PKI Assessment Guidelines 2026: Run an Internal PKIMM Maturity Assessment in 2–4 Weeks
A PKI maturity assessment tells you exactly where your certificate infrastructure stands, where the operational risk is concentrated, and what to fix first. This page gives you a complete methodology — built on the PKI Consortium's PKI Maturity Model (PKIMM) and refined through AxelSpire's implementation work across enterprise environments — that an internal team can execute in 1–2 agile sprints without external consultants.
AxelSpire's position: Most PKI assessments we see fall into one of two failure modes: a 200-page compliance document that nobody reads, or a vendor evaluation disguised as an audit. Neither produces a usable action plan. The methodology below is designed to produce one.
Related: PKI Readiness Self-Assessment (60-second interactive quiz) · PKI Implementation Guide · PQC Readiness Assessment · Private CA Comparison
Why PKI Assessment Is a 2026 Priority
Three regulatory and technical forces have converged to make PKI maturity a board-level issue:
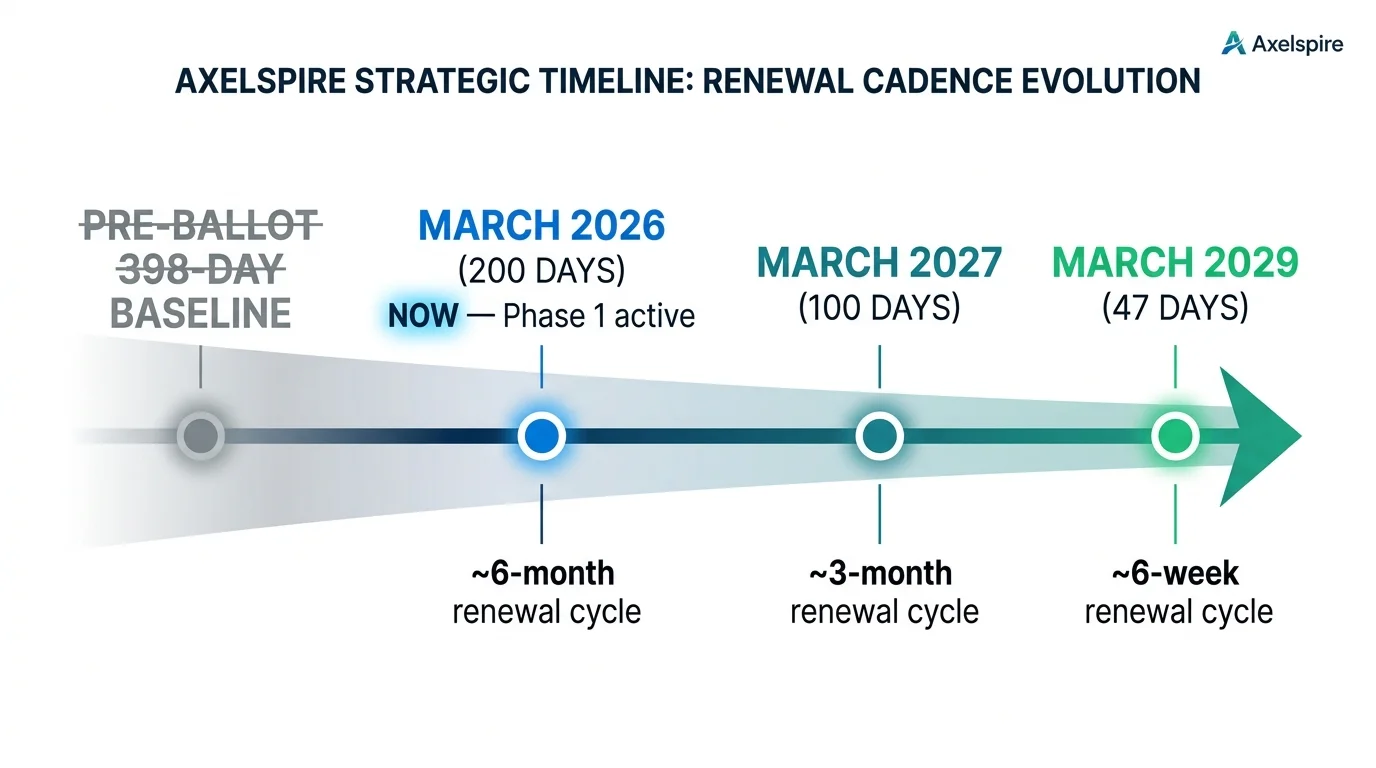
SC-081v3 is already in effect. The CA/Browser Forum's ballot passed unanimously in April 2025 and the first phase took effect on March 15, 2026 — maximum public TLS certificate lifetime dropped from 398 days to 200 days. The next phase (100 days) hits in March 2027, with 47-day certificates mandatory by March 2029. Organisations without automated certificate lifecycle management will face recurring outages on a compressed timeline. See AxelSpire's full analysis: TLS Certificate Impact Analysis.
