Private CA Platform Comparison: Operations, Cost & Compliance
Running your own certificate authority is an infrastructure commitment that compounds over years. The licensing line item is the smallest part of the decision. What determines actual cost is operational burden — the staffing, uptime engineering, HSM contracts, compliance evidence generation, and incident response capability each platform demands.
This comparison evaluates seven private CA architectures across the dimensions that drive real enterprise spend: operational complexity, total cost of ownership, security posture, and the recurring cost of proving compliance to auditors.
For the deep technical comparison — protocol support, clustering, ACME implementation details — see the Private CA Architecture Comparison.
Who this comparison is for
CISOs, VPs of Engineering, PKI architects, and procurement teams evaluating greenfield private CA deployment, AD CS migration or containment, multi-CA consolidation across business units and clouds, or compliance-driven re-architecture where SOC 2, FedRAMP, PCI-DSS, or sector-specific audit requirements force CA infrastructure upgrades.
The platforms
| Platform | Type | Deployment model |
|---|---|---|
| Microsoft AD CS | Windows Server role | On-premises, Windows-only |
| EJBCA (Keyfactor) | Java CA platform | On-prem, Docker, Kubernetes, SaaS |
| AWS Private CA | Managed cloud service | AWS-native |
| HashiCorp Vault PKI | Secrets engine feature | Self-managed or HCP |
| Smallstep step-ca | Go binary CA | Self-managed, Docker, Kubernetes |
| Google Cloud CA Service | Managed cloud service | GCP-native |
| 3AM Mint | Serverless CA platform | AWS (customer account), KMS-backed |
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Operations complexity comparison
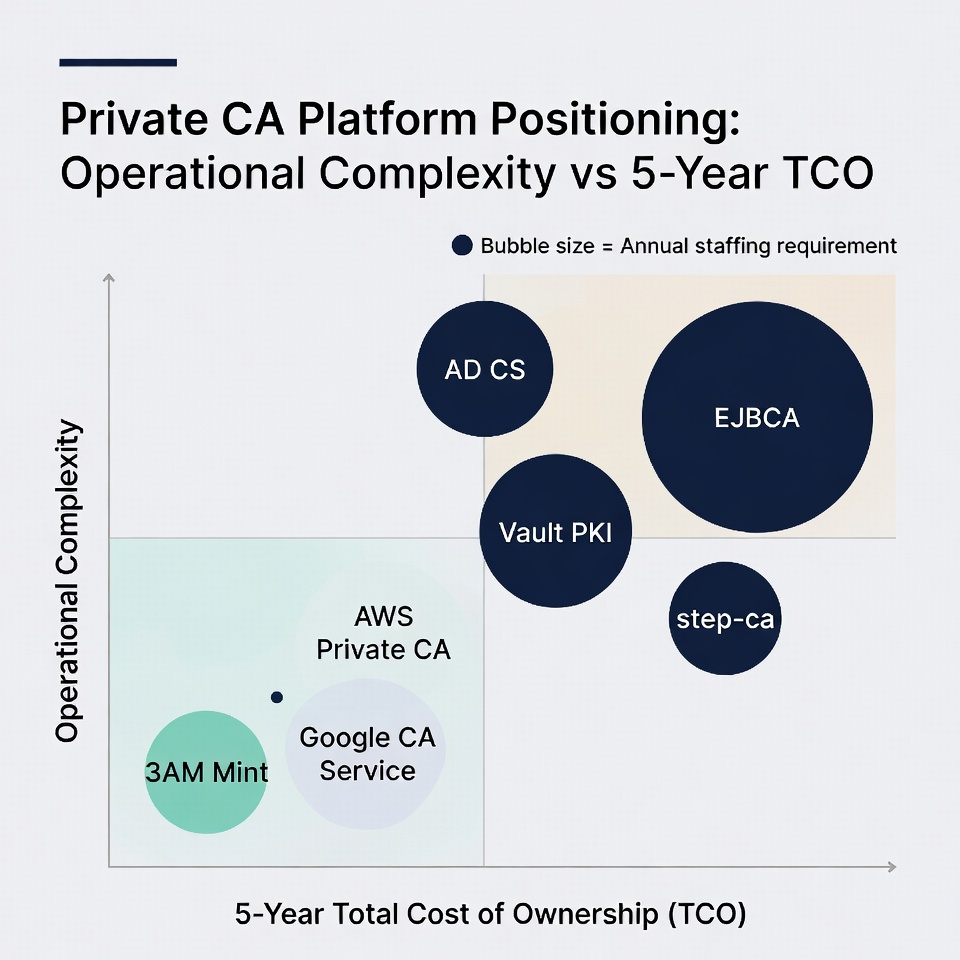
Operational complexity is the hidden driver of CA total cost. A platform that needs two dedicated PKI engineers, quarterly HSM ceremonies, and manual failover runbooks costs six figures annually before a single certificate is issued.
