HashiCorp Vault PKI: Operations, Cost & Compliance Assessment
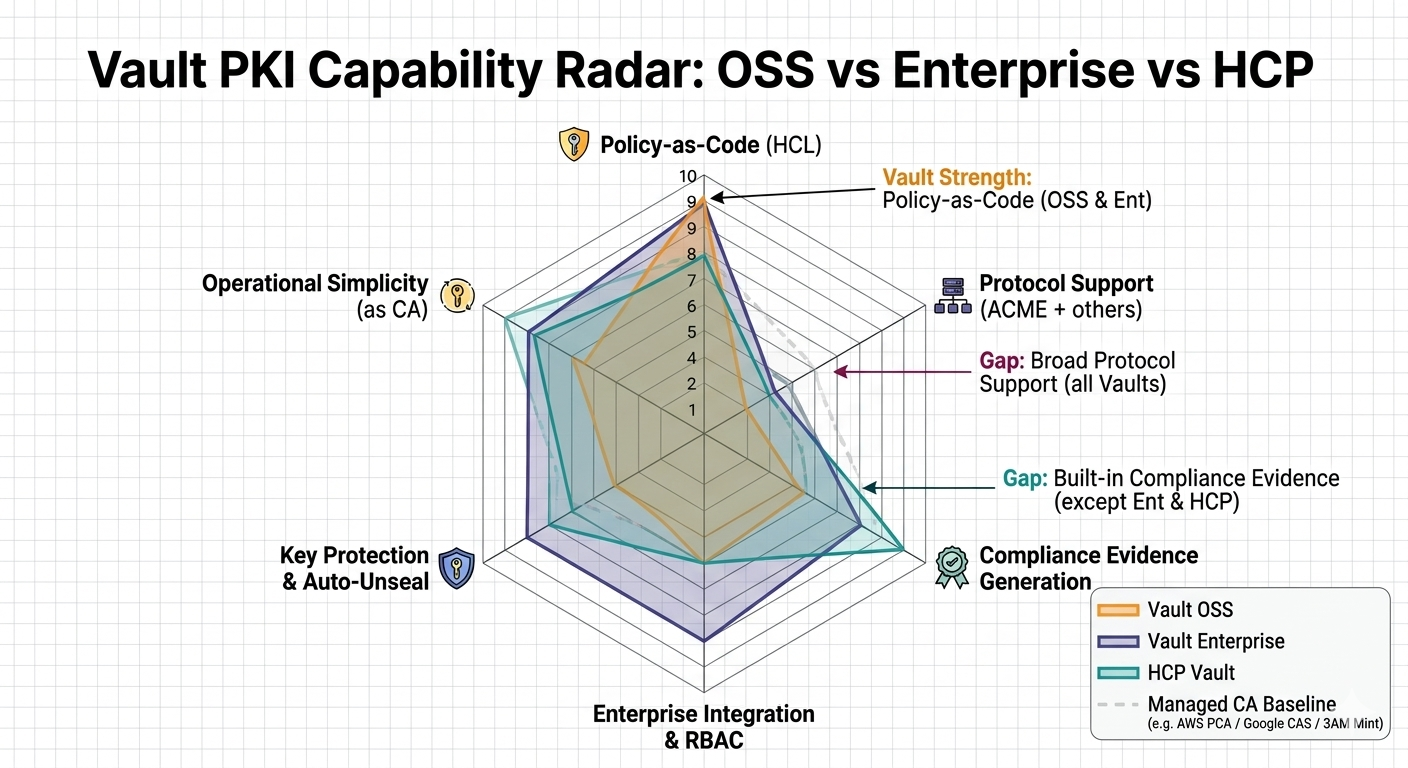
HashiCorp Vault's PKI secrets engine turns Vault into a certificate authority. For organisations already running Vault as their secrets management platform, adding PKI issuance is incremental — same operations team, same infrastructure, same policy language.
The critical framing: Vault PKI is a CA feature within Vault, not a PKI platform. It issues certificates. It does not provide cross-CA inventory, certificate discovery, enterprise lifecycle dashboards, or multi-CA policy management. Organisations that need those capabilities must layer them on top — or use a platform like 3AM that provides them natively.
