without automation, that is a coordinated outage.
- Coverage confusion:
*.example.comomitsexample.comand multi-level names unless you add SANs or more wildcards—workarounds compound scope and key-sharing problems. - CT and reconnaissance: A logged wildcard signals “interesting tree, one key” to attackers; individual certs still appear in CT but expose specific names and separate keys.
- Compliance friction: Auditors increasingly expect segmented certificate management; one wildcard spanning card data, internal admin, and marketing invites hard questions.
Each of these is a distinct wildcard certificate vulnerability, and they compound. The shared-key problem is bad on its own; combined with implicit scope expansion and fleet-wide revocation, wildcards create a class of security risk that grows silently over time.
Failure scenario: A staging host with a copy of *.example.com is compromised. The attacker uses the stolen key to terminate TLS for api.example.com or admin.example.com without touching production’s “hardened” path. Alternatively, a required wildcard revocation forces dozens of microservices offline until every deployment is updated—hours of customer impact if renewal and rollout are not automated.
The Convenience Trap
Section titled “The Convenience Trap”Wildcard TLS/SSL certificates solve a real problem. You have dozens of subdomains, certificates are expiring on different schedules, and provisioning individual certs feels like busywork. A single *.example.com certificate covers everything. Done.
Except you have made a security trade-off that many teams never revisit—and the blast radius grows every time someone spins up a new subdomain.
How Wildcard Certificates Actually Work
Section titled “How Wildcard Certificates Actually Work”A wildcard certificate covers all single-level subdomains of a given domain. *.example.com protects api.example.com, staging.example.com, and admin.example.com—but not example.com itself (you need a SAN entry for the bare domain) and not multi-level subdomains like internal.api.example.com.
This is where the first misunderstanding starts. Teams assume wildcards cover everything. They do not. The workarounds people use—issuing wildcards at multiple levels, or combining wildcards with broad SAN lists—compound the security problems.
For how names appear on certificates and how SANs relate to the subject, see Certificate anatomy and the X.509 standard overview.
Wildcard Certificate Security Risks
Section titled “Wildcard Certificate Security Risks”1. Private key blast radius
Section titled “1. Private key blast radius”Every service using a wildcard certificate shares the same private key. If that key is compromised on any server—your staging environment, a forgotten dev box, a contractor’s test instance—the attacker can impersonate every subdomain the wildcard covers.