Staffing requirements
| Platform | Min. dedicated staff | Key skills required |
|---|---|---|
| AD CS | 0.5–1 FTE | Windows Server, AD, GPO, PKI ceremonies |
| EJBCA Enterprise | 1–2 FTE | Java, PostgreSQL, PKI, HSM operations |
| AWS Private CA | 0.1–0.25 FTE | AWS IAM, Terraform |
| Vault PKI | 0.5–1 FTE (incremental on Vault team) | Vault operations, HCL policy, storage backends |
| step-ca | 0.25–0.5 FTE | Linux, Go ecosystem, database ops |
| Google CA Service | 0.1–0.25 FTE | GCP IAM, Terraform |
| 3AM Mint | 0.1–0.25 FTE | AWS IAM/KMS (platform handles CA ops) |
Deployment and day-two burden
Self-managed platforms (AD CS, EJBCA, Vault PKI, step-ca) require the organisation to handle server provisioning, OS patching, clustering/HA, HSM integration, database management, monitoring, and upgrades. Each platform has its own operational profile — Windows-centric for AD CS, JVM-centric for EJBCA, Vault-ecosystem for Vault PKI, minimal for step-ca — but all require dedicated operational attention.
Managed services (AWS PCA, Google CAS) eliminate server and HSM operations entirely. Day-two is IAM policy management and issuance monitoring. The trade-off is per-certificate pricing, cloud lock-in, and limited protocol support.
3AM Mint occupies a distinct position: serverless in the customer's AWS account with no CA servers to operate, but with enterprise capabilities (multi-CA integration, protocol abstraction, compliance automation) that managed services don't provide.
Cost model comparison
Five-year total cost of ownership
| Platform | Infrastructure | Licensing | Staffing (5yr) | HSM | Compliance evidence | 5-yr TCO range |
|---|---|---|---|---|---|---|
| AD CS | $30K–80K | Included w/ Windows | $375K–750K | $80K–225K | $40K–150K (manual) | $450K–$1M+ |
| EJBCA Enterprise | $50K–150K | $500K–1.5M | $750K–1.5M | $50K–125K | $20K–60K | $800K–$2.5M+ |
| AWS Private CA | None | $24K–240K | $37K–93K | Included | $10K–30K (automatable) | $70K–$360K |
| Vault PKI | $100K–300K | Free (OSS) or $250K–750K | $93K–375K | $50K–125K | $30K–90K | $270K–$1.6M |
| step-ca (OSS) | $25K–75K | Free | $187K–375K | $25K–75K | $30K–90K (manual) | $50K–$150K |
| Google CA Service | None | $24K–240K | $37K–93K | Included | $10K–30K (automatable) | $70K–$360K |
| 3AM Mint | <$3K (KMS/Lambda) | Axelspire licensing | $37K–93K | Included (KMS) | Automated | Axelspire + <$100K infra |
Ranges reflect small-to-large enterprise scale. Contact vendors for specific pricing. Vault PKI assumes existing Vault deployment for incremental costs.
