mTLS & Client Certificate Strategy for Financial Services
The core mTLS strategy covers phased rollout, break-glass procedures, enrollment, and lifecycle management. Financial services takes mTLS from optional best practice to regulatory mandate — and the compliance context changes every operational dimension.
PSD2 and Open Banking: Mandated mTLS Between Institutions
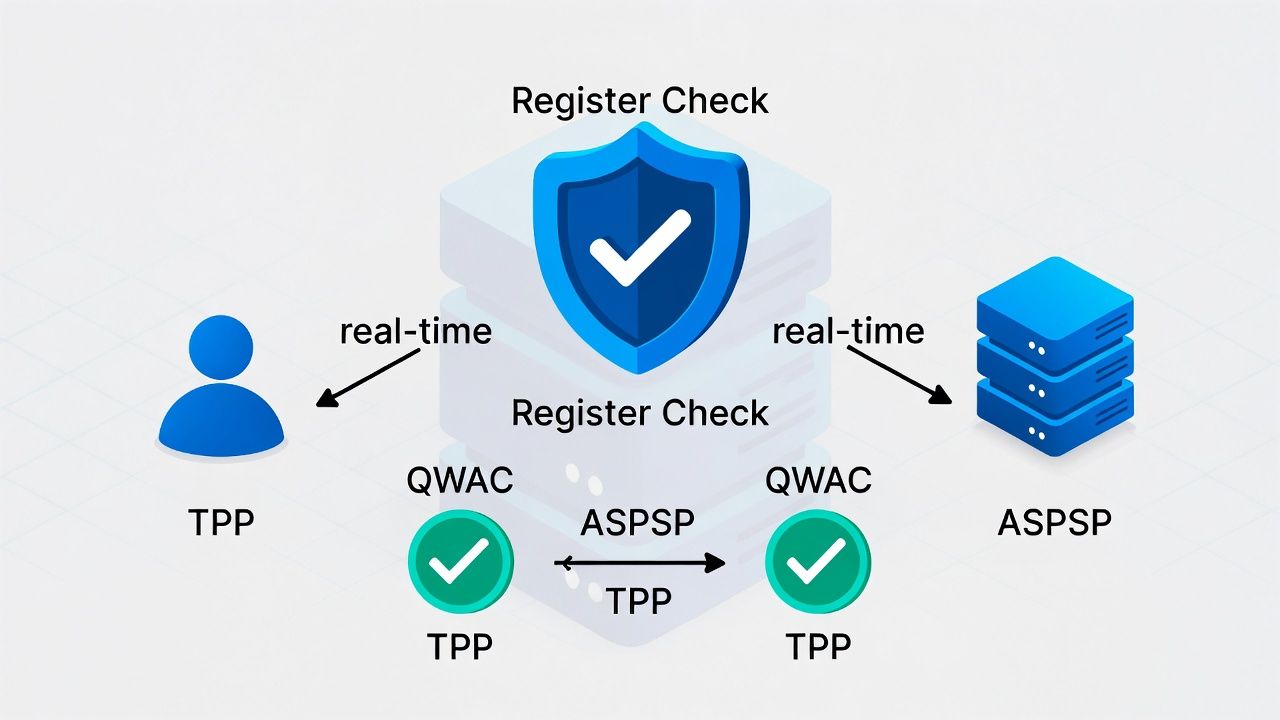
PSD2's Regulatory Technical Standards require mutual TLS for communication between Account Servicing Payment Service Providers (ASPSPs — typically banks) and Third Party Providers (TPPs — fintechs, payment initiators, account information services). This isn't a recommendation. It's law across the EU and UK.
The certificate requirements are specific. TPPs must present Qualified Website Authentication Certificates (QWACs) issued by Qualified Trust Service Providers (QTSPs) under the eIDAS regulation. These certificates include PSD2-specific fields: the TPP's authorisation number from their National Competent Authority, their PSD2 role (AIS, PIS, or both), and the name of their regulator.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
ASPSPs must validate these certificates in real-time — checking not just cryptographic validity but regulatory status. A valid eIDAS certificate from a TPP whose authorisation has been withdrawn should be rejected. This means your mTLS validation logic must integrate with NCA registers and the EBA's aggregated register, adding a regulatory data dependency to every TLS handshake.
For banks implementing PSD2 APIs, the mTLS architecture must handle: certificate validation against QTSP trust anchors (which are different from your standard trust store), extraction and verification of PSD2-specific certificate extensions, real-time authorisation status checking against regulatory registers, and audit logging sufficient for regulatory examination and dispute resolution.
