Private PKI Strategy for Healthcare
The core private PKI strategy covers when to run your own CA, cost analysis, and internal ACME. Healthcare adds three drivers that strengthen the case for private PKI: connected medical device trust, health information exchange requirements, and HIPAA audit obligations.
Connected Medical Device Trust: Private CA Requirements
Connected medical devices that communicate over the hospital network — sending telemetry, receiving orders, transmitting results — need authenticated and encrypted connections. Public CA certificates don't make sense for devices that never communicate with the public internet.
Private PKI for medical devices requires: device-specific certificates with identifiers that map to your clinical asset management system, a CA architecture that supports the enrollment protocols your devices actually speak (SCEP for legacy devices, EST or ACME for newer ones), certificate lifetimes that account for device maintenance schedules (clinical devices can't interrupt patient care for certificate renewal), and trust anchor distribution to the clinical systems that validate device certificates.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
The device identity model matters. A certificate that identifies a specific infusion pump by serial number provides stronger authentication than one that identifies "a device in the ICU." Asset-to-certificate mapping enables precise access control and audit — both of which HIPAA requires.
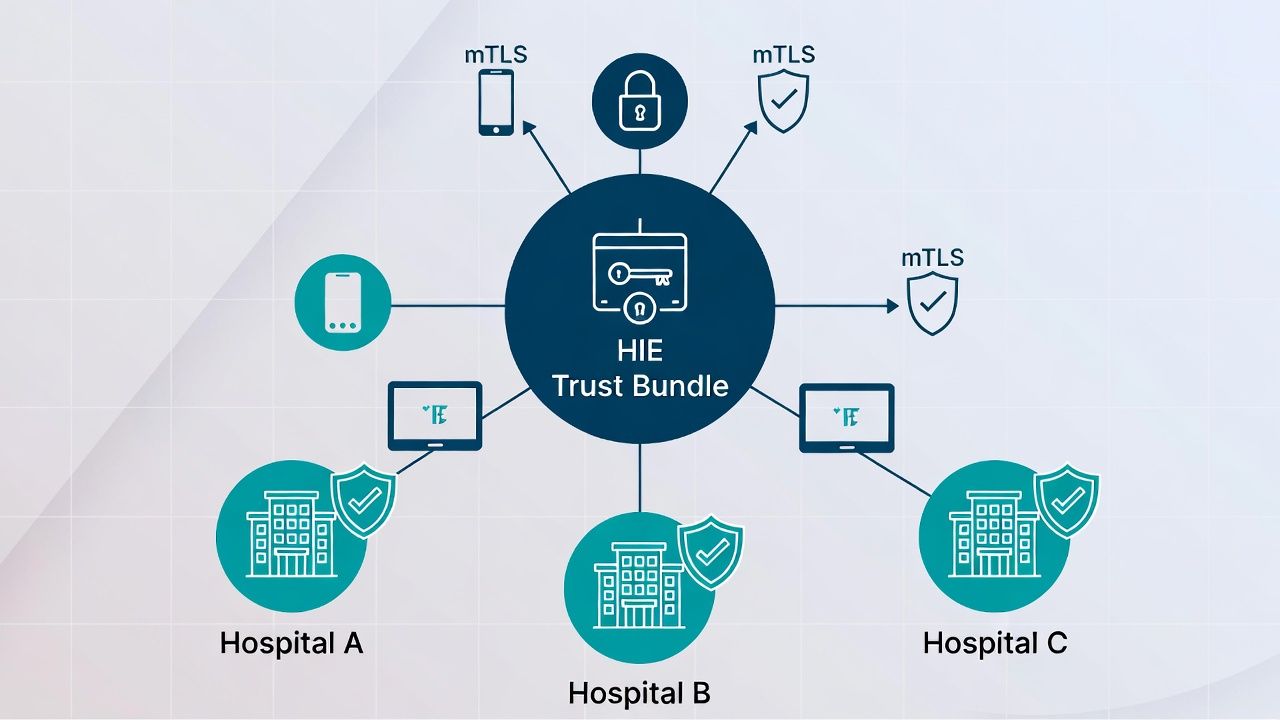
Health Information Exchange Certificate Architecture
Health Information Exchanges (HIEs) enable clinical data sharing between organisations — hospitals, clinics, laboratories, pharmacies. HIE connections use certificates for mutual authentication between participating organisations.
Each participating organisation presents certificates from its own PKI. Trust is established through the HIE framework's trust anchor distribution — typically a shared trust bundle maintained by the HIE operator. This creates a federated trust model where your private CA issues certificates for your systems, and the HIE framework ensures that other participants trust your CA (and vice versa).
