Enterprise mTLS Strategy: The Zero Trust Control Everyone Wants and Nobody Ships
Every zero trust architecture deck includes mutual TLS. Two-way authentication, cryptographic identity for every connection, no implicit trust — it's the security model's poster child. Netflix, Uber, and Google have built their internal security around mTLS and SPIFFE-based workload identity. Service meshes make east-west mTLS a checkbox deployment.
And yet, outside of service mesh contexts, enterprise mTLS adoption is strikingly low. The gap between intent and deployment is enormous, and it's not a technology gap. The protocols work. The libraries exist. cert-manager, Istio, Linkerd — the tooling is mature.
The gap is operational. mTLS projects fail on rollout planning, user experience, break-glass procedures, and the sheer organisational complexity of issuing, distributing, and managing client certificates at enterprise scale. The CISO who approves the project isn't the one explaining to the CEO why their laptop can't connect to the VPN on Saturday.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Why mTLS Adoption Lags Zero Trust Ambition
Standard TLS authenticates the server to the client — your browser confirms the website is who it claims to be. mTLS adds the reverse: the server also authenticates the client. Both sides present certificates, both sides validate, and the connection is established only when mutual trust is confirmed.
For service-to-service communication within controlled infrastructure, mTLS is straightforward. Both endpoints are managed, certificates are issued programmatically, and humans aren't involved. Service meshes have made this pattern trivially deployable.
For user-facing or device-facing mTLS — where the "client" is a person's laptop, a contractor's device, or a mobile phone — the challenges multiply. Certificate provisioning requires touching every endpoint. Key storage varies by device type and OS. Certificate renewal requires either automation that works across all device types or manual processes that users must complete correctly. Revocation must work instantly when a device is lost or compromised. And the user experience of certificate-based authentication — browser prompts, certificate selection dialogs, PIN entry for smart cards — is unfamiliar and often confusing.
