Private PKI Strategy for Financial Services
The core private PKI strategy covers when to run your own CA, the true cost of doing so, and the role of internal ACME. Everything there applies to financial services — and then regulatory requirements, multi-entity corporate structures, and audit obligations add layers that fundamentally change the strategic calculus.
Financial services organisations don't choose private PKI for operational convenience. They choose it because regulators effectively require it.
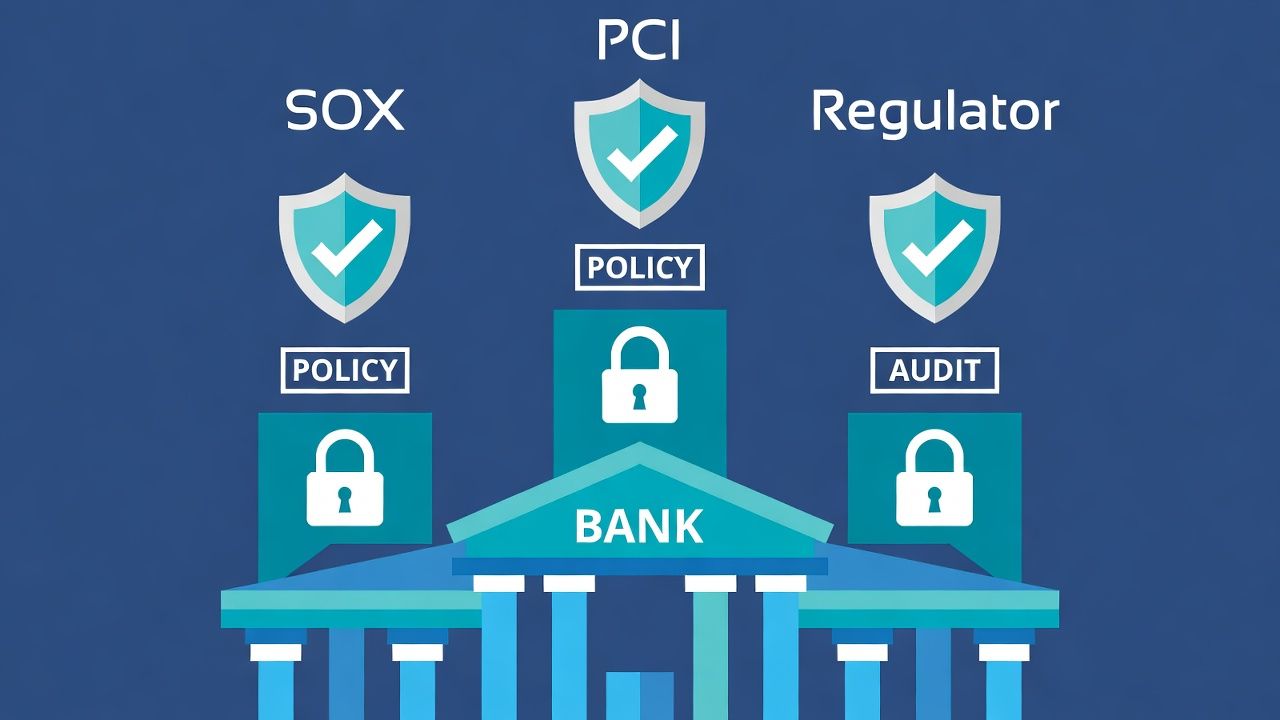
Regulatory Drivers: SOX, PCI DSS, FCA/PRA Expectations
SOX Section 404 internal controls extend to cryptographic key management. If your certificates protect systems involved in financial reporting — and in most financial institutions, the answer is "virtually all of them" — the key management practices behind those certificates are auditable. External auditors will ask: where are the CA keys stored, who has access, what are the key ceremony procedures, and where's the documentation?
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
PCI DSS applies to any system that processes, stores, or transmits cardholder data. The key management requirements in Section 3 (now v4.0) mandate specific controls for cryptographic keys: documented procedures, split knowledge and dual control, secure key storage, and defined cryptoperiods. For certificates protecting payment infrastructure, the private CA operating environment must meet PCI DSS key management standards.
The FCA and PRA in the UK — and equivalent regulators across jurisdictions — increasingly expect operational resilience documentation that covers certificate infrastructure. The FCA's operational resilience framework requires firms to identify important business services and set impact tolerances. If a certificate expiry can take down a customer-facing service (it can, and regularly does), certificate lifecycle management falls within the resilience scope.
None of these requirements mandate private PKI specifically. But meeting SOX, PCI, and regulatory audit requirements using a third-party public CA — where you have limited visibility into their key management practices and limited ability to demonstrate control — is substantially harder than meeting them with infrastructure you operate.
Multi-Entity Trust Architecture
Financial services groups rarely operate as a single legal entity. A holding company, retail banking subsidiary, investment banking arm, insurance entity, and asset management division may each be separate legal entities — often in different jurisdictions with different regulators.
Each entity may have different certificate requirements: different CAs mandated by local regulation, different compliance certifications, different key management obligations. A single enterprise root CA serving the entire group is operationally elegant but may not satisfy regulators who expect entity-specific controls.