For the cross-platform evaluation, see the Private CA Platform Comparison.
What Vault PKI does well
Vault-native issuance. If Vault is already the authentication and secrets layer, PKI issuance slots naturally into existing Vault policy, audit, and access control. Applications request certificates the same way they request database credentials — API call, policy-bound, TTL-controlled.
Policy-as-code. Vault's HCL policy language controls who can issue what certificates, with what SANs, for what TTLs. Auditable, version-controlled, and reviewable — a genuine security advantage over template-based CA systems.
cert-manager integration. The Vault issuer for cert-manager is mature and well-documented. Kubernetes clusters already using Vault for secrets can add certificate issuance through cert-manager without introducing a new CA product.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Operational complexity: Vault operations are PKI operations
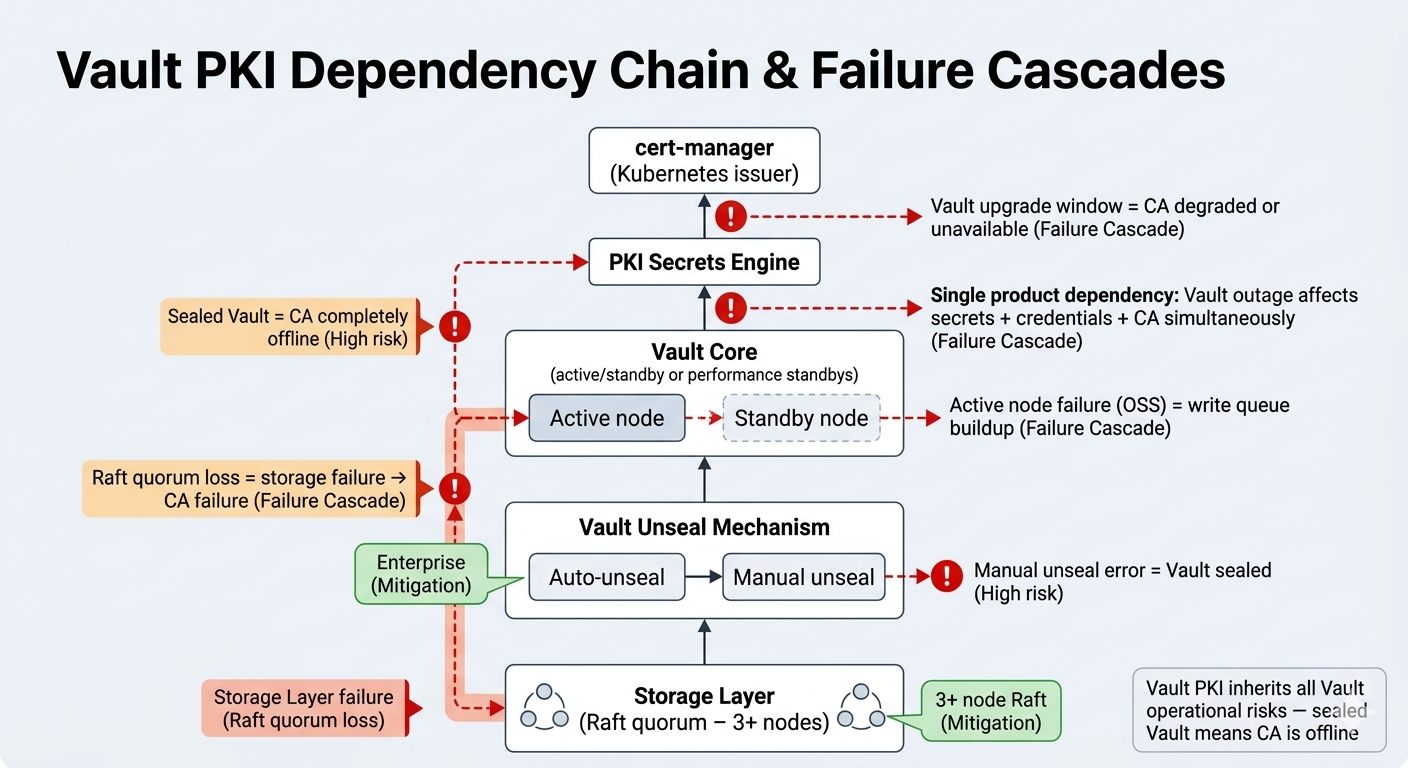
Vault PKI does not have its own operational profile — it inherits Vault's entirely:
| Vault operation | CA impact | Mitigation |
|---|---|---|
| Seal/unseal | Sealed Vault = CA offline | Auto-unseal (Enterprise only for HSM) |
| Storage (Raft quorum loss) | Storage failure = CA failure | 3+ node Raft cluster |
| Active/standby (OSS) | All writes to single active node — burst issuance queues | Enterprise performance standbys |
| Upgrades | CA unavailable or degraded during upgrade window | Careful change management |
| Single product dependency | Vault incident = secrets + DB credentials + CA all offline simultaneously | No mitigation — inherent risk |
Licensing reality: BSL transition
HashiCorp's move to the Business Source License (BSL) affects Vault. OpenBao forked from the last MPL-licensed version and is maintained by the Linux Foundation. Organisations must evaluate whether BSL terms are compatible with their use case, or factor in Enterprise licensing costs. This is an evolving landscape that adds procurement complexity — consult your legal team before committing to long-term Vault PKI deployments.
Cost model
| Scenario | 5-year TCO | Key cost driver |
|---|---|---|
| Already running Vault (OSS) | $50K–$200K incremental | 0.25–0.5 FTE PKI overhead |
| New Vault deployment for PKI | $300K–$800K | Vault infra + full staffing |
| Vault Enterprise (for PKI) | $500K–$1.5M+ | Per-node Enterprise licensing |