This is not theoretical. In practice, wildcard certificates end up deployed to environments with very different security postures. The production API server might have hardened key storage. The internal tool someone stood up last quarter probably does not.
The vulnerability is structural: the security of your wildcard is equal to the security of the weakest deployment that holds the private key.
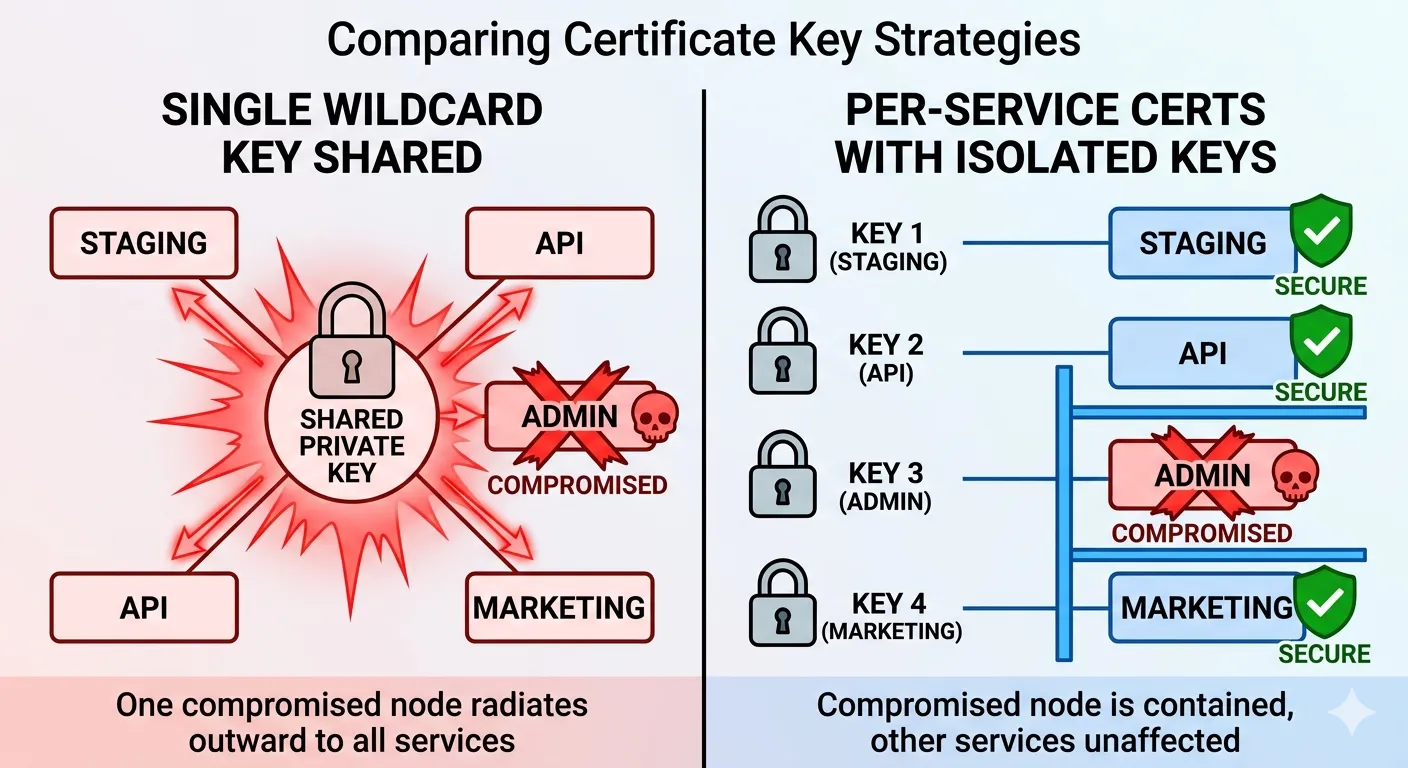 A single wildcard key compromise radiates across every subdomain (left). Per-service certificates isolate the blast radius to one service (right).
A single wildcard key compromise radiates across every subdomain (left). Per-service certificates isolate the blast radius to one service (right).
See Private key protection and Key management best practices for control patterns that apply whether you use wildcards or not.
2. Scope creep is the default behaviour
Section titled “2. Scope creep is the default behaviour”Wildcard certificates do not just cover the subdomains you have today. They cover every subdomain you will create in the future. That means your certificate’s scope expands without review, approval, or even awareness from the security team.
New microservice? Covered. Shadow IT subdomain? Covered. Subdomain takeover target? Also covered—and now an attacker who claims that DNS record gets a valid TLS certificate for free, because the wildcard already trusts it.
This is the opposite of least privilege. You are pre-authorising trust for infrastructure that does not exist yet.
3. Revocation becomes a blast event
Section titled “3. Revocation becomes a blast event”When you need to revoke a wildcard certificate—because a key was exposed, a server was compromised, or an employee with access leaves—you are revoking trust for every service that depends on it simultaneously.
In a microservices environment, this can mean dozens of services losing their TLS certificates at once. Even with automation, re-provisioning and redeploying across that many services takes time. If you do not have automation, you are looking at a coordinated outage.
Operational detail: plan for Certificate revocation (CRL & OCSP) and lifecycle runbooks in Certificate lifecycle management.
4. Certificate Transparency exposure
Section titled “4. Certificate Transparency exposure”Every publicly trusted certificate is logged in Certificate Transparency (CT) logs. A wildcard certificate in CT logs tells attackers: “There are interesting subdomains under this domain, and they all share a key.” It is an invitation to enumerate.
Individual certificates also appear in CT logs, but they reveal specific subdomains one at a time—and each can use its own isolated key.