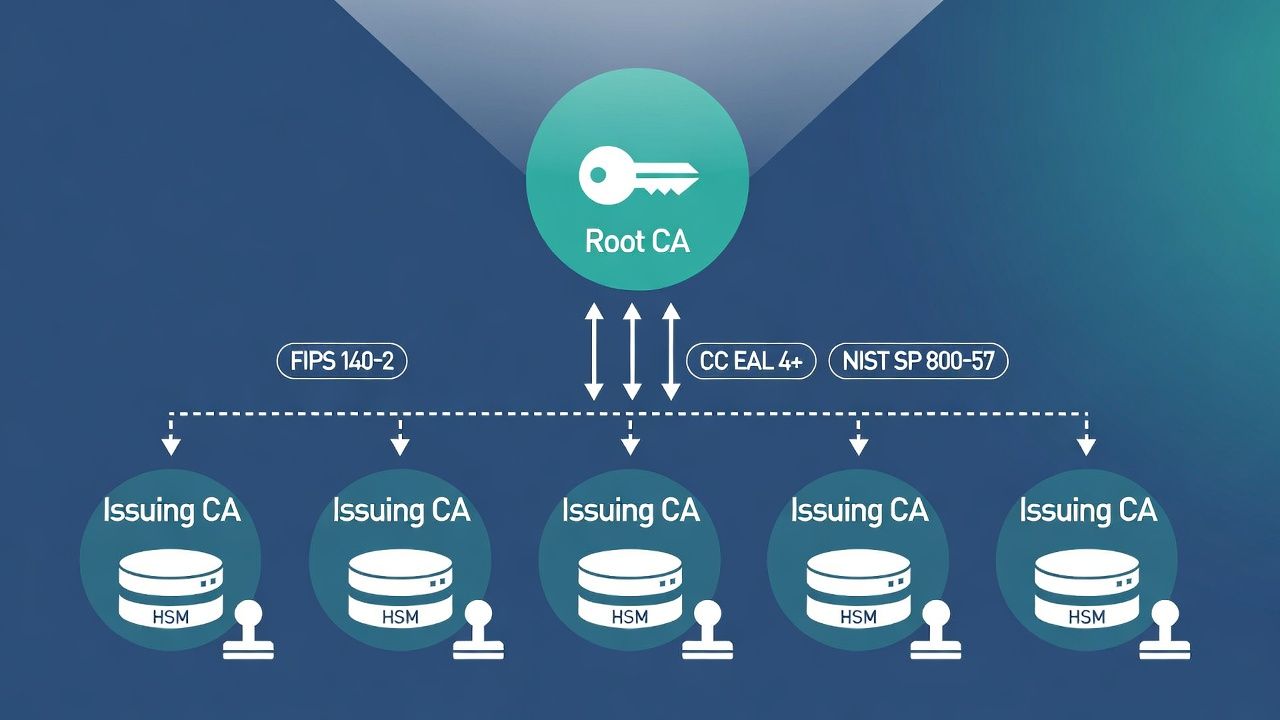
The trust hierarchy that addresses this uses a private root CA at the group level with subordinate issuing CAs per entity or per regulatory domain. The root CA key is ceremonially generated and stored offline in HSMs with group-level custodians. Issuing CAs inherit trust from the root but operate independently, with entity-specific policies, access controls, and audit trails.
This architecture satisfies entity-level regulatory requirements while maintaining a common trust anchor across the group. Cross-entity service communication works because all certificates chain to the same root. Entity-specific audit is possible because each issuing CA maintains separate logs.
The challenge is governance. Who controls the root CA? If it's the group IT function, entity-level regulators may question whether the entity has sufficient autonomy over its cryptographic infrastructure. If it's distributed, coordination complexity increases. The right answer depends on your regulatory landscape, but the architecture should be designed to satisfy the most demanding regulator in your portfolio.
HSM and Key Ceremony Requirements
In general enterprise, HSMs for private PKI are a best practice. In financial services, they're non-negotiable. Regulatory expectations — and audit firm expectations, which often exceed regulatory minimums — require hardware-protected key material for CA operations.
Key ceremonies in financial services require: formally documented procedures reviewed by compliance, multiple key custodians (typically 3-of-5 or similar threshold schemes), physical security controls and witness requirements, video recording in some jurisdictions, and comprehensive audit logs that are retained for the period mandated by your regulator (often 7+ years).
Cloud HSM services (AWS CloudHSM, Azure Dedicated HSM) can meet these requirements but introduce questions about data residency and third-party access that regulators may scrutinise. On-premises HSMs with FIPS 140-2 Level 3 or FIPS 140-3 certification remain the default in most financial services PKI deployments.
Audit Trail and Key Custodian Obligations
The audit trail for a financial services private CA extends beyond standard PKI logging. Every certificate issuance, revocation, key ceremony, policy change, and access event must be logged in a tamper-evident format. Audit trails must be available for internal audit, external audit (SOX, PCI QSA), and regulatory examination on demand.
Key custodian programmes require defined roles (custodian, backup custodian, ceremony witness), regular attestation that custodians still meet suitability requirements (background checks, employment status), and procedures for custodian replacement when individuals leave the organisation or change roles.
These obligations are operational overhead that the core private PKI cost analysis should account for when building the financial services business case.
Related in this cluster: Certificate strategy hub · Private PKI · mTLS · M&A PKI · Multi-CA · Revocation · Certificate Transparency · CAA & DNS trust · Kubernetes TLS · Edge TLS · Code signing · Observability · SCEP / NDES sunset.