Private PKI Strategy for Manufacturing & OT
The core private PKI strategy assumes connected infrastructure with ACME-capable endpoints and automated lifecycle management. Manufacturing and OT environments break most of those assumptions. Air-gapped networks, 15-25 year device lifetimes, limited device compute, and safety-critical operational constraints create a fundamentally different PKI environment.
OT Network Certificate Architecture: Air-Gapped and Semi-Connected Models
OT networks are typically segmented from IT networks — by design, by regulation (IEC 62443), and by operational necessity. Many OT environments are air-gapped or semi-connected, with tightly controlled data transfer between IT and OT zones.
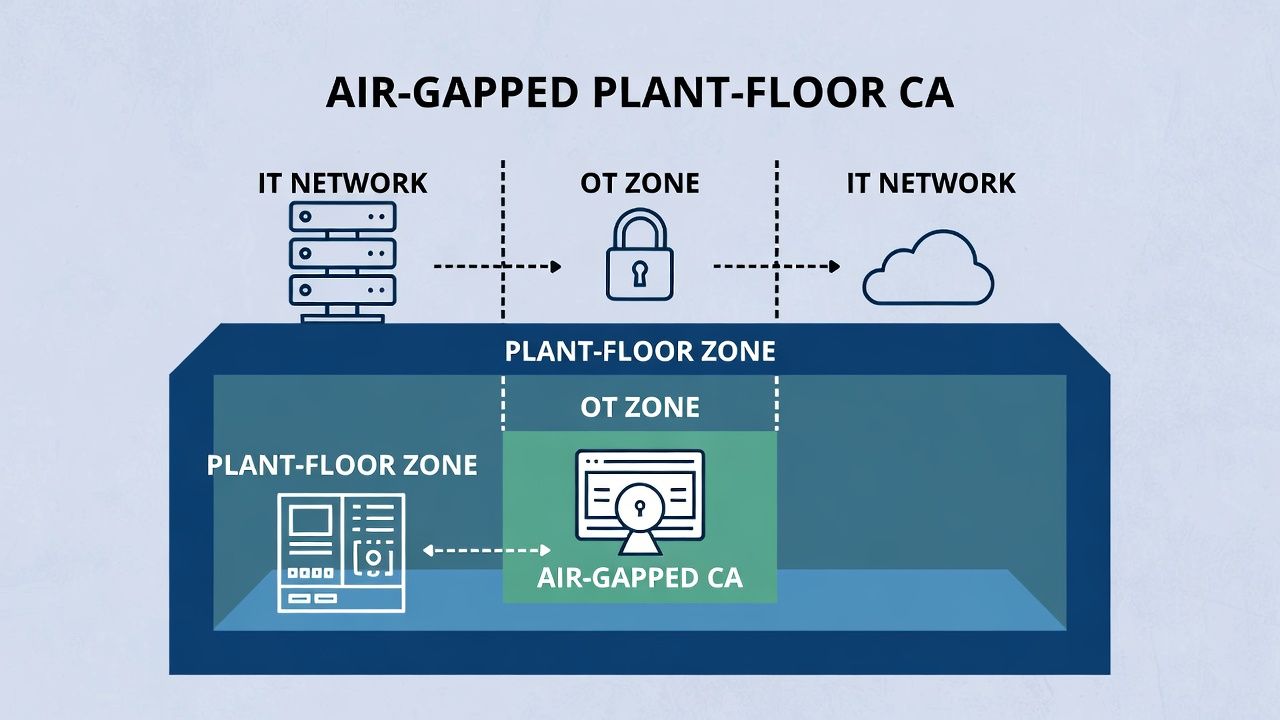
An air-gapped OT network can't reach an ACME server on the IT network. CRL distribution points that rely on HTTP access aren't reachable. OCSP responders are unavailable. The CA infrastructure for OT certificates must either reside within the OT zone or use offline certificate issuance and manual distribution.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Architectures that work: a subordinate CA deployed within the OT zone, issuing certificates locally (with the root CA in the IT zone, connected only during certificate signing ceremonies). Alternatively, certificates can be pre-generated and loaded onto devices during commissioning or scheduled maintenance, with replacement certificates prepared in advance and staged for deployment during plant shutdown windows.
Both approaches require procedures that the IT PKI team may find unfamiliar — certificate provisioning as a physical activity, performed by engineers in the plant, not by automation running in a data centre.
IT/OT Convergence: Unifying Two PKI Worlds Without Breaking Production
IT/OT convergence is connecting factory floor devices to enterprise networks for data analytics, remote monitoring, and predictive maintenance. This creates a trust boundary problem: IT systems need to authenticate OT devices, and OT systems need to trust IT services.
If IT and OT operate separate PKI hierarchies with separate root CAs, cross-zone communication requires cross-certification or trust anchor exchange. If they share a single PKI hierarchy, the IT CA infrastructure must meet OT availability requirements — which are far more stringent than IT norms (99.999% uptime, where certificate failure means production stops).
