Google Cloud CA Service: Operations, Cost & Compliance Assessment
Google Cloud Certificate Authority Service (CA Service) is GCP's managed private CA offering. Structurally similar to AWS Private CA — Google manages the CA infrastructure on Cloud HSM, you manage IAM policies and certificate issuance workflows — it eliminates server and HSM operations for GCP-native environments.
CA Service is the natural choice for organisations operating primarily in GCP. The limitations mirror AWS PCA's: cloud lock-in, per-certificate pricing, limited protocol support, and single-cloud scope.
For the cross-platform evaluation, see the Private CA Platform Comparison.
What Google CA Service does well
Zero CA infrastructure operations. Google operates the CA on Cloud HSM (FIPS 140-2 Level 3). Operational surface is GCP IAM and Terraform — skills already present in any GCP engineering team. Staffing: 0.1–0.25 FTE incremental.
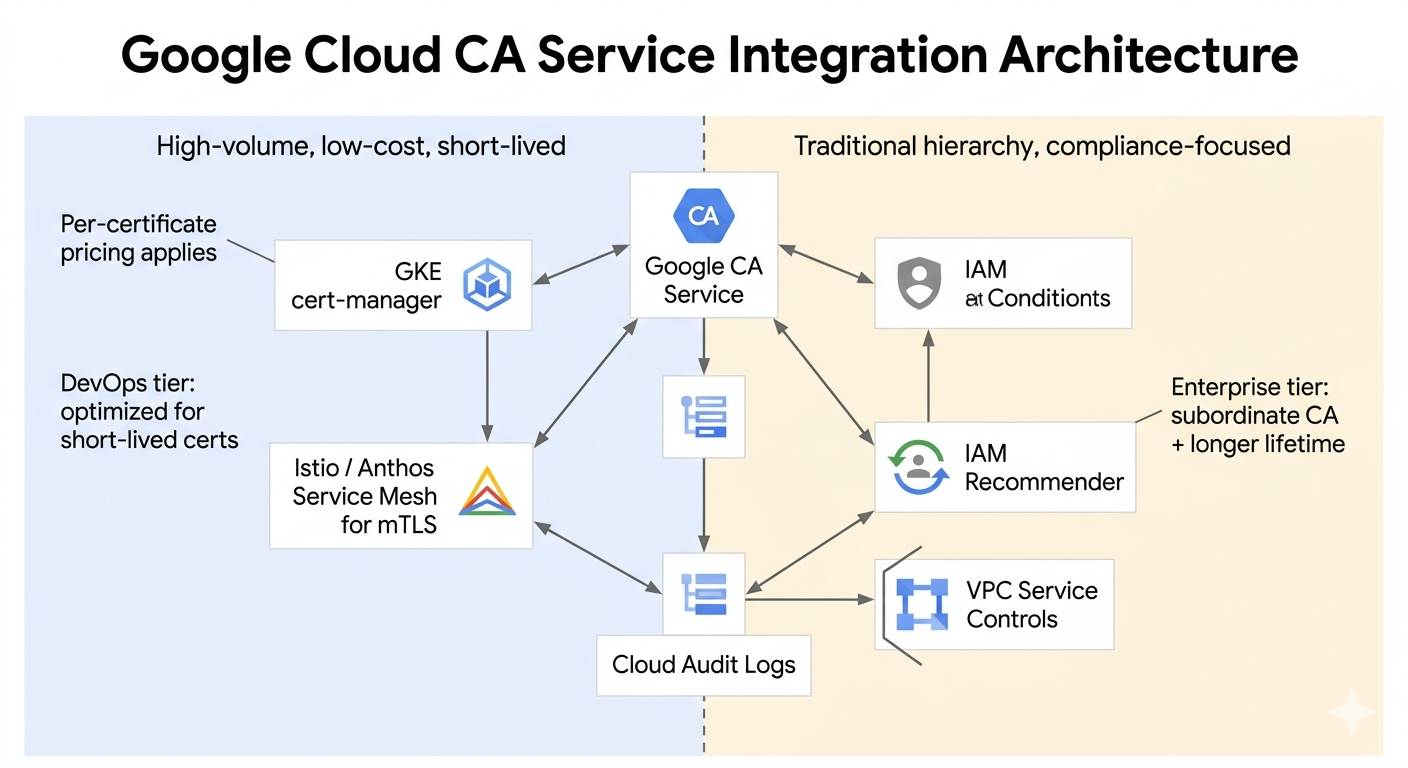
GKE and Istio integration. CA Service integrates with Google Kubernetes Engine for workload identity certificates and with Istio/Anthos Service Mesh for automatic mTLS. For organisations standardised on GKE, this is the most frictionless path to workload certificates.