These aren't theoretical concerns. They're the reason most enterprise mTLS projects stall between pilot and production.
The Phased Rollout Framework
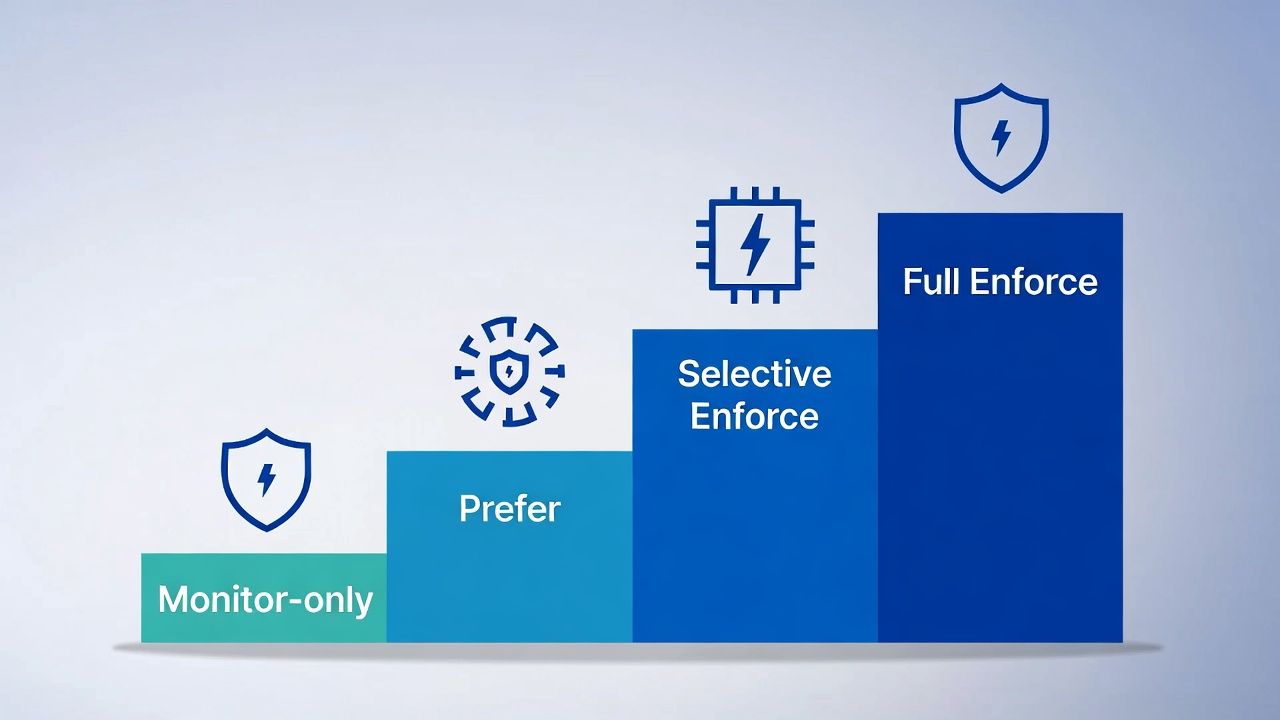
The organisations that successfully deploy enterprise mTLS share a common approach: they don't hard-cut. They phase.
Phase 1: Monitor-only. Deploy mTLS infrastructure and configure servers to request client certificates but not require them. Log which connections present valid certificates and which don't. This phase reveals your actual certificate deployment coverage, identifies devices and applications that don't support client certificates, and surfaces configuration issues — all without affecting production access.
Phase 2: Enforce-on-fallback. Configure servers to prefer mTLS but accept connections without client certificates, while logging the gap. Begin requiring mTLS for internal-only services with low user impact. This phase builds operational confidence and identifies the long tail of systems that need certificate provisioning.
Phase 3: Selective enforcement. Require mTLS for high-value services — administrative interfaces, sensitive data access, privileged API endpoints. Maintain fallback authentication (MFA, SSO) for general access. This phase delivers the highest security value with the lowest blast radius.
Phase 4: Full enforcement. Require mTLS for all connections within scope. At this point, break-glass procedures must be tested, help desk runbooks must be complete, and certificate provisioning must cover 100% of intended endpoints. Organisations that reach this phase typically do so 12-18 months after starting Phase 1.
The temptation to skip directly to Phase 4 is strong and always wrong. Every skipped phase is a production incident you'll discover during enforcement rather than during monitoring.
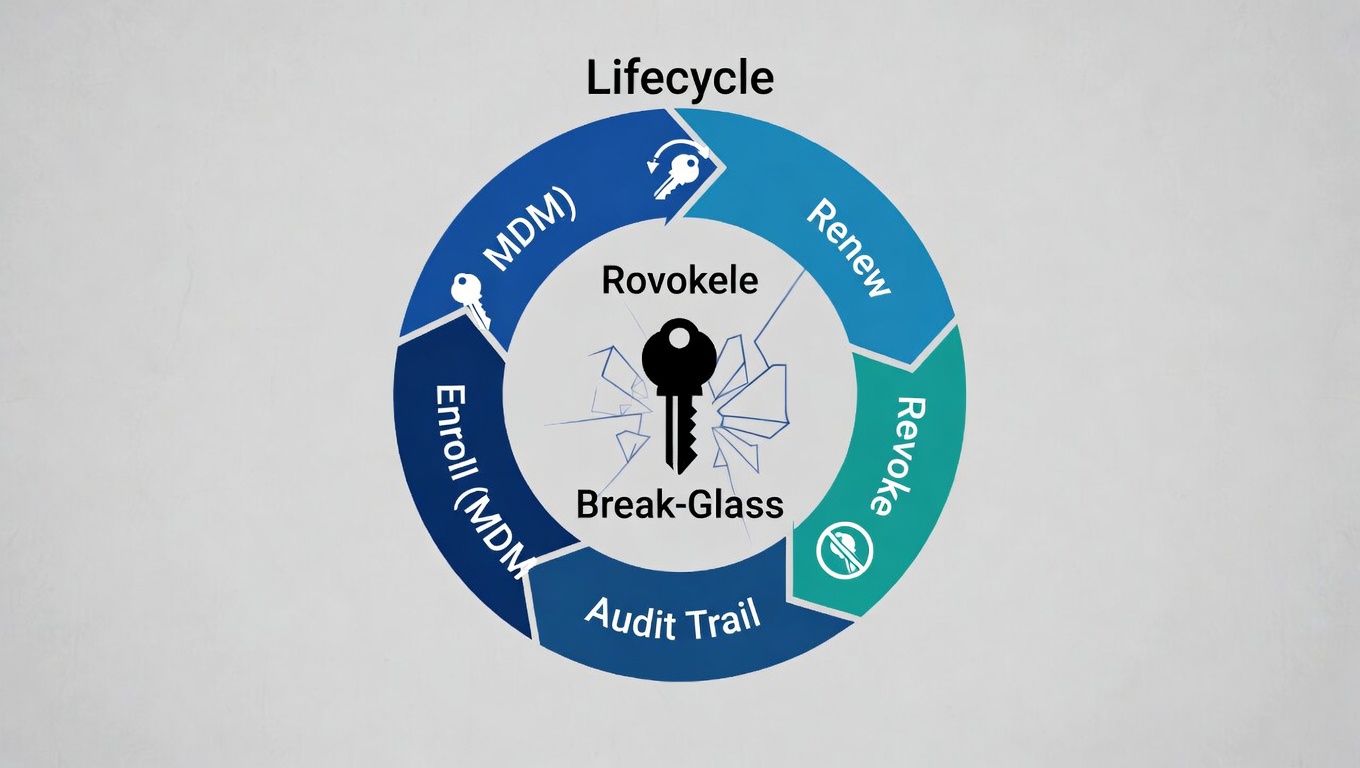
Break-Glass Procedures
Break-glass is the operational question that separates mTLS projects that succeed from those that get rolled back.
When mTLS is enforced, a certificate failure means access failure. The scenarios are predictable: a certificate expires because automation failed, a device is rebuilt without its certificate being reprovisioned, a user's smart card is damaged, or a certificate is revoked for a device that's still in use. In each case, someone who should have access doesn't.
