SCEP/NDES Sunset Strategy: Migration When Half Your Estate Can't Move
Simple Certificate Enrollment Protocol was designed in the late 1990s. Microsoft's Network Device Enrollment Service (NDES) implements SCEP as a component of Active Directory Certificate Services. Together, they've been the default certificate enrollment mechanism for devices that can't use browser-based enrollment or manual CSR submission — network equipment, printers, mobile devices via MDM, and a vast range of enterprise endpoints.
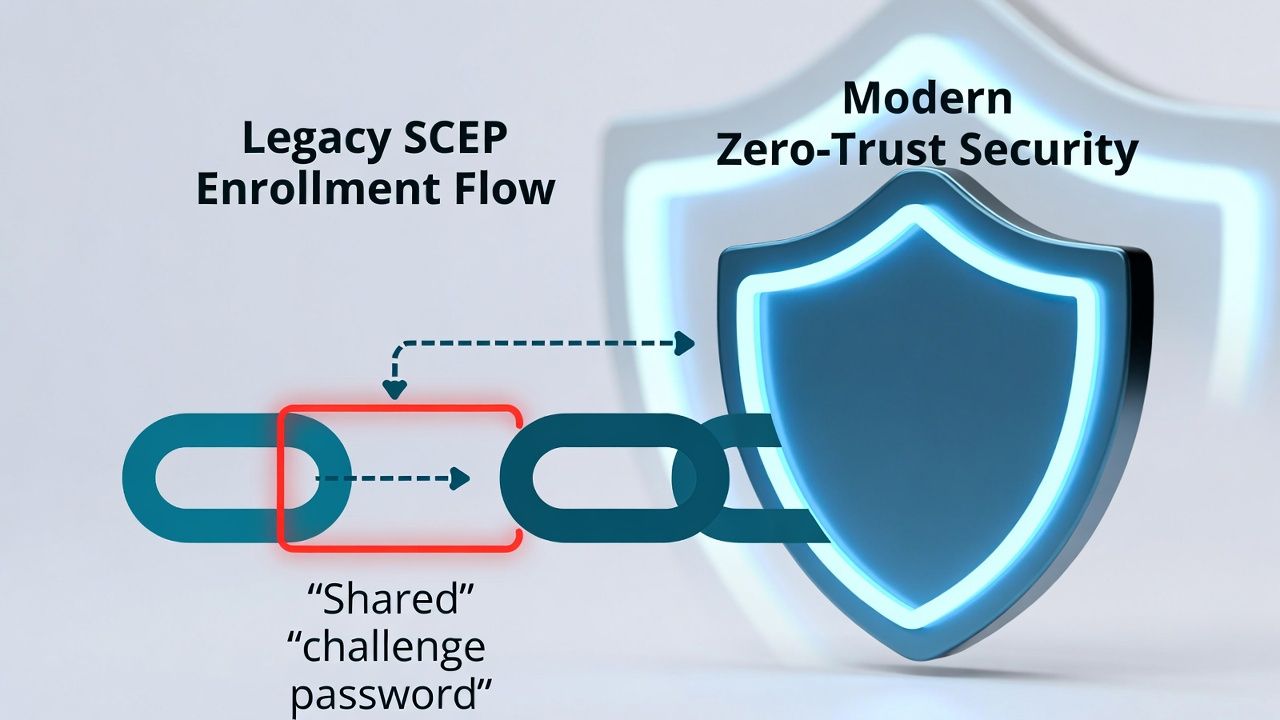
SCEP works. That's the problem. It works well enough that nobody has a burning platform to replace it, despite its security weaknesses being well-documented and increasingly uncomfortable in a zero-trust world.
The security issues are structural. SCEP's authentication model relies on a shared challenge password — a static secret that any device with knowledge of the password can use to request a certificate. In many NDES deployments, the challenge password is the same for every device, effectively making it a pre-shared key that grants certificate enrollment rights to anyone who possesses it. The challenge password is often embedded in MDM profiles, configuration scripts, or documentation, where it can be extracted and reused.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
SCEP provides limited audit capability. The protocol doesn't authenticate the identity of the requesting device in a cryptographically meaningful way — it verifies possession of a shared secret. This means you know that someone with the challenge password requested a certificate, but you don't have strong assurance of which device requested it.
And SCEP has no built-in mechanism for certificate renewal. Renewal workflows are typically built as a separate process layered on top of SCEP, adding complexity and fragility.
The Replacement Landscape
Several modern enrollment protocols address SCEP's weaknesses. None is a direct drop-in replacement for every SCEP use case — which is precisely why migration is hard.
EST (Enrollment over Secure Transport) is SCEP's designated successor, defined in RFC 7030. EST uses TLS for transport security (eliminating the need for SCEP's envelope encryption), supports modern authentication methods (TLS client certificates, HTTP Basic/Digest), and provides a cleaner protocol for initial enrollment, renewal, and CA certificate retrieval. EST is supported by some MDM platforms and network equipment vendors, but coverage is not universal.
ACME (Automatic Certificate Management Environment) is the protocol that powers Let's Encrypt and is increasingly available for private PKI. ACME automates the full certificate lifecycle — request, validation, issuance, renewal — and is the strategic direction for certificate automation. However, ACME requires an ACME client on the enrolling device, which limits its applicability to devices with sufficient compute and connectivity.