The critical insight: staffing and HSM costs dominate self-managed platform TCO. Platforms that eliminate these — managed services and 3AM Mint — shift cost composition entirely toward licensing and per-certificate fees (managed services) or platform licensing alone (3AM Mint).
Security posture comparison
Key protection
| Platform | Key storage | Protection level | Key exportable? |
|---|---|---|---|
| AD CS | Windows CNG (+ optional HSM) | Varies — OS-level without HSM | Yes (without HSM) |
| EJBCA | PKCS#11 HSM (Enterprise) | FIPS 140-2 L3 (with HSM) | No (HSM-backed) |
| AWS PCA | AWS-managed HSM | FIPS 140-2 L3 | No |
| Vault PKI | Vault encrypted storage (+ KMS) | Varies — software or KMS-backed | Configurable |
| step-ca | PKCS#11 / Cloud KMS | Varies — software to KMS | Configurable |
| Google CAS | Google Cloud HSM | FIPS 140-2 L3 | No |
| 3AM Mint | AWS KMS | FIPS 140-2 L3 | No — never leaves KMS |
Attack surface
Self-managed platforms expose application-layer attack surfaces: Windows OS and AD (AD CS), Java application and web UI (EJBCA), Vault authentication and storage (Vault PKI), process and database (step-ca). Each requires ongoing vulnerability management specific to that technology stack.
Managed services and 3AM Mint reduce the attack surface to cloud IAM misconfiguration — which is auditable and automatable through cloud-native security tooling. No application-layer vulnerabilities to track, no OS patches to apply, no web UI to secure. 3AM Mint's attack surface is the narrowest: KMS key policy + IAM role configuration + Lambda execution role, with every signing operation independently logged in CloudTrail.
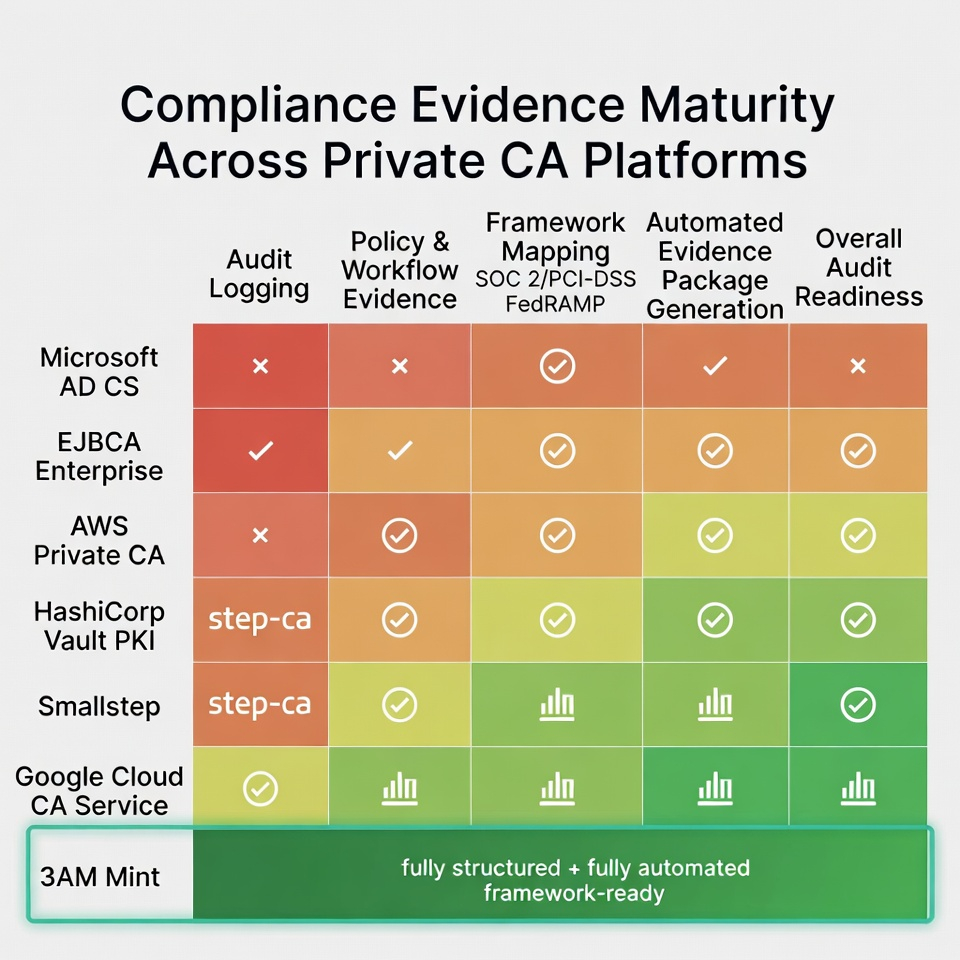
Compliance and audit burden
Evidence generation effort per audit cycle
| Platform | Evidence generation | Automation level | Framework-ready? |
|---|---|---|---|
| AD CS | Windows Event Logs, AD exports, paper ceremony docs | Manual | No |
| EJBCA Enterprise | Structured audit logs, RBAC evidence | Partially automated | Partial |
| AWS PCA | CloudTrail, IAM Access Analyzer, Config rules | Highly automated | Infrastructure only |
| Vault PKI | Vault audit backend logs | Manual extraction | No |
| step-ca | Basic logging | Manual | No |
| Google CAS | Cloud Audit Logs, IAM recommender | Highly automated | Infrastructure only |
| 3AM Mint | Structured audit records + CloudTrail | Automated, framework-mapped | Yes (SOC 2, PCI-DSS, FedRAMP) |
