Firmware Signing Strategy for Manufacturing
The core code signing strategy covers key protection, CI/CD integration, timestamping, and governance. Manufacturing firmware signing adds dimensions that enterprise software signing doesn't face: hardware root of trust, secure boot chains, multi-vendor component signing, regulatory mandates from the EU Cyber Resilience Act, and the challenge of signing updates for devices already deployed in the field.
Firmware Signing as Product Security
In enterprise IT, code signing protects the software supply chain within your organisation. In manufacturing, firmware signing protects your customers. A compromised firmware update pushed to deployed industrial controllers, consumer IoT devices, or medical equipment directly endangers the people and systems that use your products.
This shifts firmware signing from an IT governance concern to a product security concern. The signing keys, processes, and governance should be owned by the product security team, not the IT security team. The business case isn't "protect our build pipeline" — it's "protect our customers and our product liability exposure."
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
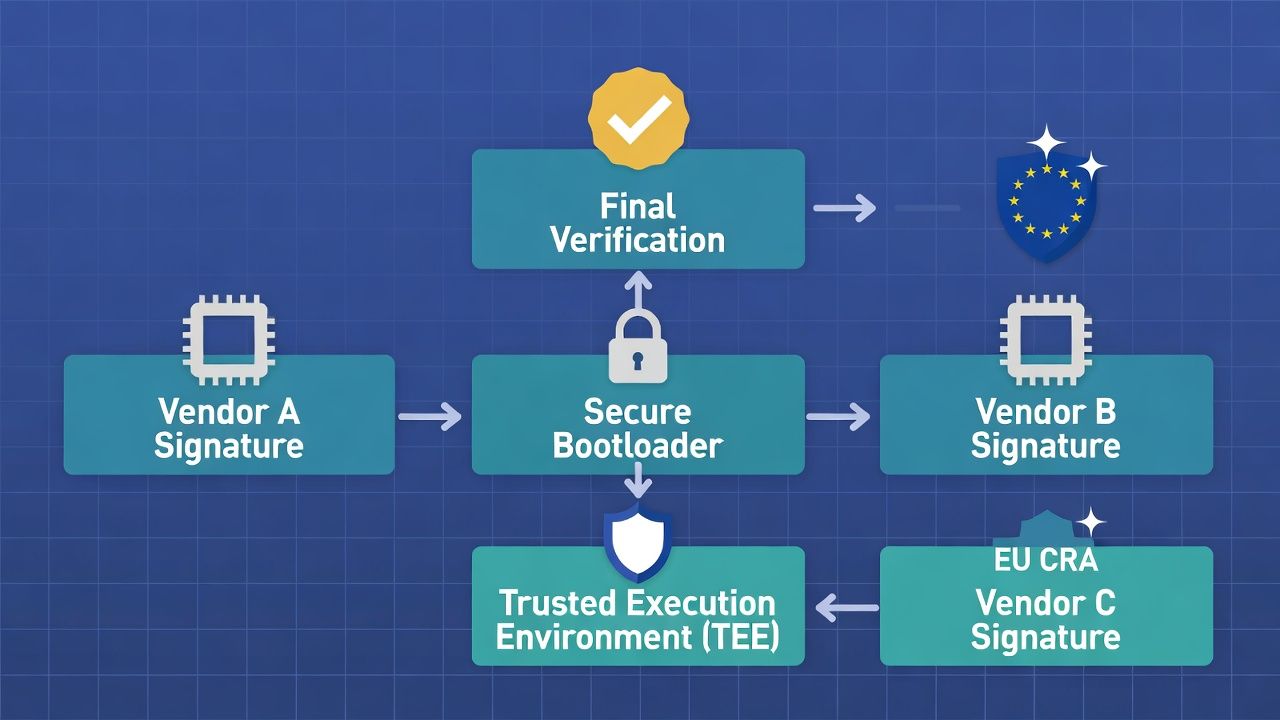
Secure Boot Chain Architecture
Secure boot ensures that only authenticated firmware can execute on a device. The trust chain typically runs: hardware root of trust (ROM-based, immutable) → bootloader (signed with a manufacturer root key) → OS/RTOS (signed with a platform key) → application firmware (signed with an application key).
Each stage in the boot chain verifies the next before allowing execution. A compromised or unsigned component at any stage halts the boot process. The certificate architecture must support this chain — each signing key corresponds to a stage, with the root key being the most tightly protected (typically burned into device hardware at manufacturing).
Key management for secure boot requires: hardware-stored root keys that cannot be extracted post-manufacturing, a subordinate key hierarchy that allows component-level signing without exposing the root key, key revocation mechanisms that can invalidate compromised intermediate keys without bricking devices (this is genuinely hard and must be designed from the start), and key provisioning during manufacturing that scales to production volumes.