5. Compliance friction
Section titled “5. Compliance friction”PCI DSS, SOC 2, and other frameworks increasingly expect segmented certificate management. Auditors ask questions when they see a single wildcard covering payment processing, internal tooling, and marketing sites. The conversation about why your card processing subdomain shares a private key with your blog is never a comfortable one.
Compliance and audit and Threat models and attack vectors help frame reviews and evidence.
When Wildcards Are Defensible
Section titled “When Wildcards Are Defensible”Wildcards are not always wrong. They make sense in narrow, well-controlled scenarios:
Homogeneous environments with consistent security postures. If every subdomain runs on identically configured infrastructure with the same key protection, the shared-key risk is contained. Think: a CDN edge fleet where every node is identical.
Truly ephemeral environments. Short-lived development or CI/CD environments where certificates exist for minutes or hours, not months. The exposure window is small enough that the convenience trade-off is reasonable.
Internal-only, private CA deployments. When you control the entire trust chain and the certificate never touches the public internet, the CT exposure and public trust concerns disappear. You still have the shared key problem, but you can mitigate it with short lifetimes and automated rotation.
Private PKI patterns: CA architecture and Certificate issuance workflows.
The Alternatives
Section titled “The Alternatives”SAN certificates (Subject Alternative Names)
Section titled “SAN certificates (Subject Alternative Names)”SAN certificates list each covered domain explicitly. You get multi-domain coverage without the implicit “cover everything” behaviour of wildcards. Each renewal is an opportunity to review scope. Each certificate documents exactly what it protects.
The operational cost used to be significant—maintaining SAN lists manually is tedious. With ACME automation, the cost difference between a wildcard and a SAN certificate is negligible. Your automation already knows which subdomains exist. Let it request exactly what is needed.
DNS-based validation is common for wildcards and multi-name certs: DNS-01 challenge validation. Implementation context: ACME protocol implementation.
Per-service certificates
Section titled “Per-service certificates”The cleanest approach: every service gets its own certificate with its own private key. A compromise affects exactly one service. Revocation affects exactly one service. Scope is explicit by definition.
This was impractical when certificate provisioning was a manual process. With automated certificate lifecycle management, per-service certificates are often less operational work than managing wildcard distribution and key synchronisation across services.
Short-lived certificates
Section titled “Short-lived certificates”Regardless of whether you use wildcards, SANs, or per-service certificates, shorter lifetimes reduce the window of exposure from any compromise. A 90-day certificate is better than a one-year certificate. A 24-hour certificate is better still.
Short lifetimes also force you to build the automation that makes wildcards unnecessary in the first place.
Industry direction: 47-day TLS certificates, Certificate automation readiness, and Renewal automation.
Why Wildcards Require DNS-01 Validation
Section titled “Why Wildcards Require DNS-01 Validation”One operational reality teams overlook: wildcard certificates cannot be validated using HTTP-01 or TLS-ALPN-01 ACME challenges. The ACME protocol (RFC 8555) mandates DNS-01 as the only challenge type for wildcard names. This is not a CA-specific quirk — it is a protocol-level requirement.
The reason is structural. HTTP-01 and TLS-ALPN-01 prove control of a specific host by responding on port 80 or 443 of that host’s IP. A wildcard covers names that may not resolve to any host yet — there is no IP to answer the challenge. DNS-01 proves domain-level control by placing a TXT record at _acme-challenge.<domain>, which works regardless of whether individual subdomains have running servers.
Persistent DNS-01 delegation
Section titled “Persistent DNS-01 delegation”In practice, the main pain point with DNS-01 is that it requires write access to your authoritative DNS zone — and most teams do not want their ACME client holding production DNS credentials. The standard mitigation is persistent CNAME delegation: you create a static CNAME record that redirects the challenge to a zone your automation controls.
For example:
_acme-challenge.example.com. CNAME _acme-challenge.acme-delegate.example.com.The ACME client writes the validation token to the delegate zone only. Your production DNS zone never changes after the initial CNAME is set. This is sometimes called “DNS-01 persist” or permanent delegation — the CNAME is created once and left in place across all future renewals.
This pattern is critical for wildcard automation at scale. Without it, every renewal cycle requires production DNS writes, which introduces both a privilege escalation vector and a fragile dependency on DNS API availability during the renewal window.