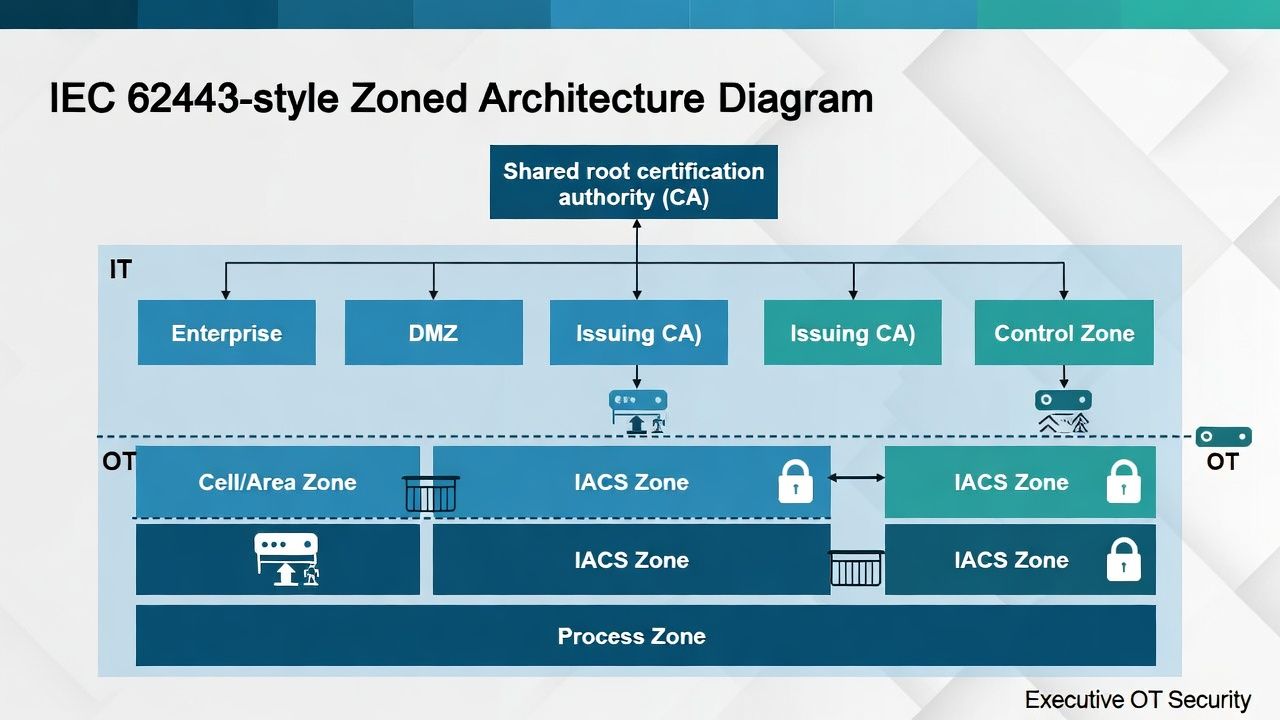
The practical architecture for most manufacturers is a shared root CA with separate issuing CAs for IT and OT zones. The root CA is the common trust anchor. The OT issuing CA is deployed within or adjacent to the OT zone with operational independence from IT infrastructure. This provides unified trust without creating an IT dependency that OT operations can't tolerate.
Long-Lived Devices, Short-Lived Certificates: The Renewal Challenge
An industrial PLC deployed in 2020 may run until 2040. The certificate issued to that PLC has a much shorter lifetime — 1-3 years, or potentially shorter under updated policies. Over the device's operational life, the certificate must be renewed 10-20+ times.
For devices that support automated renewal (via EST or ACME), this is manageable — assuming the enrollment infrastructure remains available and compatible for the device's entire operational life. For devices with manual certificate provisioning, each renewal is a maintenance event that may require physical access to the device, potentially during a plant shutdown.
The strategic response is to invest in enrollment automation for OT devices that support it, accept manual renewal processes for devices that don't, and align certificate renewal schedules with planned maintenance windows to minimise unscheduled access.
IEC 62443 and Certificate Requirements for Industrial Automation
IEC 62443 (Industrial Automation and Control Systems Security) defines security levels and requirements for industrial control system environments. The standard's requirements for identification and authentication, communication integrity, and data confidentiality all map to certificate-based controls.
Zones and conduits — the fundamental IEC 62443 architectural concept — align naturally with PKI trust boundaries. Each zone can have its own certificate policy appropriate to its security level. Conduits between zones can use mTLS for authenticated, encrypted communication. The certificate architecture becomes a technical implementation of the zone/conduit model that IEC 62443 requires.
Related in this cluster: Certificate strategy hub · Private PKI · mTLS · M&A PKI · Multi-CA · Revocation · Certificate Transparency · CAA & DNS trust · Kubernetes TLS · Edge TLS · Code signing · Observability · SCEP / NDES sunset.