A break-glass procedure provides emergency access that bypasses mTLS enforcement temporarily, under controlled conditions. The design principles are: break-glass should be auditable (every use is logged and reviewed), time-limited (access expires within a defined window), approval-gated (requires authorisation from a defined authority), and rare (frequent use means your primary authentication path is broken).
Common break-glass patterns include: temporary fallback to MFA-only authentication for specific users or endpoints, one-time-use certificate issuance via a separate emergency provisioning channel, emergency certificate re-provisioning via MDM push, and physical token or smart card override for on-premises access.
The break-glass design must account for cascade failures. If your certificate authority is down and your MDM platform depends on the same infrastructure, your emergency provisioning channel doesn't work either. Break-glass should have minimal dependencies on the infrastructure it's designed to bypass.
Enrollment and Provisioning
Certificate provisioning is the operational bottleneck of enterprise mTLS. The mechanism you choose determines adoption speed, user experience, and ongoing management overhead.
MDM-managed provisioning is the cleanest path for organisations with mature device management. Intune, Jamf, VMware Workspace ONE, and similar platforms can push certificate profiles to managed devices. The certificate request, issuance, and installation happen silently. Users don't see it. This is ideal but limited to devices under MDM control — it doesn't cover personal devices, contractor laptops, or legacy systems.
SCEP enrollment remains common in enterprises with existing Microsoft ADCS infrastructure. NDES (Network Device Enrollment Service) bridges between SCEP clients and the CA. The protocol is old, the security model has known weaknesses (static challenge passwords), and it's being sunset in favour of modern alternatives — but it works today and many MDM platforms integrate with it natively. See SCEP/NDES Sunset Strategy for the migration path.