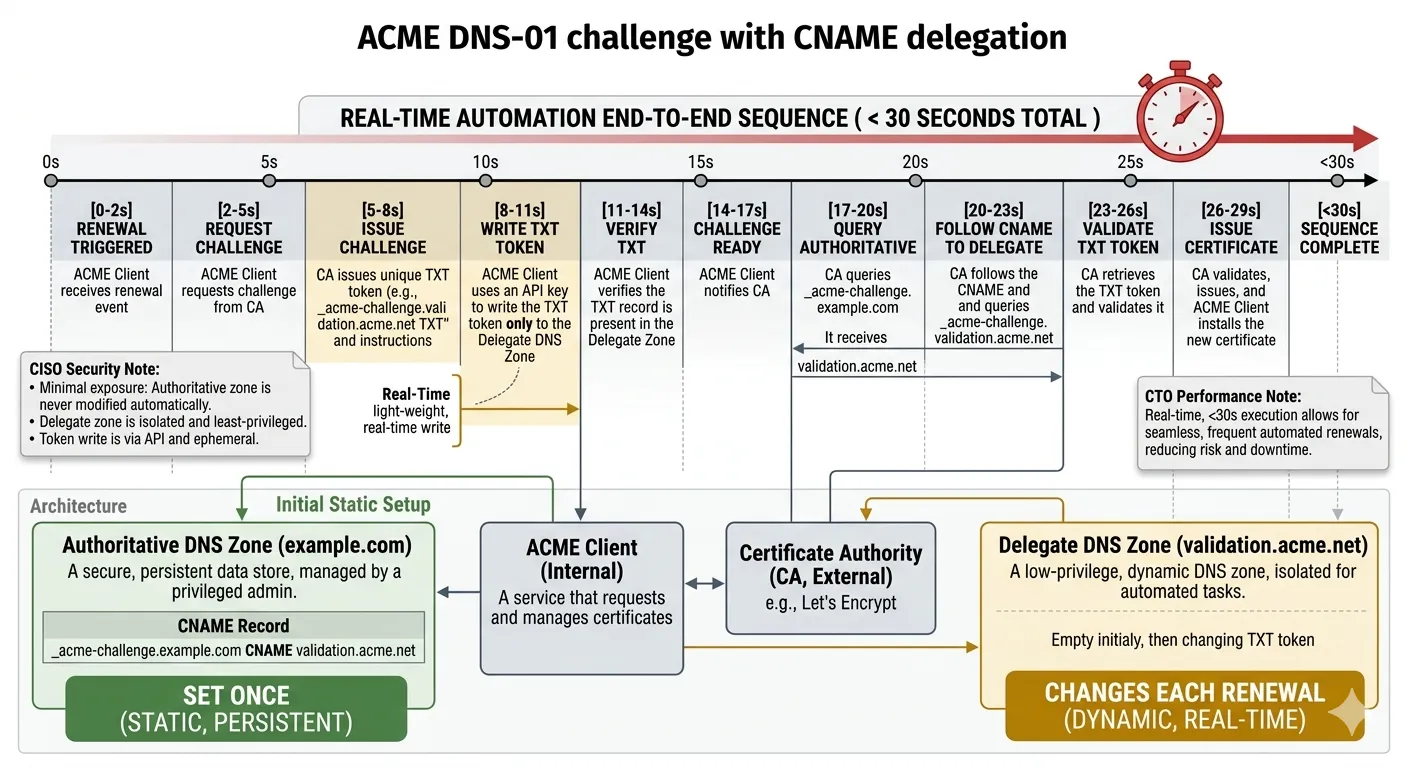 Persistent CNAME delegation for DNS-01 wildcard validation. The static CNAME (set once) redirects challenges to a delegate zone where the ACME client writes ephemeral TXT tokens — production DNS is never modified during renewal.
Persistent CNAME delegation for DNS-01 wildcard validation. The static CNAME (set once) redirects challenges to a delegate zone where the ACME client writes ephemeral TXT tokens — production DNS is never modified during renewal.
