M&A PKI Strategy for Financial Services
The core M&A PKI playbook covers due diligence, acquisition integration phases, and divestiture carve-outs. Financial services M&A adds regulatory approval timelines, ring-fencing requirements, and payment system certificate dependencies that fundamentally reshape the integration timeline and constraints.

Regulatory Approval Timelines and PKI Integration Sequencing
Financial services acquisitions require regulatory approval from one or more prudential regulators — the PRA and FCA in the UK, OCC and FDIC in the US, ECB for significant eurozone institutions. Approval timelines range from 3 months to over a year. During this period, the two entities must operate independently — including their PKI infrastructure.
This creates a sequencing constraint: PKI integration cannot begin until regulatory close. The cross-trust phase from the core playbook effectively cannot start until day one post-close, compressing the integration timeline. For financial services acquisitions, plan for 18-30 months post-close for full PKI rationalisation, versus the 12-24 months in general enterprise.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Pre-close, due diligence can still capture the PKI inventory and identify integration challenges. Post-close, the cross-trust phase should be prioritised alongside Day 1 operational integration — employees from the acquired entity need access to the acquirer's systems, and certificate-based authentication failures will block that access.
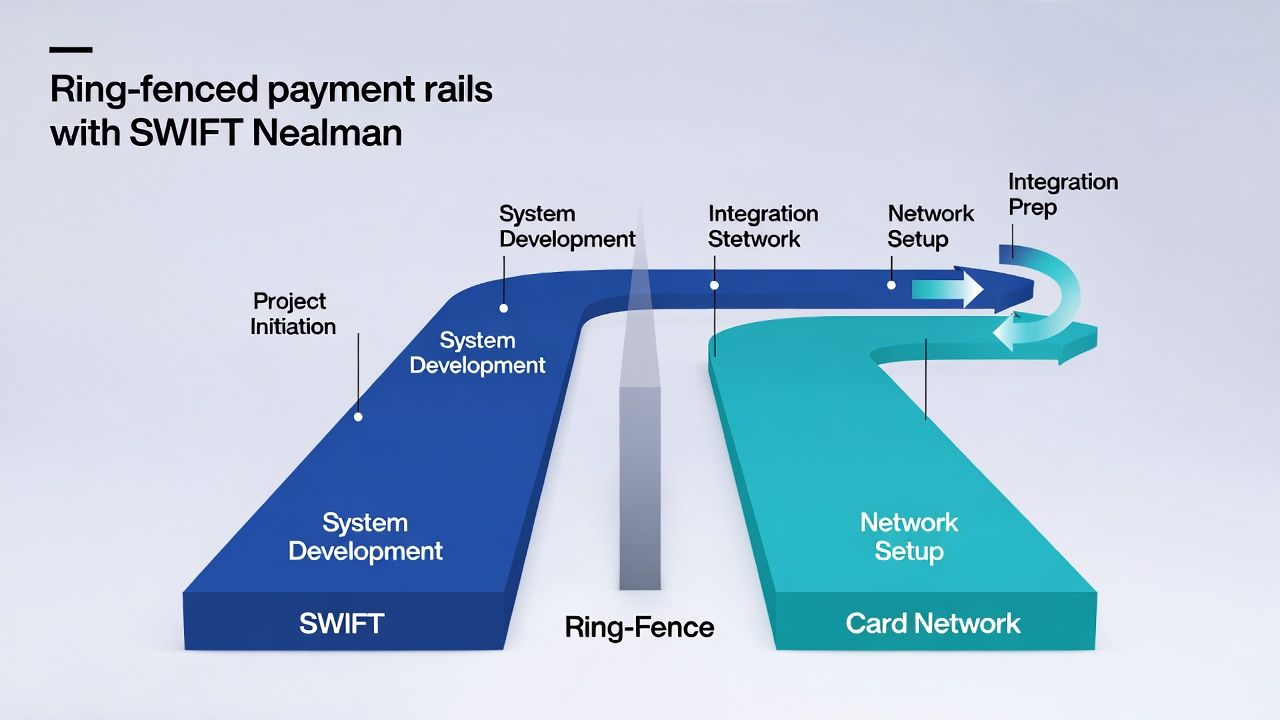
Ring-Fenced Entity Certificate Separation
UK ring-fencing regulations (and similar structural separation requirements in other jurisdictions) require that ring-fenced banks operate with a degree of operational independence from the wider group. This has direct PKI implications: the ring-fenced entity may need its own CA hierarchy, its own key management infrastructure, and demonstrable independence in its certificate operations.
A shared enterprise root CA serving both ring-fenced and non-ring-fenced entities may satisfy regulators if the operational separation is documented and enforced. But some regulators may require separate root CAs for ring-fenced entities — which means separate trust anchors, separate key ceremonies, and separate operational teams. This is a regulatory conversation that should happen early, not during integration.
Payment System Certificate Migration
Payment system connections — SWIFT, card network interfaces (Visa, Mastercard), clearing house connectivity, CHAPS/BACS in the UK, ACH/Fedwire in the US — use certificates that are tightly coupled to the legal entity and its membership credentials.
These certificates cannot simply be re-issued. Migration requires coordinating with the payment scheme operator, updating membership records, and testing connectivity — often within defined maintenance windows. SWIFT connectivity changes, for example, require advance notification and testing with SWIFT's infrastructure.
The M&A PKI integration plan must identify all payment system certificate dependencies during due diligence and build separate migration workstreams for each. These workstreams operate on the payment scheme's timeline, not yours.
Due Diligence Checklist: PKI-Specific Items for Financial Acquisitions
In addition to the general PKI due diligence questions, financial services acquisitions should assess: regulatory-mandated PKI controls (which regulators have specific requirements, and are they being met?), ring-fencing or structural separation PKI implications, payment system certificate inventory and migration dependencies, PSD2/open banking certificate infrastructure (QWAC/QSealC management), HSM fleet inventory and FIPS certification status, key custodian programme and personnel, and outstanding regulatory findings or remediation programmes that affect PKI.
Related in this cluster: Certificate strategy hub · Private PKI · mTLS · M&A PKI · Multi-CA · Revocation · Certificate Transparency · CAA & DNS trust · Kubernetes TLS · Edge TLS · Code signing · Observability · SCEP / NDES sunset.