MDM-managed provisioning (via SCEP, EST, or proprietary protocols) is the practical replacement for many enterprise device enrollment scenarios. Modern MDM platforms — Intune, Jamf, VMware Workspace ONE — abstract the enrollment protocol from the device, handling certificate requests and installation through their management channel. When MDM is in place, the enrollment protocol becomes an implementation detail that the MDM platform manages.
Cloud-native enrollment from managed PKI services (AWS Private CA Connector for SCEP, Google Cloud CAS, Azure cloud PKI) bridges the gap by providing SCEP-compatible interfaces that front modern CA infrastructure. These services let legacy devices continue using SCEP while the CA backend is modernised — a transitional architecture rather than a permanent solution.
The Device Compatibility Matrix
The real blocker to SCEP sunset isn't protocol availability — it's device support. The decision to migrate away from SCEP is ultimately constrained by what your devices can support.
Modern managed endpoints (Windows 10+, macOS, iOS, Android with MDM) can migrate to EST or MDM-managed enrollment today. These devices have the compute, connectivity, and software update paths to support modern enrollment protocols.
Network equipment (switches, routers, wireless controllers, firewalls) varies dramatically. Recent equipment from major vendors often supports EST or proprietary enrollment protocols. Legacy network equipment — the 10-year-old switches in the distribution closet — may only support SCEP, with no firmware path to anything newer.
Printers and IoT devices are frequently SCEP-only. Many of these devices have no firmware update mechanism, fixed certificate enrollment implementations, and lifespans that extend well beyond the protocol's useful life.
Medical devices in healthcare environments present specific constraints: FDA-cleared devices may require re-certification if firmware is modified, making protocol updates a regulatory process, not just a technical one. Healthcare teams should plan around clinical and regulatory constraints (see IoT certificate lifecycle).
Industrial control systems in manufacturing and OT environments — PLCs, RTUs, HMIs — may have no enrollment protocol support beyond SCEP, and plant shutdown windows are the only opportunity for device-level changes. OT teams should align with plant windows and device constraints (see IoT certificate lifecycle).
Map your device estate against enrollment protocol support before committing to a migration timeline. The map will show you that migration isn't a single project — it's a set of parallel tracks moving at different speeds.
The Parallel-Run Migration Pattern
The only viable migration strategy for most enterprises is parallel operation: run modern enrollment alongside SCEP, migrate device categories as they become capable, and maintain SCEP for the long tail of devices that can't move.
Phase 1: Harden existing SCEP. Before migrating anything, reduce the risk of your current SCEP deployment. Implement per-device challenge passwords (not a shared password), restrict NDES access to known IP ranges or VLANs, enable comprehensive logging on the NDES server, and monitor enrollment requests for anomalies. These measures don't fix SCEP's structural weaknesses but reduce the exploitable surface while migration is underway.
Phase 2: Deploy modern enrollment for new devices. Configure EST or ACME enrollment as the default for all new device deployments. New devices get modern enrollment from day one. This stops the SCEP estate from growing.
Phase 3: Migrate capable existing devices. Working through the device compatibility matrix, migrate device categories to modern enrollment as support becomes available. MDM-managed devices are typically the first wave. Network equipment follows as firmware updates add EST support. Each migration wave reduces the SCEP-dependent population.
Phase 4: Maintain SCEP for residual devices. Accept that some devices will remain on SCEP for years. Medical devices with FDA certification constraints, legacy network equipment on extended maintenance, and industrial controllers in OT environments won't migrate on your preferred timeline. The goal is to minimise and contain the SCEP population, not eliminate it on a specific date.
Cutover criteria for decommissioning SCEP should be defined in advance: all device categories either migrated or on a documented timeline, SCEP enrollment volume below a defined threshold, and remaining SCEP devices isolated to specific network segments with enhanced monitoring.
When SCEP Stays
The honest answer for many enterprises: SCEP will run for another 5-10 years. Not because it's acceptable, but because the device lifecycle demands it.
For the devices that can't move, the strategy is containment. Segment SCEP-dependent devices onto dedicated VLANs. Apply additional network-level controls (port-based authentication, MAC filtering) to compensate for SCEP's weak device authentication. Monitor SCEP enrollment activity for anomalous requests. And document the risk acceptance — SCEP's continued operation should be a conscious, risk-assessed decision visible to security leadership, not an accidental continuation because nobody turned it off.
The M&A dimension adds another layer: acquired companies may bring their own SCEP/NDES infrastructure, their own device estates with SCEP dependencies, and their own timelines for modernisation. PKI due diligence should include SCEP/NDES inventory and migration status.
Sector guides: Healthcare · Manufacturing & OT.

← Back to Certificate Strategy: The Framework Most Organisations Skip
Related guides: IoT certificate lifecycle, regulated PKI implementation.
External References
- RFC 8894: Simple Certificate Enrollment Protocol (SCEP) — ietf.org
- RFC 7030: Enrollment over Secure Transport (EST) — ietf.org
- RFC 8555: Automatic Certificate Management Environment (ACME) — ietf.org
- Microsoft NDES Documentation — learn.microsoft.com
- AWS Private CA Connector for SCEP — aws.amazon.com