Operational implications for wildcard issuance
Section titled “Operational implications for wildcard issuance”The DNS-01 requirement means wildcard certificate automation is inherently more complex than per-host automation:
- DNS API credentials must be available to the ACME client, scoped as tightly as possible — ideally to the delegate zone only.
- Propagation delays affect validation. Unlike HTTP-01, which completes in seconds, DNS-01 depends on TTLs and resolver caching. Automation must handle polling or back-off.
- Multi-provider environments complicate delegation when subdomains are split across DNS providers (e.g., Cloudflare for the CDN edge, Route 53 for internal services).
With per-service or SAN certificates, you can use HTTP-01 validation — no DNS write access required, no propagation delays, no delegation plumbing. This is one of the under-appreciated reasons why migrating away from wildcards simplifies your automation, not just your security posture.
For a full walkthrough of DNS-01 challenge mechanics, delegation patterns, and provider-specific configuration, see DNS-01 challenge validation.
The Migration Path
Section titled “The Migration Path”If you are currently relying on wildcards, the migration path is not “replace everything overnight.” It is incremental:
- Inventory your wildcard deployments. Identify every server and service that holds a copy of each wildcard certificate’s private key. This step alone usually reveals surprises—forgotten deployments, unexpected scope, key copies in places they should not be. Use Inventory and discovery practices.
- Classify by risk. Separate the subdomains into tiers based on what they handle. Payment processing, authentication, and customer data services move first. Internal tools and static content can wait.
- Automate before you migrate. Do not replace wildcards with manually managed individual certificates. That trades one problem for a worse one. Get ACME-based automation in place first, then migrate services onto individually issued certificates.
- Keep wildcards only where defensible. After migration, you may still have legitimate wildcard use cases—the CDN fleet, the ephemeral CI environments. That is fine. The goal is not zero wildcards. It is zero unexamined wildcards.
Broader rotation patterns: Certificate rotation strategies.
The Operational Reality
Section titled “The Operational Reality”The reason wildcards persist is not that teams have evaluated the trade-offs and decided they are acceptable. It is that provisioning individual certificates used to be painful enough that wildcards were the path of least resistance.
That calculus has changed. Automated certificate management makes per-service certificates operationally cheaper than wildcard distribution. The security benefits of isolation come for free once your provisioning pipeline handles it.
The question is not whether you can afford to replace your wildcards. It is whether you can afford to explain, in your next incident review, why a staging server compromise gave an attacker valid TLS for your production API.
Checklist
Section titled “Checklist”- Inventory: Every host, load balancer, and secret store that holds the wildcard private key is documented and owned.
- Risk tiering: High-risk workloads (auth, payments, PII) are not sharing a wildcard key with low-trust or experimental environments.
- Automation: Issuance and renewal are automated before you depend on per-service or tight SAN certs at scale.
- DNS-01 delegation: If wildcards remain, persistent CNAME delegation is in place so renewal does not require production DNS writes.
- Revocation runbook: You can answer who rotates what, in what order, and within what SLA if the wildcard must be revoked.
- DNS and names: Apex and nested names are explicitly covered (SAN or separate certs)—no accidental gaps or wildcard stacks “just to make it work.”
- Exceptions: Remaining wildcards have written rationale (homogeneous fleet, ephemeral CI, private CA) and review dates.
Related Documentation
Section titled “Related Documentation”- Private key protection — where keys must live and how to protect them
- Key management best practices — ownership, rotation, and segregation patterns
- Certificate lifecycle management — issuance through revocation as an operational program
- DNS-01 challenge validation — DNS-01 mechanics, persistent delegation, and provider configuration for wildcard and multi-name certs
- Certificate automation readiness — prerequisites before shortening lifetimes or splitting certs
- Inventory and discovery — finding wildcard key copies and dependents
- 47-day TLS certificates — why short-lived certs assume automation
- Certificate anatomy — SANs, subjects, and what a cert actually binds
Wildcard overuse is one of the most common patterns we see in certificate management assessments. If your organisation is running wildcards across mixed-trust environments, talk to us about a certificate landscape review.
