Certificate Strategy: The Framework Most Organisations Skip
Certificates are decisions that compound. Every certificate you issue creates a dependency — on a CA, a key management practice, a renewal process, a trust anchor, and an operational workflow that someone has to maintain. One certificate is trivial. Ten thousand certificates, issued by three CAs, across four cloud providers, managed by six teams with different tooling, is a strategic problem.
Most organisations don't have a certificate strategy. They have a certificate habit. Somebody picked a CA years ago, somebody else configured auto-renewal on a few domains, a third person built a spreadsheet to track the ones that keep expiring. The result isn't a strategy — it's an accumulation of tactical decisions made under pressure, each one reasonable in isolation, collectively forming an architecture that nobody designed and nobody fully understands.
The CA/Browser Forum's April 2025 approval of Ballot SC-081v3 made this gap impossible to ignore. Public TLS certificate lifetimes are dropping to 200 days in March 2026, 100 days in 2027, and 47 days by March 2029. An organisation managing 1,000 certificates will go from roughly 1,000 renewal events per year to over 8,000. That's not a tooling problem. That's a strategic inflection point.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Why Certificates Need a Strategy, Not Just a Tool
The certificate management vendor pitch is straightforward: buy our platform, discover your certificates, automate renewals, avoid outages. It's a reasonable pitch. It's also incomplete.
A tool handles the mechanics. A strategy handles the decisions that determine whether those mechanics work at scale. Which CAs do you use, and what happens when one of them is distrusted — as Entrust was by Chrome, Apple, and Mozilla in late 2024? Who holds your private keys when TLS terminates at a CDN edge? What's your revocation posture for code signing versus web-facing TLS versus internal service mesh? How does your PKI integrate when you acquire another company, or divest a business unit?
These aren't operational questions. They're architectural decisions with multi-year consequences, and they intersect in ways that no single tool can resolve. A certificate strategy is the framework that connects them.
The organisations that get this right share a common trait: they treat certificates as infrastructure, not as IT tickets. Certificate management becomes a platform engineering discipline — with defined owners, SLOs, observability, and a roadmap. The organisations that get it wrong discover their gaps during incidents, audit findings, or the kind of fire drill that Entrust customers experienced in the second half of 2024.
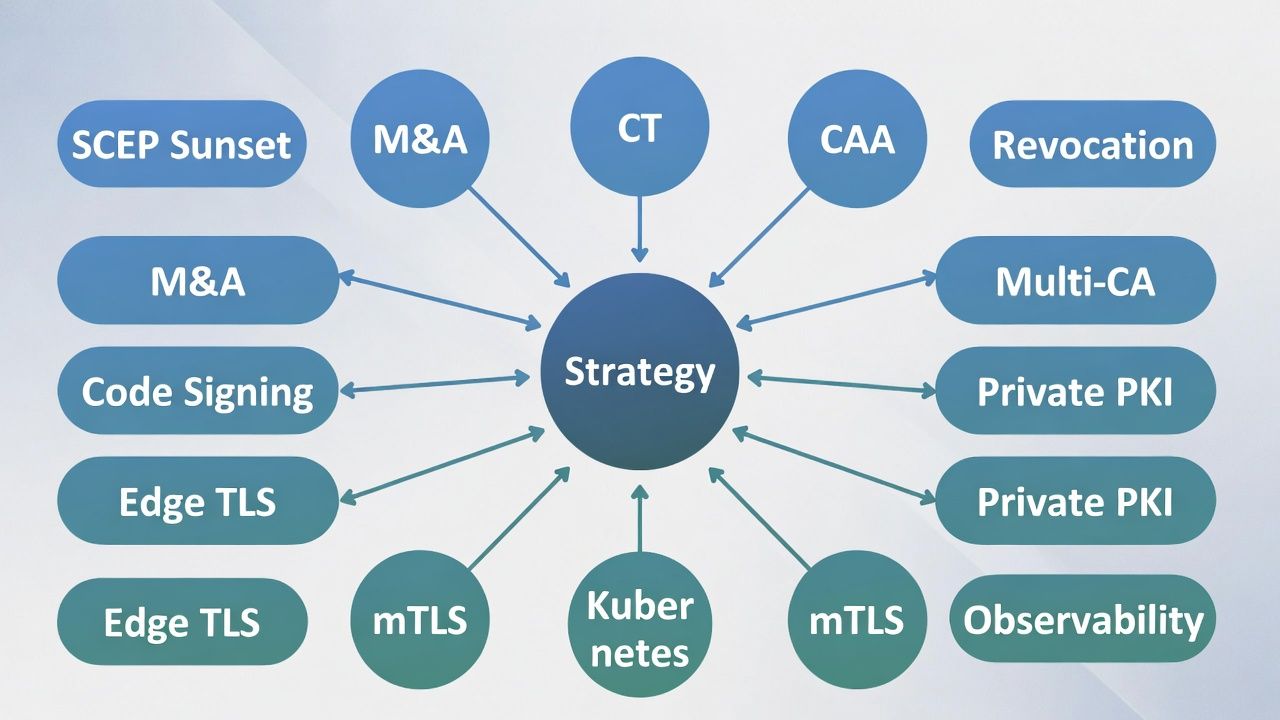
The 12 Dimensions of Certificate Strategy
Certificate strategy isn't a single decision. It's a set of interconnected decisions across trust, operations, deployment, and governance. Each dimension below represents a strategic surface area that most organisations discover reactively. Together, they form a complete framework.