Post-quantum migration timelines are hardening. NSM-10, OMB M-23-02, and EO 14144 have set federal PQC migration deadlines, and supply-chain pressure is pushing these timelines into private-sector procurement requirements. A PKI assessment is the first step in any credible PQC readiness plan.
Certificate sprawl is accelerating. Zero-trust architectures, service mesh mTLS, IoT device identity, and short-lived workload certificates have multiplied the number of certificates organisations manage by an order of magnitude — often without corresponding visibility. AxelSpire's assessment work consistently finds that actual certificate counts are significantly higher than what appears in the CMDB. See Certificate Sprawl & Visibility.
The Industry Standard: PKI Consortium PKIMM
The PKI Maturity Model (PKIMM) is the only vendor-neutral, globally recognised PKI assessment framework released in the last five years. Published by the PKI Consortium (2023–2026), it replaces earlier ad-hoc approaches with a structured, CMMI-inspired model.
5 Maturity Levels
| Level | Name | What It Looks Like |
|---|---|---|
| 1 | Initial | Reactive, no visibility. Outages discovered after services fail. |
| 2 | Basic | Ad-hoc processes, spreadsheet tracking, one person "owns" PKI informally. |
| 3 | Advanced | Documented standards, centralised discovery, defined roles and RACI. |
| 4 | Managed | Automated lifecycle, proactive monitoring, metrics, compliance integration. |
| 5 | Optimised | Strategic enabler. Crypto-agile, PQC-ready, continuous improvement. |
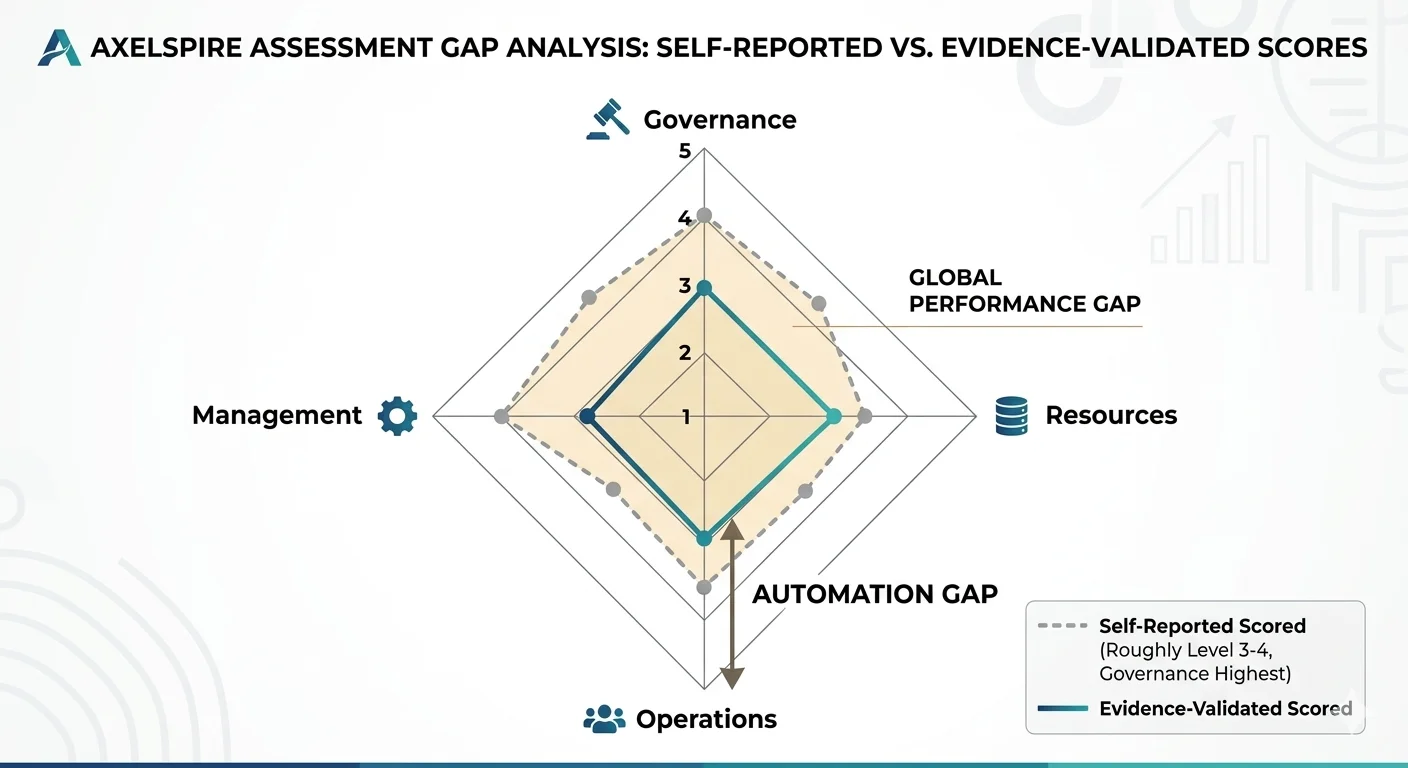
AxelSpire's observation: most enterprise organisations self-assess at Level 3 but score at Level 2 when evidence is required. The gap is almost always in Operations (automation and monitoring) and Resources (training and institutional knowledge).
Structure: 4 Modules, 15 Categories
| Module | Categories |
|---|---|
| Governance | Strategy & vision · Policies & documentation · Compliance · Processes & procedures |
| Management | Key management · Certificate management · Infrastructure management · Change management & agility |
| Operations | Resilience · Automation · Interoperability · Monitoring & auditing |
| Resources | Sourcing · Knowledge & training · Awareness |
The PKIMM's structure is sound, but AxelSpire's implementation experience has identified two areas where it underweights risk:
- Automation readiness is buried inside Operations rather than being a cross-cutting theme. In a 200-day (and soon 47-day) certificate world, automation capability is the single largest determinant of operational risk. It should be weighted accordingly.
- The model doesn't explicitly assess crypto-agility — the ability to rotate algorithms, CAs, or certificate profiles without re-architecting. This is critical for PQC migration and CA distrust scenarios. See Crypto-Agility & PQC Migration.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
AxelSpire's 2-Sprint Assessment Methodology
Designed for internal security and architecture teams. No external consultants required. Total elapsed time: 2–4 weeks.
Sprint 0 — Preparation (1–2 days)
- Appoint a PKI Assessment Owner. Choose someone outside day-to-day PKI operations for objectivity. In AxelSpire's experience, the best results come from a security architect or compliance lead — not the person who runs the CA.
- Define scope. Which PKI instances and use cases? Internal CA, public TLS, IoT device identity, DevOps/CI pipeline certificates, mTLS for service mesh, code signing. Scoping too broadly in Sprint 1 is the most common cause of assessment overrun.
- Assemble stakeholders. Security, Infrastructure, Compliance, DevOps, Legal. One representative per domain is sufficient.
- Obtain the assessment tool. Use the official PKIC Excel Assessment Tool (free) or the simplified scorecard below.
Sprint 1 — Assessment & Evidence Collection (5–7 days)
Day 1–2: Certificate Discovery
Run a certificate inventory scan. Sources: internal scanner or ACME-compatible discovery tool, CMDB export, CT log search (crt.sh) for public certificates, TLS connection logs, load balancer and CDN certificate stores.
Document: total certificate count by type (public TLS, private/internal, client auth, code signing, IoT), issuing CA, expiry distribution, key algorithm distribution (RSA-2048, RSA-4096, ECDSA P-256, any PQC/hybrid).
Day 3–5: Stakeholder Workshops
Run one 45–60 minute structured session per PKIMM module (Governance, Management, Operations, Resources). Score each of the 15 categories on the 1–5 scale. Collect evidence for each score: policy documents, runbooks, monitoring dashboards, RACI matrices, incident post-mortems, automation coverage percentages.
Day 5–7: Score Reconciliation
Reconcile scores across stakeholders. Where self-assessments diverge by more than 1 level, the lower score is almost always more accurate — use it as the baseline.
