Certificate Management ROI: Cost Savings & Outage Prevention Calculator
 Certificate Lifecycle is not alchemy
Certificate Lifecycle is not alchemy
SSL Certificate Lifecycle Management: A Modern Approach for Enterprise Environments
Certificate management has long been synonymous with obscure PKI specialisms — skills with little value outside very niche use cases. That needs to change. As automation matures and certificate validity windows shrink, the question isn’t whether to automate SSL/TLS certificate lifecycle management, it’s how to do it in a way that engineers and administrators can own, without depending on PKI specialists who are increasingly hard to find.
This post covers how we approach certificate lifecycle management for enterprises — the architecture decisions that matter, what centralised management actually delivers operationally, and where most implementations fall short.
Why Traditional PKI Designs Don’t Scale
As an organisation’s digital presence grows, so does its certificate inventory. What was manageable with spreadsheets and calendar reminders at 50 certificates becomes a serious operational liability at 500. Traditional PKI designs compound the problem: they require dedicated software installations, ongoing maintenance, and specialist knowledge to operate. The consequences of under-investment are predictable — unplanned outages from expired certificates, security risks from outdated trust stores, and compliance gaps from inconsistent policy enforcement.
The shift to shorter certificate validity periods accelerates all of this. Browsers are pushing maximum validity toward 100 days (March 2027), with proposals for 47 days already in discussion. At that cadence, manual renewal processes don’t just become inefficient — they become impossible to sustain.
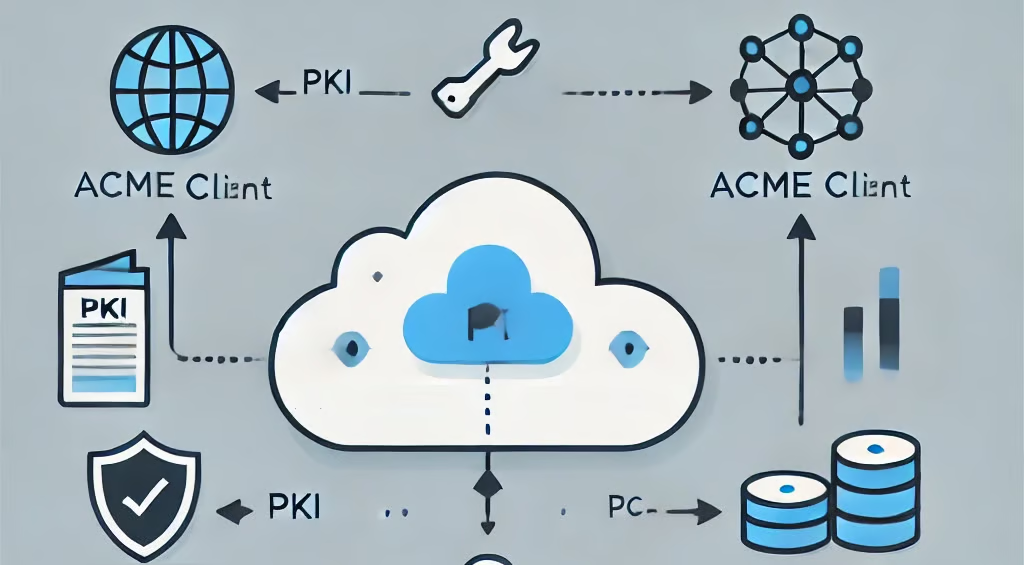
A Serverless Architecture for Certificate Lifecycle Management
Our approach uses fully managed PKI cloud services combined with a serverless infrastructure-as-code deployment. There is no additional software to install or maintain. The entire solution deploys automatically via CI/CD pipelines into a dedicated VPC, giving the customer complete network isolation and the option to own the separate cloud account where it runs.
Core certificate issuance uses AWS Private Certificate Authority, which supports FIPS 140-2 Level 3 requirements for key security. External CAs — GlobalSign, DigiCert, Sectigo, Entrust — can be substituted or run in parallel. The architecture treats the signing layer as replaceable: any technology that provides digital signing can underpin the issuance function.
This design meets HIPAA, PCI DSS, and other regulatory standards through network and logical separation, without requiring bespoke infrastructure for each compliance framework.
ACME Protocol: The Practical Foundation of Automated Provisioning
The ACME protocol is the right foundation for automated SSL certificate lifecycle management. It standardises the entire issuance flow — key generation, validation, installation — and removes the manual steps where errors and delays accumulate.
