mTLS & Client Certificate Strategy for Healthcare
The core mTLS strategy provides the phased rollout framework, break-glass design, and enrollment patterns. Healthcare introduces constraints that don't exist in other verticals: shared workstation models, clinical workflow integration, FDA-regulated devices, and a break-glass calculus where patient safety fundamentally overrides security policy.

HIPAA and Mutual Authentication
The HIPAA Security Rule (45 CFR § 164.312) requires access controls and audit controls for electronic protected health information (ePHI). While HIPAA doesn't mandate specific authentication technologies, mTLS provides the strongest technical control for authenticating both users and systems accessing ePHI — particularly for API-based access between clinical systems.
The addressable specification for person or entity authentication (§ 164.312(d)) encourages organisations to implement authentication mechanisms proportionate to the risk. For inter-system communication carrying ePHI — between EHR systems, lab information systems, pharmacy systems, and health information exchanges — mTLS provides cryptographic proof of identity at the transport layer, satisfying the authentication requirement and providing the audit trail that HIPAA demands.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
The practical challenge is that HIPAA compliance must be demonstrated across the entire data flow, including break-glass scenarios. Any fallback authentication mechanism must maintain the same audit granularity as mTLS. A break-glass event that bypasses mTLS but doesn't log the authenticating identity at an equivalent level of assurance creates a HIPAA audit gap.
Shared Clinical Workstations and Certificate-Based Access
Healthcare's dominant device model is the shared workstation. Nursing stations, physician charting terminals, and clinical department PCs are used by multiple clinicians across shifts. This model is fundamentally hostile to user-bound client certificates.
A client certificate tied to a user (stored on a smart card or in a user profile) works when users log in to their own device. In a shared workstation environment, clinicians need to authenticate quickly — often in under 10 seconds between patient interactions. Smart card insertion and PIN entry adds friction that clinical workflow doesn't tolerate.
Approaches that work in healthcare shared environments include: proximity-based smart card readers (tap-in/tap-out with contactless smart cards), virtual smart card solutions where the certificate is stored in the network and presented after lightweight authentication (e.g., badge tap + PIN), device-level certificates for the workstation combined with user-level authentication at the application layer (reducing but not eliminating the mTLS benefit), and session management solutions that map a quick-authentication event to an existing mTLS session.
Each approach trades off between authentication strength, clinical workflow impact, and implementation complexity. The phased rollout from the core strategy is essential — pilot in a department with lower workflow pressure (administration, not emergency) before attempting clinical areas.
EHR Integration Patterns for Certificate Authentication
Electronic Health Record systems — Epic, Cerner (now Oracle Health), MEDITECH — are the central nervous system of clinical IT. EHR interoperability standards (HL7 FHIR, IHE profiles) increasingly support certificate-based authentication for API access.
SMART on FHIR, the dominant app authorisation framework for EHR systems, uses OAuth 2.0 — but the backend connection between application servers and EHR FHIR endpoints can be secured with mTLS for transport-level authentication. This is particularly relevant for system-to-system integrations: lab results flowing into the EHR, pharmacy systems checking drug interactions, and clinical decision support tools querying patient data.
The certificate management challenge is that EHR environments are typically managed by the EHR vendor or a dedicated EHR operations team, not by enterprise IT. Certificate deployment and renewal must integrate with EHR maintenance windows and change management processes that operate on different timelines than general infrastructure.
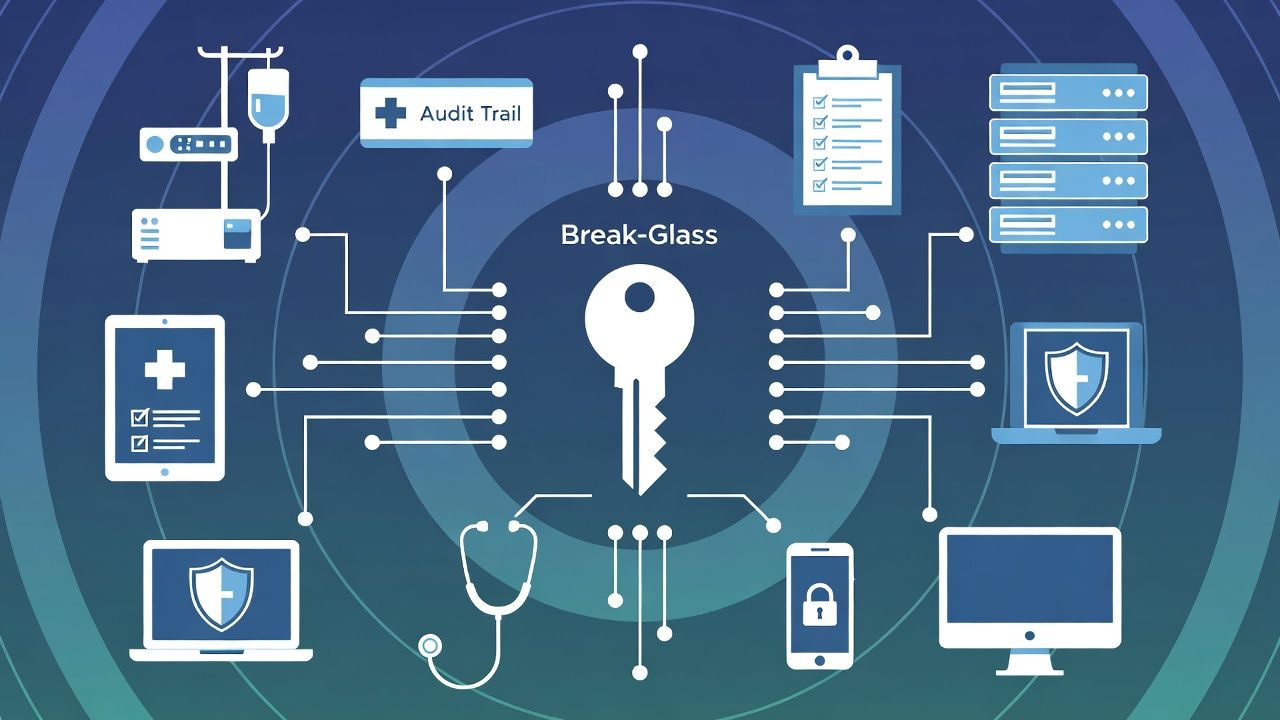
Break-Glass in Clinical Settings: Patient Safety Overrides Security
In general enterprise, break-glass is about business continuity. In healthcare, break-glass is about patient safety. This changes the design fundamentally.
A clinician who cannot authenticate to the medication administration system because their client certificate has expired is a patient safety risk. The break-glass decision must be immediate, must not require supervisor approval in real-time, and must never delay clinical care. Regulatory frameworks (Joint Commission standards, CMS Conditions of Participation) support this: patient care takes precedence.
Break-glass design for clinical mTLS should include: automatic fallback to secondary authentication (badge + PIN, biometric) without manual intervention, departmental emergency credentials that provide immediate access to clinical systems (audited, time-limited, reviewed post-event), clinical system-specific override mechanisms that EHR vendors provide for exactly this scenario, and post-event review processes that satisfy both HIPAA audit requirements and clinical quality assurance.
The key design principle: break-glass in healthcare should never require the clinician to think about IT infrastructure. If they're aware the authentication mechanism failed, the break-glass design has failed.
Related in this cluster: Certificate strategy hub · Private PKI · mTLS · M&A PKI · Multi-CA · Revocation · Certificate Transparency · CAA & DNS trust · Kubernetes TLS · Edge TLS · Code signing · Observability · SCEP / NDES sunset.