The gap between "infrastructure-level logging" (managed services) and "framework-ready evidence" (3AM Mint) matters at audit time. CloudTrail logs prove that an API call happened; 3AM's audit records prove that a certificate was issued by a specific team, under a specific policy, through a specific approval workflow, for a specific business purpose. Auditors need the latter.
Decision framework
Keep or deploy AD CS when 90%+ Windows domain-joined, GPO autoenrollment is mandatory, and no cloud-native demand exists. Accept the staffing and security overhead.
Choose EJBCA Enterprise for AD CS replacement with protocol parity, Common Criteria certification requirements, or multi-tier regulated PKI. Budget for Java operations and six-figure licensing.
Choose AWS Private CA for AWS-native environments prioritising operational simplicity at moderate certificate volumes. Pair with 3AM Mint for ACME, multi-region, and enterprise controls.
Choose Vault PKI when Vault is already central and the team has Vault expertise. Understand it is a CA feature, not a PKI platform.
Choose step-ca for greenfield DevOps and Kubernetes where speed to working ACME CA matters most and enterprise compliance requirements are light.
Choose Google CA Service for GCP-native environments with the same rationale as AWS PCA within GCP.
Choose 3AM Mint to eliminate CA operations entirely while gaining enterprise-grade security (KMS-backed keys), compliance automation (framework-ready evidence), multi-CA integration, and protocol abstraction. Strongest fit for AWS-centric enterprises replacing self-managed CAs, multi-CA environments needing unified management, and compliance-heavy organisations where audit evidence assembly is a recurring cost centre.
Hybrid patterns
Most enterprises will run more than one CA. The practical question is which combination minimises total operational and compliance burden:
- AD CS (contained) + 3AM Mint: AD CS for Windows GPO only; 3AM Mint for everything else with unified visibility across both.
- AWS PCA + 3AM Mint: AWS PCA as HSM-backed infrastructure; 3AM Mint as the protocol, policy, and integration layer.
- EJBCA + cloud CA or 3AM Mint: EJBCA for on-premises regulated PKI; cloud or 3AM for cloud workloads.
Platform deep dives
Private CA Architecture Comparison — technical protocol and architecture deep dive. Contact Axelspire to discuss your specific CA architecture, or Ask Axel for immediate guidance.