Deploying Vault solely for PKI is difficult to justify — the cost and complexity exceed lighter CA alternatives. Vault PKI is rational only for organisations already invested in the Vault ecosystem.
Security posture and ACME maturity
Key protection: CA keys stored in Vault's encrypted storage. Enterprise supports auto-unseal with HSM/cloud KMS and managed keys (1.10+) for external KMS. OSS stores keys in Vault's barrier — the key exists in software within Vault's process memory during operations.
ACME maturity: Vault added ACME support in version 1.14. HTTP-01 and DNS-01 challenges supported; TLS-ALPN-01 is not. ACME implementation is newer and less battle-tested than step-ca's or EJBCA's — factor this into production readiness assessments.
Compliance and audit
Vault's audit backend logs every request and response (file, syslog, socket). Evidence assembly is manual — Vault audit logs capture what happened but producing framework-specific evidence packages requires extraction, filtering, and formatting through SIEM or GRC integration. No built-in compliance reports. Self-managed Vault has no cloud provider compliance inheritance; HCP Vault's SOC 2 covers HashiCorp Cloud Platform, not customer-hosted deployments.
When Vault PKI fits — and doesn't
Choose Vault PKI when Vault is already the secrets management platform, issuance is API-driven (not protocol-diverse), and the Kubernetes cert-manager + Vault issuer path is natural.
Don't choose Vault PKI as a standalone CA for organisations not already invested in Vault — step-ca or AWS Private CA have significantly lower operational entry points for teams that just need a working CA. Don't use it when broad protocol support (SCEP, EST, CMP, CEP/CES) is needed — EJBCA Enterprise is the protocol-complete option. Don't deploy it when cross-CA inventory and lifecycle management are requirements.
Pair Vault PKI with 3AM Mint when Vault handles issuance but the organisation needs enterprise visibility across all CA backends, unified policy enforcement, and compliance audit trails with business context. 3AM Mint provides the enterprise integration layer Vault PKI intentionally leaves to the operator.
Private CA Platform Comparison — step-ca (lighter OSS alternative) — EJBCA (protocol-complete alternative) — AWS Private CA (managed alternative) — 3AM Mint (enterprise integration layer). Contact Axelspire or Ask Axel.