ACME-based enrollment is the modern approach for managed infrastructure. Where ACME clients can be deployed (servers, containers, managed workstations), ACME provides automated certificate lifecycle management with the same protocol used for public TLS certificates. The limitation is client-side support — end-user devices don't typically run ACME clients natively.
Manual enrollment — user-initiated CSR generation, certificate download, and installation — is the option of last resort. It's error-prone, doesn't scale, and creates support burden. Some organisations use self-service portals that guide users through the process, but the UX remains poor compared to MDM-managed provisioning. Reserve manual enrollment for edge cases: contractor devices, BYOD, and systems that don't support any automated provisioning mechanism.
The provisioning strategy should match your device landscape. Most enterprises need a combination: MDM for managed endpoints, SCEP or ACME for infrastructure, and a self-service fallback for everything else.
Client Certificate Lifecycle at Scale
Issuance is the beginning, not the end. Client certificates have a full lifecycle that needs operational planning.
Renewal is the most critical operational concern. If client certificates expire without renewal, users lose access. Automated renewal via MDM or ACME is the target state. For certificates that can't be auto-renewed, alerting must give sufficient lead time — 30 days minimum for manual processes. Your certificate observability should track client certificate expiry across the entire estate.
Revocation is one of the few contexts where revocation actually matters. A lost or stolen device with a valid client certificate can authenticate as a trusted endpoint. Revocation must be fast (hours, not days) and the relying party must check revocation status before accepting connections. CRL distribution or OCSP with hard-fail enforcement is essential. Short-lived client certificates (24-72 hour lifetimes with automated renewal) can reduce the revocation dependency, but the enrollment infrastructure must be reliable enough to support frequent renewal without degrading user experience.
Key recovery and migration arise when users change devices. The client certificate on the old device needs to be revoked, and a new certificate needs to be provisioned to the new device. If the private key is stored in a hardware-backed keystore (TPM, Secure Enclave), it can't be migrated — a new key pair and certificate are required. The provisioning workflow must handle this gracefully.
Cross-device certificates are relevant for users who access services from multiple devices (laptop, phone, tablet). Each device needs its own certificate with its own key pair. The identity model must support multiple active certificates per user, and your observability and revocation processes must handle per-device lifecycle independently.
mTLS Beyond the Perimeter
Enterprise mTLS increasingly extends beyond internal infrastructure. B2B API connections, partner integrations, and regulatory mandates are driving mTLS adoption for external-facing connections.
PSD2 and Open Banking in financial services mandate mutual TLS for connections between Account Servicing Payment Service Providers (ASPSPs) and Third Party Providers (TPPs). This isn't optional — it's a regulatory requirement for institutions operating in the EU and UK.
API gateway platforms — Kong, Apigee, AWS API Gateway — increasingly support mTLS as an authentication mechanism for API consumers. This pattern replaces or supplements API keys and OAuth tokens with certificate-based identity, providing cryptographic assurance of the caller's identity.
For B2B mTLS, the trust model adds complexity. You need to either issue certificates to your partners from your private PKI (which requires them to trust your root) or accept certificates from their PKI (which requires you to trust theirs). Cross-organisation trust anchor management is a governance challenge that technical teams often underestimate.
Sector guides: Financial services · Healthcare.
← Back to Certificate Strategy: The Framework Most Organisations Skip
Related guides: Regulated PKI implementation, Machine identity & zero trust.
External References
- SPIFFE: Secure Production Identity Framework for Everyone — spiffe.io
- PSD2 / Open Banking mTLS Requirements — European Banking Authority
- NIST SP 800-207: Zero Trust Architecture — nist.gov
- Istio mTLS Configuration — istio.io
- Linkerd mTLS — linkerd.io