Trust and Verification
Certificate Transparency and Mis-Issuance Detection — CT logs are public audit trails for certificate issuance. The strategic question isn't whether you publish to them — every public CA does — but whether you'd know within minutes if someone mis-issued a certificate for your domain. Most organisations treat CT as a compliance checkbox. The ones that treat it as a detection surface find problems before their customers do.
CAA and DNS Chain of Trust — Certificate Authority Authorization records let you specify which CAs can issue for your domains. Only around 16% of the top websites use them, despite CAA being mandatory for CAs to check since 2017. The deeper strategic conversation is about DNS itself: your certificate security is only as strong as your DNS security, and most organisations treat DNS as plumbing rather than infrastructure.
Revocation Strategy — Revocation is largely theatre for web-facing TLS. Browsers soft-fail on OCSP. Let's Encrypt shut down its OCSP service in 2025, and the CA/Browser Forum made OCSP optional in 2023. The strategic question is whether to invest in revocation infrastructure or make certificates short-lived enough that revocation becomes irrelevant. The answer depends entirely on certificate type.
Operational Resilience
Multi-CA and Issuer Redundancy — Single-CA dependency is a supply chain risk that organisations ignore until distrust day. The Entrust distrust in 2024 forced enterprises to emergency-migrate thousands of certificates. Multi-CA isn't "buy two vendors" — without policy-driven routing, you just have two messes instead of one.
Private PKI and Internal ACME — The decision to run your own certificate authority is the line between organisations that understand certificate management and those that are simply reacting to expiry alerts. Internal ACME brings public-CA automation patterns inside the perimeter. The build-vs-buy framing is too simple; the real question is what you need to control versus what you should delegate.
Certificate Observability and Operational SLOs — The industry's definition of certificate monitoring is "alert before expiry." That's one metric. A mature certificate operation tracks issuance failure rates, policy drift, configuration consistency, renewal velocity, and CA SLA adherence. You can't manage what you only measure when it breaks.
Platform and Deployment
Kubernetes and Platform TLS Strategy — cert-manager is not a certificate strategy. It's a tool. The strategic decisions sit above it: what issues certificates for ingress versus mesh? Who owns trust anchors? How do you maintain visibility across clusters when every team runs their own cert-manager instance? Kubernetes TLS is a platform engineering problem, not a certificate management problem.
Enterprise mTLS and Client Certificate Rollout — Mutual TLS is where zero trust meets operational reality. Every CISO wants it. Nobody wants the help desk calls when the CEO's client cert expires on Sunday. Failed mTLS projects don't fail on cryptography — they fail on UX and operational planning.
Edge TLS and Key Exposure — Every organisation that uses a CDN or cloud load balancer has handed their private keys to a third party. Most haven't considered what that means. The strategic question: where does TLS terminate, who holds the keys, and what's your exposure if that third party is compromised?
Lifecycle and Governance
Code Signing and Software Supply Chain — Code signing is the certificate use case where compromise has the highest blast radius. SolarWinds proved that. Yet most organisations treat code signing certificates identically to TLS certificates, without the governance, key protection, or audit trail the risk actually demands.
