M&A PKI Strategy for Manufacturing
The core M&A PKI playbook covers due diligence, acquisition phases, and divestiture. Manufacturing acquisitions add OT-specific complexity: factory floor networks with independent PKI, product identity certificates as intellectual property, and industrial certifications that constrain PKI changes.

Factory Network PKI: What You Inherit in a Manufacturing Acquisition
When you acquire a manufacturing company, you acquire their factory networks — and whatever PKI infrastructure (or lack thereof) exists within those networks. The range of what you might find is wide.
Best case: The acquired factory has a managed OT network with certificate-based device authentication, a documented private CA, and an inventory of device certificates. Integration follows the standard playbook with OT-specific timing constraints.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Typical case: The factory has some certificate usage — wireless authentication for mobile devices, VPN for remote access, TLS for SCADA web interfaces — but no centralised CA. Certificates were generated ad hoc, possibly with self-signed CAs, and nobody has a complete inventory.
Worst case: No certificate infrastructure. Devices communicate over unencrypted protocols. Authentication is password-based or nonexistent. The acquisition is an opportunity to establish PKI from scratch — but the timeline for deploying certificates to existing industrial equipment is measured in years.
Due diligence for manufacturing acquisitions should include a physical assessment of factory network infrastructure alongside the standard PKI inventory questions. Remote assessment tools won't reach air-gapped OT networks.
Product Identity PKI as Acquired Intellectual Property
Some manufactured products carry digital identity — certificates baked into firmware at manufacturing that identify the product to cloud services, to other devices in an ecosystem, or to the end customer's infrastructure.
These product identity certificates are typically issued from a product-specific CA hierarchy. The CA root key, the issuing CA infrastructure, and the certificate provisioning line are part of the acquired intellectual property. Customers' deployed products trust certificates from this specific CA hierarchy. Changing the root CA would require updating the trust store on every deployed product — which may be technically impossible for devices without an update mechanism.
The M&A treatment of product identity PKI: treat the CA infrastructure as a critical acquired asset. Document it during due diligence. Maintain it independently post-acquisition until a product lifecycle transition (new product generation) provides a natural point to integrate or replace the CA hierarchy.
Industrial Certification Constraints on PKI Changes
Manufactured products may carry industrial certifications — UL, CE marking, TÜV, ATEX, IECEx — that reference specific configurations, including firmware and security configurations. If a certificate or PKI component is part of the certified configuration, changing it may invalidate the certification.
This creates a PKI integration constraint that doesn't exist in other verticals. Before modifying certificate infrastructure on certified equipment, assess whether the change affects certified configurations. If it does, the certification body must be consulted, and re-certification may be required — a process that takes months and has direct market access implications.
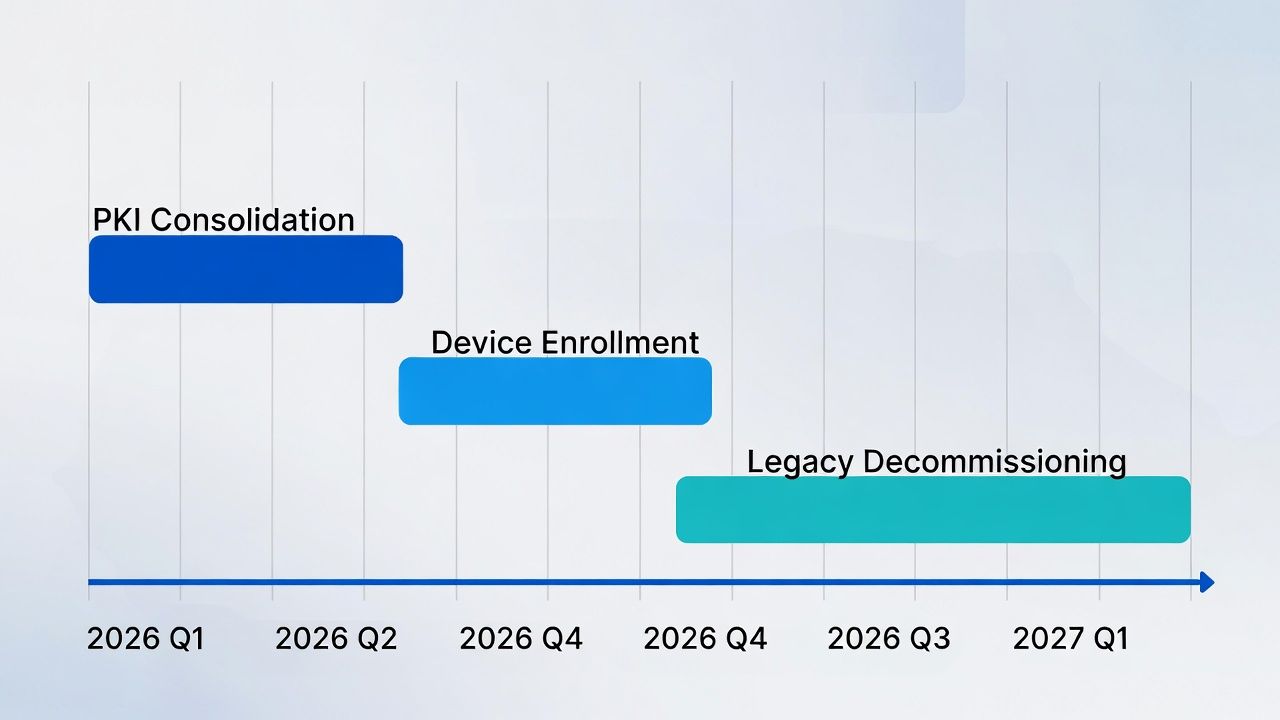
Integration Playbook: Manufacturing Acquisition PKI Timeline
Phase 1 (Months 1-6): IT PKI cross-trust and consolidation. Factory IT systems (email, ERP, engineering workstations) follow the standard playbook.
Phase 2 (Months 6-18): OT network assessment and planning. Inventory factory floor certificates, assess device capabilities, and plan OT PKI integration. This phase is primarily planning, not execution.
Phase 3 (Months 18-36): OT PKI integration, aligned with plant shutdown windows and production schedules. Migrate devices that can be migrated. Establish parallel CA infrastructure for the OT zone.
Total timeline: 24-36 months for full integration, with some OT devices remaining on legacy PKI until device end-of-life replacement.
Related in this cluster: Certificate strategy hub · Private PKI · mTLS · M&A PKI · Multi-CA · Revocation · Certificate Transparency · CAA & DNS trust · Kubernetes TLS · Edge TLS · Code signing · Observability · SCEP / NDES sunset.