In practice this means:
- Certificates are requested and renewed automatically, eliminating the category of “expired certificate caused an outage”
- New services get the certificates they need at deployment speed, not at the speed of a ticket queue
- Policy enforcement is consistent because the workflow is standardised, not dependent on whoever ran the manual process last time
Centralised management of ACME clients across the infrastructure extends this further. A single repository — whether on-premises, cloud, or hybrid — handles version control, client health monitoring, and policy enforcement across all endpoints. When a client version needs updating, it updates centrally. When a client goes unhealthy, it alerts. This is the operational model that makes certificate lifecycle management something a generalist IT team can own.
Truststore Management: The Underestimated Problem
Most SSL certificate lifecycle management implementations focus on issuance and renewal, and treat truststore management as an afterthought. This is a mistake. Using certificate authorities not approved by the organisation puts data in transit at risk. Inability to add new CAs quickly limits your ability to automate issuance. Outdated trust anchors across the infrastructure create inconsistent security behaviour that is difficult to diagnose.
Centralised truststore management solves this: trust relationships stay synchronised across all systems, updates propagate quickly, and the risk from compromised or outdated certificates is contained. For application teams, it simplifies operations considerably — they work against a managed, consistent trust baseline rather than managing CA bundles independently per system.
Certificate Validation as an Intelligence Layer
CRL and OCSP services are typically treated as pure infrastructure — necessary plumbing, nothing more. We think that undersells what they can do. When all validation traffic routes through a centralised service, every OCSP request carries a certificate identifier. Aggregated, this data maps your network: which clients connect to which servers, which systems depend on which certificates, and where anomalies appear.
This matters for two teams. PKI and infosec teams get real visibility into certificate utilisation across the enterprise — useful for reporting and identifying orphaned or unmanaged certificates. Cyber defence teams get an independent data set for threat detection: unusual validation request patterns, sudden changes in access behaviour, and early indicators of certificate compromise before it can be exploited.
This kind of intelligence isn’t common in certificate lifecycle management solutions. It requires a level of architectural maturity that most implementations don’t reach. Built in from the start, it changes the value proposition of the PKI from infrastructure cost to active security capability.
Business Intelligence Built In
Certificate data becomes genuinely useful when it’s accessible to the people who need it. We use Amazon QuickSight to deliver built-in analytics dashboards covering certificate status, expiration timelines, renewal activity, and compliance posture across the entire infrastructure.
PKI teams get utilisation reporting. Security teams get validation analytics and threat indicators. Managers get renewal status and system health at a summary level. Compliance teams get automated tracking against security policies and audit-ready reporting. Each team sees the view relevant to their role, drawn from the same underlying data set.
What This Delivers Operationally
The business case for modern certificate lifecycle management for enterprises comes down to three things.
Cost. Serverless architecture eliminates software licensing and the infrastructure overhead of traditional PKI deployments. Pay-as-you-go AWS services mean costs scale with actual usage. Automation reduces the personnel cost of certificate management significantly — and reduces the far larger cost of certificate-related incidents, which run to hundreds of thousands of dollars per outage in lost revenue and recovery time.
Security. Automated renewal with short validity periods limits private key exposure windows. Consistent policy enforcement removes the human error that creates security gaps. FIPS 140-2 Level 3 key protection and VPC isolation meet the requirements of regulated industries. OCSP analytics provide early warning of compromise. The overall security posture is stronger than any manually operated equivalent, and it stays strong as the environment scales.
Operational maturity. Certificate management stops being a specialist function and becomes a standard operational capability. Engineers and administrators manage it like any other automated infrastructure. The PKI team shifts focus from running renewals to reporting, compliance, and continuous improvement — the work that actually reflects a cyber-mature organisation.
The ROI math gets you to “we should automate.” It doesn’t tell you which platform will actually deliver those savings once it meets your change process, CMDB, incident workflows, and platform teams.
Most vendors are strong on the core PKI mechanics and weak on integration into how your company already runs. Our PKI vendor comparison matrix compares market leaders on the parts the glossy ROI decks skip: process fit, integration depth, and real operating cost after year one.
Procurement via AWS Marketplace
For organisations already using AWS, the solution is available directly through AWS Marketplace. This bypasses the standard procurement cycle — no separate contract negotiations, no new vendor onboarding, no additional purchase orders. Costs appear on your regular AWS bill with automated cost allocation and tracking. For enterprise procurement teams, that removes significant friction from the adoption decision.
![Dan Cvrcek [Tsvrcheck]](/blog/assets/images/bio-photo.jpg)