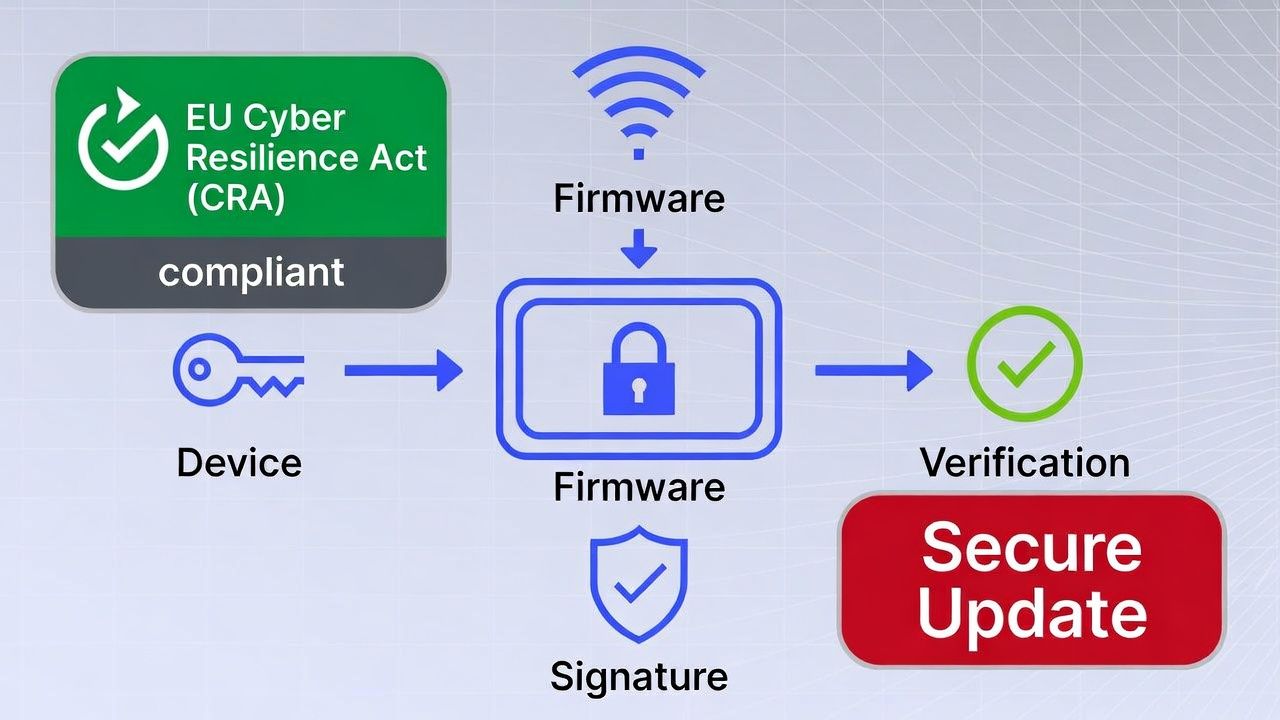
EU Cyber Resilience Act: Mandatory Software Update Signing
The EU Cyber Resilience Act (CRA), entering enforcement in phases from 2025-2027, introduces mandatory cybersecurity requirements for products with digital elements sold in the EU market. Among its requirements: manufacturers must ensure the integrity and confidentiality of software updates, and updates must be delivered securely with verified authenticity.
In practice, this means firmware signing is no longer a best practice for products sold in the EU — it's a legal requirement. The CRA also requires a documented vulnerability handling process, coordinated disclosure, and a Software Bill of Materials (SBOM), all of which interact with firmware signing governance.
Manufacturers outside the EU selling into the EU market must comply. This makes firmware signing strategy a market access question, not just a security question.
Supply Chain Signing: Multi-Vendor Component Integrity
Modern manufactured products contain firmware components from multiple vendors — chipset firmware, communication module firmware, sensor firmware, and application firmware may each come from different suppliers. Each component should be independently signed by its vendor, and the final product firmware should verify all component signatures during assembly or boot.
The trust model requires maintaining a registry of trusted vendor signing certificates, validating vendor signatures during incoming component inspection (or at boot time), and establishing contractual requirements for vendor signing practices — including key protection, timestamping, and revocation procedures.
OTA Update Signing for Deployed Device Fleets
For devices deployed in the field — from consumer IoT to industrial equipment — firmware updates are delivered over-the-air (OTA). Every OTA update must be signed and verified by the device before installation. An unsigned or incorrectly signed update should be rejected.
The OTA signing challenge at scale: signing infrastructure must handle high-throughput signing operations during release pushes, update verification must work on devices with limited compute (some embedded devices can't verify RSA-4096 signatures in reasonable time — algorithm and key size must match device capability), and rollback protection must prevent downgrade attacks where an attacker pushes an older, vulnerable firmware version with a valid signature.
Related in this cluster: Certificate strategy hub · Private PKI · mTLS · M&A PKI · Multi-CA · Revocation · Certificate Transparency · CAA & DNS trust · Kubernetes TLS · Edge TLS · Code signing · Observability · SCEP / NDES sunset.