SCEP/NDES Sunset Strategy for Manufacturing & OT
The core SCEP/NDES sunset strategy covers the replacement landscape and parallel-run migration pattern. Manufacturing and OT environments face the most extreme version of the migration problem: devices that literally cannot support anything beyond SCEP, maintenance windows measured in days per year, and failure modes where a certificate issue stops a production line.
Industrial Control System Enrollment: Beyond SCEP's Limitations
Industrial control systems — PLCs, RTUs, HMIs, SCADA servers, DCS controllers — were not designed with certificate lifecycle management in mind. Many support SCEP because it was the only option available when network connectivity was added to these devices. Some support only static certificate installation during commissioning (no enrollment protocol at all).
The device categories in manufacturing and OT, ranked by migration difficulty:
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Modern IT-adjacent OT (historians, SCADA servers, engineering workstations): These run standard operating systems and can migrate to EST or ACME. Treat like enterprise IT devices.
Network infrastructure in OT zones (managed switches, wireless access points, firewalls): Similar to enterprise network equipment but with stricter change management. Firmware updates that add modern enrollment support may be available but require validation in an OT test environment.
Industrial controllers and edge devices (PLCs, RTUs, HMIs, IoT gateways): The hard category. Many support only SCEP or static certificate loading. Firmware updates may not be available, and applying firmware updates to safety-critical controllers requires comprehensive testing and often regulatory or safety approval.
Legacy embedded devices (sensors, actuators, specialised equipment): No enrollment protocol support. Certificates, if used at all, are provisioned during manufacturing and replaced only when the device is physically serviced.
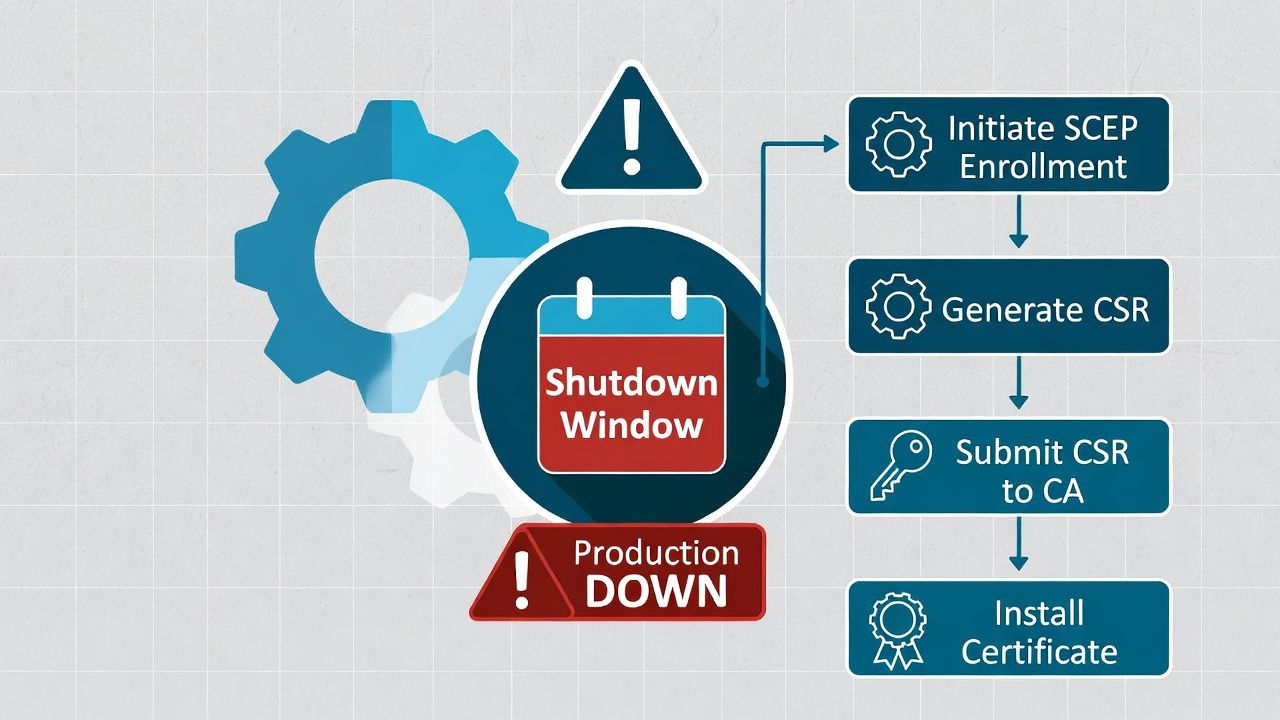
Plant Shutdown Windows as Certificate Migration Opportunities
Manufacturing facilities operate on production schedules with defined maintenance windows — typically annual or semi-annual shutdowns for equipment maintenance, calibration, and upgrades. These shutdowns are the primary opportunity for certificate-related device changes.
Certificate migration activities must be planned alongside other shutdown maintenance: re-enrollment of devices onto new CA infrastructure, trust anchor updates on devices that can't reach the IT network during normal operations, and firmware updates that add modern enrollment protocol support.
The planning window for shutdown activities is typically 3-6 months ahead. Certificate migration tasks must be scoped, tested in a lab environment, and documented with rollback procedures before the shutdown. There is no tolerance for extending a plant shutdown because a certificate migration failed.
For devices that can be reached during normal operations (via the OT network), certificate maintenance can happen outside shutdown windows — but change management in OT environments is far more restrictive than IT. Any change to a running production system requires safety analysis, approval from operations, and often a hot standby configuration to allow rollback.
Safety-Critical Systems: When Certificate Expiry Stops Production
In manufacturing, a certificate expiry on a PLC controlling a chemical process, a robotic welding cell, or a packaging line doesn't generate a help desk ticket. It stops production. The cost is measured in lost output — thousands to millions of pounds per hour depending on the facility.
This changes the certificate lifecycle strategy fundamentally. Certificates on safety-critical OT devices must have expiry monitoring with lead times of 90+ days, renewal procedures documented and rehearsed with the operations team, and fallback configurations that allow the system to continue operating if certificate renewal fails (graceful degradation rather than hard failure).
Some OT environments implement certificate validity checking in "warn" mode rather than "fail" mode — the system logs an expiry warning but doesn't reject the connection. This trades security for availability, which in a safety-critical OT context may be the correct trade-off. The decision should be documented in the risk assessment.
Vendor Coordination
Unlike enterprise IT, where you control your own firmware updates, OT device firmware updates depend on the device vendor. Getting modern enrollment support (EST, ACME) into PLC firmware requires the PLC vendor to develop, test, and release the update — on their timeline, not yours.
Proactive engagement with device vendors is part of the SCEP sunset strategy for manufacturing. Include enrollment protocol modernisation in vendor discussions, procurement requirements, and contract renewals. New device purchases should specify EST or ACME support as a requirement.
Related in this cluster: Certificate strategy hub · Private PKI · mTLS · M&A PKI · Multi-CA · Revocation · Certificate Transparency · CAA & DNS trust · Kubernetes TLS · Edge TLS · Code signing · Observability · SCEP / NDES sunset.