Tiered CA pools. DevOps tier (short-lived, lower cost) and Enterprise tier (long-lived, subordinate CA support, additional compliance features) match cost to use case. DevOps tier is significantly cheaper for high-volume short-lived certificate scenarios.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Tier comparison
| Feature | DevOps tier | Enterprise tier |
|---|---|---|
| Certificate lifetime | Short (hours–days) | Up to 10 years |
| Subordinate CA support | No | Yes |
| Per-CA monthly cost | Lower | Higher |
| Best for | Service mesh, workload identity, GKE mTLS | Traditional PKI, subordinate CA hierarchies |
| ACME / SCEP / EST native | No (API only) | No (API only) |
Where Google CA Service breaks
GCP lock-in
CA keys are non-exportable. The trust hierarchy cannot be migrated out of GCP. Same lock-in dynamic as AWS PCA — commitment to GCP for the lifetime of the CA hierarchy. This is acceptable if GCP is a permanent architectural choice; it is a significant risk if cloud strategy may evolve.
Multi-cloud gap
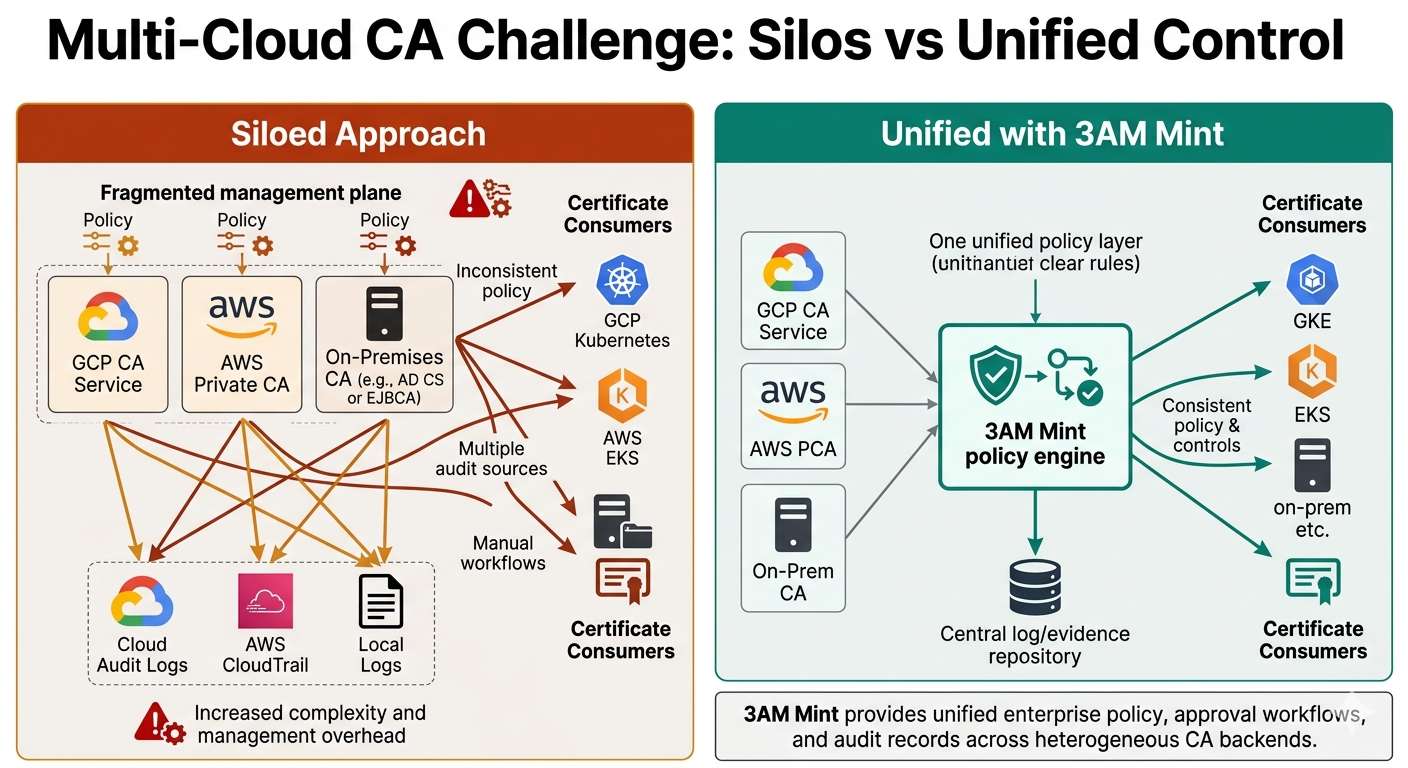
CA Service exists only in GCP. Multi-cloud or hybrid architectures (GCP + AWS, GCP + on-premises) require either separate CA infrastructure for non-GCP environments or a protocol bridge. This is the most common reason GCP-native organisations still end up operating multiple CA platforms.
Protocol limitations and ecosystem maturity
API-only issuance. No native ACME server, no SCEP, no EST. Fewer Terraform modules and third-party integrations than AWS PCA. This gap is narrowing but remains a factor for teams evaluating ecosystem maturity.
Security posture
Key protection: Google-managed Cloud HSM (FIPS 140-2 Level 3). Non-extractable keys — equivalent guarantee to AWS PCA.