The certificate management requirements include: compliance with the HIE's certificate policy (key sizes, algorithms, naming conventions, validity periods), automated certificate renewal that accounts for HIE connectivity testing requirements, and incident response procedures coordinated with the HIE operator when a certificate issue affects data exchange.
HIPAA-Aligned Key Management and Audit Controls
HIPAA's Security Rule requires audit controls for ePHI access and integrity controls for ePHI in transit. Private PKI operations that protect ePHI must maintain audit trails that satisfy HIPAA's requirements — which, while less prescriptive than SOX, still require demonstrable controls.
Specifically: CA operations must be logged and the logs must be protected from modification, key access must be restricted to authorised personnel with documented roles, key management procedures must be documented as part of your HIPAA Security Rule policies, and breach notification procedures must account for CA key compromise as a potential breach of ePHI (since a compromised CA key could enable traffic interception or device impersonation).
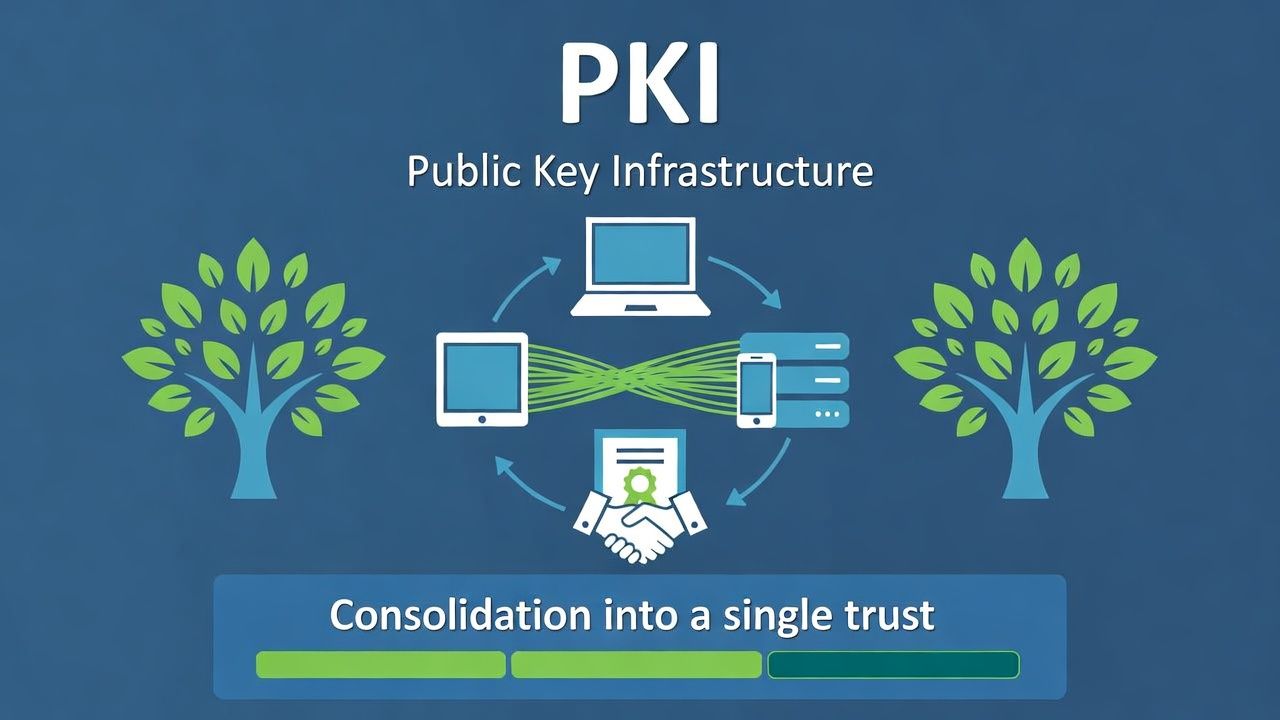
Multi-Facility Health Systems: Unifying PKI After Acquisitions
Health systems grow through acquisition — acquiring community hospitals, physician practices, and specialty clinics. Each acquired facility may operate its own IT infrastructure, including its own PKI (or no PKI at all).
The M&A PKI integration playbook applies directly: cross-trust first, consolidation second, rationalisation third. The healthcare-specific consideration is that acquired facilities often have connected medical devices with certificates from the old PKI that can't be easily re-issued. Cross-trust must extend to the medical device trust anchors, and the slow-track migration timeline for medical devices must be factored into the PKI rationalisation plan.
Related in this cluster: Certificate strategy hub · Private PKI · mTLS · M&A PKI · Multi-CA · Revocation · Certificate Transparency · CAA & DNS trust · Kubernetes TLS · Edge TLS · Code signing · Observability · SCEP / NDES sunset.