Client Certificates for Trading and Settlement Platforms
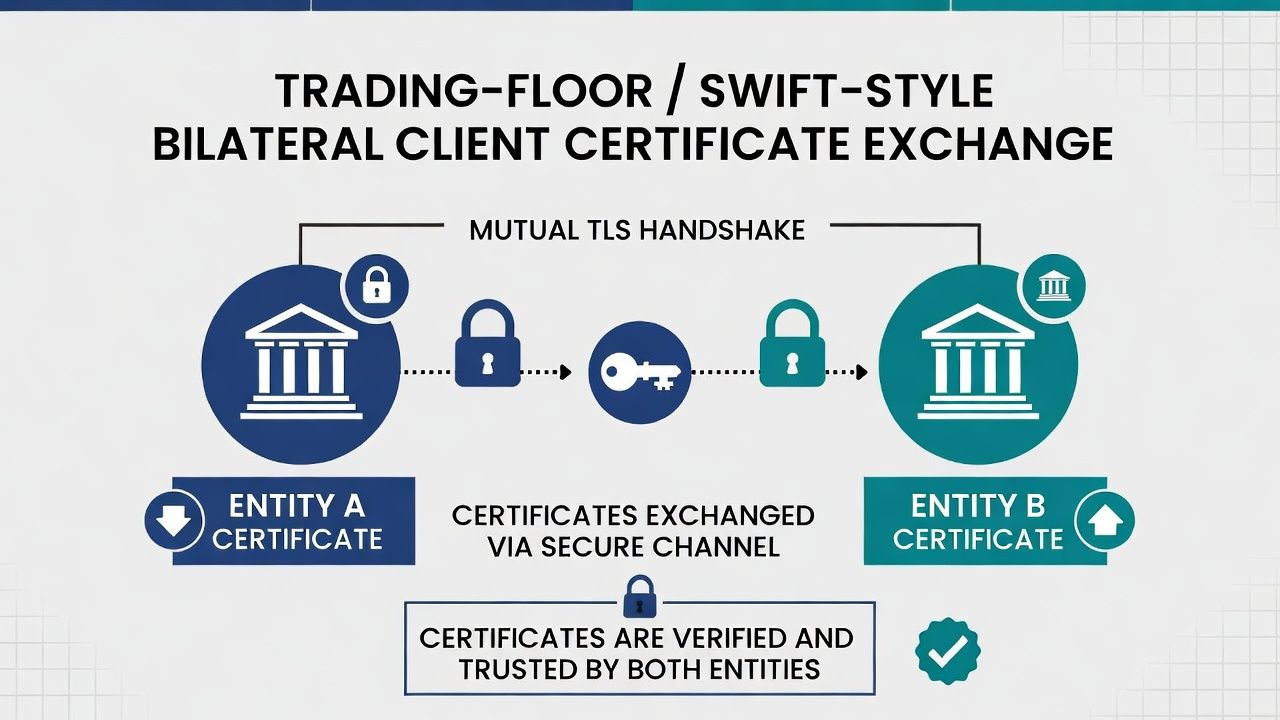
Institutional trading platforms, settlement systems (SWIFT connectivity, card network interfaces), and inter-bank communication channels increasingly require client certificate authentication. The trust model here is typically bilateral — each counterparty issues certificates from their own PKI, and trust is established through explicit cross-certification or trust anchor exchange.
SWIFT's Customer Security Programme includes requirements for securing operator sessions and API access. Card networks (Visa, Mastercard) require certificate-based authentication for certain integration patterns. Central counterparties and clearing houses are moving toward certificate-based identity for member connectivity.
For these use cases, certificate lifecycle coordination becomes a multi-party problem. Certificate renewal, revocation, and trust anchor updates must be communicated to counterparties on defined timelines. A certificate that expires without coordinated renewal can disrupt settlement flows — which in financial services means regulatory exposure and potential financial penalties.
Regulatory Break-Glass: When Authentication Fails in Regulated Operations
The core break-glass framework covers general principles. In financial services, break-glass has regulatory dimensions.
If mTLS enforcement prevents access to a system that processes payments, the break-glass event itself may trigger regulatory notification requirements. The FCA's operational resilience framework expects firms to report material operational incidents. A certificate failure that disrupts customer-facing payment services for more than a defined threshold (typically 2-4 hours, depending on the service) may constitute a reportable incident.
Break-glass procedures for regulated systems must include: a regulatory impact assessment (does this break-glass event trigger notification requirements?), timestamped documentation of the event, root cause, and resolution, and post-incident review with compliance sign-off.
The break-glass mechanism itself must be designed to maintain audit continuity. Fallback authentication (MFA, token-based) must produce an audit trail that meets the same regulatory standard as certificate-based authentication. A gap in the audit trail during break-glass is a compliance finding.
Certificate Lifecycle for Third-Party Provider Connections
Managing certificates for TPP connections at scale requires automation that accounts for the regulatory dimension. eIDAS certificates have defined validity periods (typically 1-2 years for QWACs). TPPs are responsible for renewal, but ASPSPs need processes to handle the transition — accepting both old and new certificates during a rollover window, removing expired trust anchors, and maintaining a current inventory of which TPPs are connected with which certificates.
When a TPP's regulatory authorisation is withdrawn, the ASPSP must cease accepting connections from that TPP regardless of certificate validity. This requires integration between your certificate validation pipeline and regulatory register monitoring — a coupling that standard TLS infrastructure doesn't provide out of the box.
Related in this cluster: Certificate strategy hub · Private PKI · mTLS · M&A PKI · Multi-CA · Revocation · Certificate Transparency · CAA & DNS trust · Kubernetes TLS · Edge TLS · Code signing · Observability · SCEP / NDES sunset.