M&A and Divestiture PKI Integration — PKI in M&A is a massive blind spot. Trust anchors don't merge automatically. Internal CAs don't integrate themselves. Certificate-dependent applications don't discover their new trust hierarchy. This gets addressed at integration time, not due diligence time — and by then, the timeline is already compressed.
SCEP/NDES Legacy Enrollment Sunset — SCEP is a 20-year-old protocol that enterprises can't turn off because it's the only enrollment mechanism their MDM, network equipment, and legacy devices understand. The strategic question isn't whether to migrate — it's how to migrate when half your device estate doesn't support anything newer.
Strategy by Industry
These 12 dimensions apply universally, but the weight of each dimension shifts by industry. Regulatory environment, device estate, compliance requirements, and threat model all change the strategic calculus.
Financial services organisations face the heaviest regulatory friction. PSD2 mandates mutual TLS for open banking connections. SOX and PCI DSS impose specific key management controls. Multi-entity corporate structures create trust anchor hierarchy challenges that don't exist in single-entity companies. And financial services M&A — where regulatory approval timelines can stretch integration windows to 24 months — makes PKI integration planning essential, not optional.
Financial services deep dives: Private PKI, mTLS, M&A PKI.
Healthcare organisations contend with connected medical devices that may only support SCEP, clinical workstation models where certificates meet shift-based access patterns, and HIPAA requirements that touch key management and audit. Break-glass procedures in healthcare aren't about business continuity — they're about patient safety, which fundamentally changes the risk calculus for mTLS rollouts.
Healthcare deep dives: mTLS, SCEP / NDES, Private PKI.
Manufacturing and OT environments introduce constraints that enterprise IT rarely encounters: air-gapped networks, 15-to-25-year device lifetimes, plant shutdown windows as the only opportunity for certificate re-enrollment, and firmware signing requirements driven by the EU Cyber Resilience Act. IT/OT convergence means two PKI worlds colliding — and the OT side rarely has the automation infrastructure that IT takes for granted.
Manufacturing & OT deep dives: Private PKI, Firmware signing, SCEP / NDES, M&A PKI, Certificate observability.
The Automation Prerequisite
Every dimension of certificate strategy eventually leads to the same operational requirement: automation. Not because automation is fashionable, but because the maths no longer works without it. The shift to 47-day certificates means an 8× increase in renewal events. Multi-CA architectures require policy-driven routing that humans can't execute reliably at scale. Short-lived certificates for service mesh require issuance cycles measured in hours, not days.
But automation without strategy is just faster chaos. Automating certificate issuance across three CAs with no policy framework, no observability, and no understanding of your revocation posture doesn't solve the problem — it amplifies it. The Volume Paradox is real: successful automation increases your certificate count 5-10× rather than simply reducing costs. You need the strategy first.
How Axelspire Approaches Certificate Strategy
Axelspire exists because we've seen what happens when organisations treat certificates as an IT operations problem rather than an infrastructure architecture problem. We've managed PKI estates exceeding 100,000 certificates across financial services, telecommunications, and media organisations. The pattern is consistent: the invisible infrastructure tax — the hidden operational cost of certificate management — typically runs $4-6M annually in organisations that think they're spending a fraction of that.
Our approach is what we call Infrastructure Intelligence: not just managing certificates, but understanding the operational patterns, risk surfaces, and architectural decisions that determine whether a certificate estate is an asset or a liability.
The framework above isn't theoretical. It's the lens through which we assess every engagement, and the structure we use to help organisations move from reactive certificate management to strategic PKI operations.
If any of these 12 dimensions resonated as a gap in your organisation, start a conversation with us. Not a sales call — a strategy conversation.
Sector strategy briefs: FS — Private PKI · FS — mTLS · FS — M&A PKI · Healthcare — Private PKI · Healthcare — mTLS · Healthcare — SCEP / NDES · Mfg & OT — Private PKI · Mfg — Firmware signing · Mfg & OT — SCEP / NDES · Mfg — M&A PKI · Mfg & OT — Observability.
External References
- CA/Browser Forum Ballot SC-081v3: Schedule of Reducing Validity and Data Reuse Periods (April 2025) — cabforum.org
- Google Chrome Entrust Certificate Distrust Announcement (June 2024) — security.googleblog.com
- Let's Encrypt OCSP End of Life and Static CT API Migration — letsencrypt.org
- CNCF Annual Survey 2025: Cloud-Native Technology Adoption — cncf.io
- Certificate Transparency Project — certificate.transparency.dev