Sprint 2 — Analysis & Roadmap (5–7 days)
- Calculate module and overall scores. Average per module, then weighted overall. AxelSpire recommends weighting: Governance 25%, Management 20%, Operations 35%, Resources 20%. The Operations overweight reflects the SC-081v3 reality — automation capability is now the primary risk driver.
- Identify top 3–5 gaps ranked by business risk (outage probability × blast radius × compliance exposure).
- Build a prioritised 90-day action plan. Separate quick wins (achievable in <2 weeks, typically monitoring and alerting) from strategic projects (automation rollout, CA consolidation, PQC readiness). See AxelSpire's certificate automation readiness guide for the automation workstream.
- Present findings to leadership. One-page executive summary + detailed gap register + 90-day roadmap.
PKI Assessment Scorecard
Rate each of the 15 PKIMM categories from 1 (Initial) to 5 (Optimised). Collect evidence for every score above 2.
Governance Module
| Category | Score (1–5) | Evidence / Notes |
|---|---|---|
| Strategy & vision | Is there a documented PKI strategy aligned to business objectives? | |
| Policies & documentation | CP/CPS current? Policy review cycle defined? | |
| Compliance | Mapped to regulatory requirements (SOC 2, PCI-DSS, FedRAMP, HIPAA)? | |
| Processes & procedures | Documented operational procedures for issuance, renewal, revocation? |
Management Module
| Category | Score (1–5) | Evidence / Notes |
|---|---|---|
| Key management | HSM usage? Key rotation schedule? Backup and recovery tested? | |
| Certificate management | Full lifecycle tracked? Renewal process defined? | |
| Infrastructure management | CA infrastructure documented? DR/failover tested? | |
| Change management & agility | Can you rotate CAs or algorithms without re-architecting? (Crypto-agility) |
Operations Module
| Category | Score (1–5) | Evidence / Notes |
|---|---|---|
| Resilience | CA failover tested? Certificate-dependent services identified? | |
| Automation | What percentage of certificates are issued/renewed via ACME or API? | |
| Interoperability | Can certificates be consumed across platforms, clouds, and protocols? | |
| Monitoring & auditing | Real-time expiry alerts? Audit logs centralised? CT log monitoring? |
Resources Module
| Category | Score (1–5) | Evidence / Notes |
|---|---|---|
| Sourcing | PKI budget defined? Vendor contracts current? | |
| Knowledge & training | More than one person understands the CA infrastructure? | |
| Awareness | Do application teams know how to request and deploy certificates? |
Scoring guidance: The official PKIC tool provides detailed scoring rubrics per category. The tables above are sufficient for a first-pass assessment; use the full tool for deeper analysis.
Common Gaps Found in 2024–2026 Assessments
Based on AxelSpire's assessment work and cross-referenced with the Ponemon 2024 Global PKI & IoT Trends Study:
1. No clear PKI owner. Still the most common structural failure. PKI responsibility is split across infrastructure, security, and DevOps with no single accountable owner and no RACI matrix. This is the root cause of most assessment scores below Level 3.
2. Automation coverage below 30%. Organisations report "we use ACME" but actual coverage — the percentage of certificates issued and renewed without human intervention — is typically under 30%. With 200-day certificate lifetimes already in effect and 47-day approaching, anything below 80% automation coverage represents material outage risk. AxelSpire's 3AM platform addresses this by providing a single automation and policy control plane across multiple CAs.
3. Unknown certificate inventory. Discovery scans consistently reveal certificates that don't appear in any tracking system — orphaned certs on legacy load balancers, developer-provisioned certs in CI pipelines, IoT device certificates issued by OEM CAs. The certificate sprawl problem compounds with every new microservice and cloud account.
4. No PQC migration plan. Most organisations score Level 1 on crypto-agility. They have no inventory of cryptographic algorithms in use, no assessment of PQC-sensitive data flows, and no timeline for hybrid certificate testing. This is understandable — PQC is emerging — but the assessment should surface it as a tracked gap. See AxelSpire's PQC readiness assessment framework.
5. Key management gaps. Private CA keys stored in software rather than HSMs or cloud KMS. No documented key rotation procedures. Backup and recovery untested. This is the gap with the highest severity and lowest visibility — it doesn't cause outages until it causes a catastrophic one. See HSM Deployment Strategy.