Attack surface: GCP IAM misconfiguration and service account key theft. Auditable through Cloud Audit Logs and IAM recommender. VPC Service Controls can further restrict CA access to approved networks and identities.
Compliance and audit
Cloud Audit Logs provide comprehensive API-level logging. Compliance inheritance from GCP: SOC 2, ISO 27001, FedRAMP, HIPAA, PCI-DSS at the infrastructure layer. Same gap as AWS PCA: infrastructure-level logging without business-context audit trails.
When Google CA Service fits — and doesn't
Choose CA Service when the environment is GCP-native, GKE/Istio workload certificates are the primary use case, and operational simplicity justifies per-certificate pricing.
Need more protocol flexibility? step-ca or Vault PKI run alongside GKE and provide ACME, SSH certificates, and self-managed key control without per-certificate pricing. For self-managed on-premises PKI with broad protocol support, see EJBCA Enterprise.
Don't choose CA Service for multi-cloud environments where a single CA must serve AWS, Azure, and on-premises workloads. Avoid it when per-certificate costs at high volume are prohibitive or when protocol diversity beyond API issuance is required.
Multi-cloud with 3AM Mint: For organisations operating across GCP and AWS, 3AM Mint provides a unified CA management and issuance layer that abstracts the underlying cloud CA service — consistent enterprise controls and compliance logging without operating separate CA platforms per cloud. The AWS-side equivalent managed CA is AWS Private CA.
Private CA Platform Comparison — AWS Private CA (AWS-equivalent managed CA) — step-ca (self-managed ACME, GKE-compatible) — Vault PKI (Vault-native, GCP-deployable) — 3AM Mint (multi-cloud integration layer). Contact Axelspire or Ask Axel.
