EJBCA (Keyfactor): Operations, Cost & Compliance Assessment
EJBCA is the most feature-complete open-source-lineage CA platform available. Originally developed by PrimeKey (now Keyfactor), it has been in production since 2001, deployed in government PKI programmes, national identity systems, and enterprise environments that need broad protocol support with compliance certifications.
The critical distinction for procurement: EJBCA Community (LGPL) and EJBCA Enterprise (commercial) are materially different products. Keyfactor states Community is not intended for production deployment. Most capabilities that make EJBCA attractive for enterprise use — production clustering, HSM support, Common Criteria certification, advanced audit and role separation — are Enterprise-only.
For the cross-platform evaluation, see the Private CA Platform Comparison.
What EJBCA does well
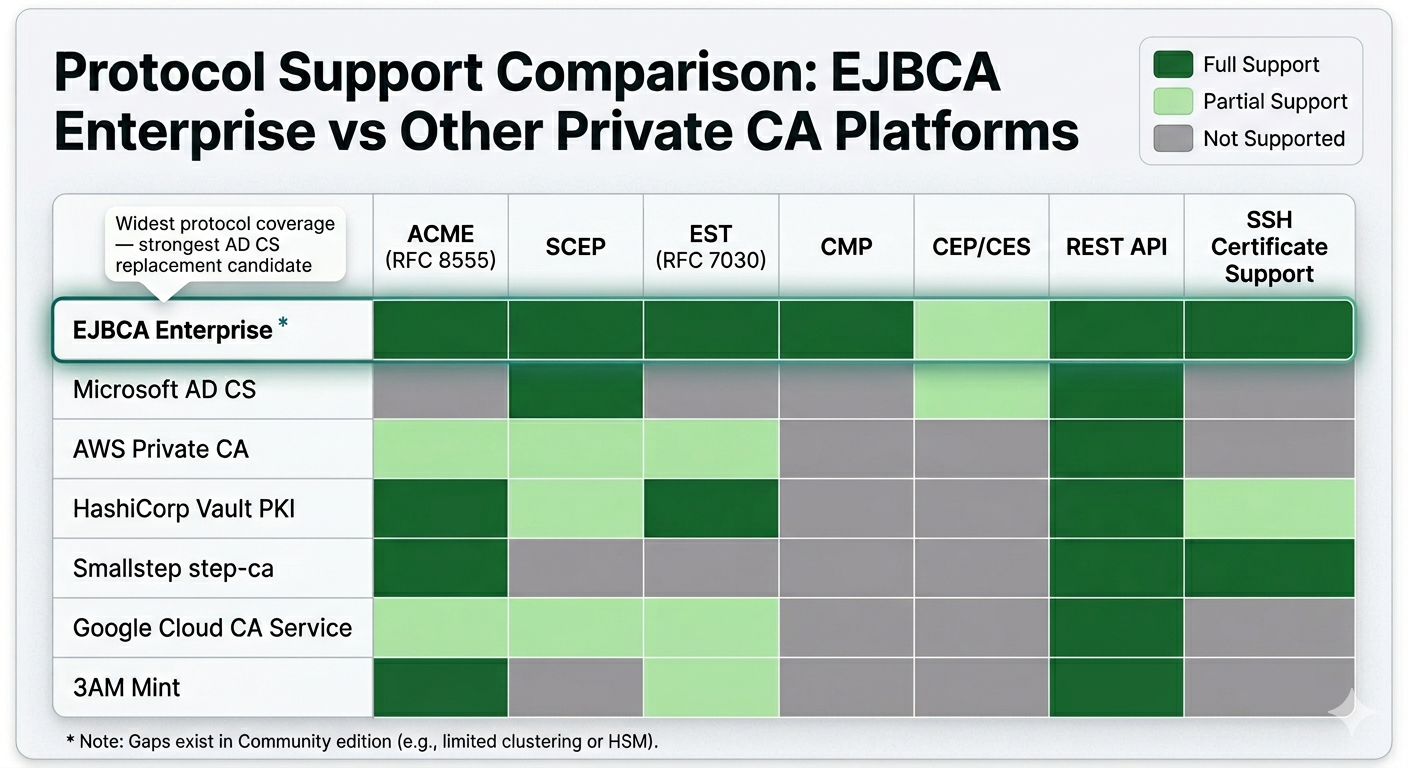
Protocol breadth. EJBCA Enterprise supports ACME (RFC 8555), SCEP, EST (RFC 7030), CMP, CEP/CES-compatible enrollment, REST API, and SSH certificates. Widest protocol coverage of any CA platform — critical for AD CS migration where existing enrollment patterns must be preserved.
AD CS replacement path. EJBCA Enterprise's CEP/CES-compatible enrollment allows GPO autoenrollment against a non-Microsoft CA — the closest functional replacement for AD CS in environments that must retire Microsoft CA infrastructure while keeping Windows autoenrollment working.
Compliance certifications. Common Criteria (EAL4+) evaluated configurations and FIPS 140-2 certified appliance options. For regulated industries, government, and defence where CA-specific certification is a procurement requirement, EJBCA Enterprise is often the only realistic option.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Operational complexity
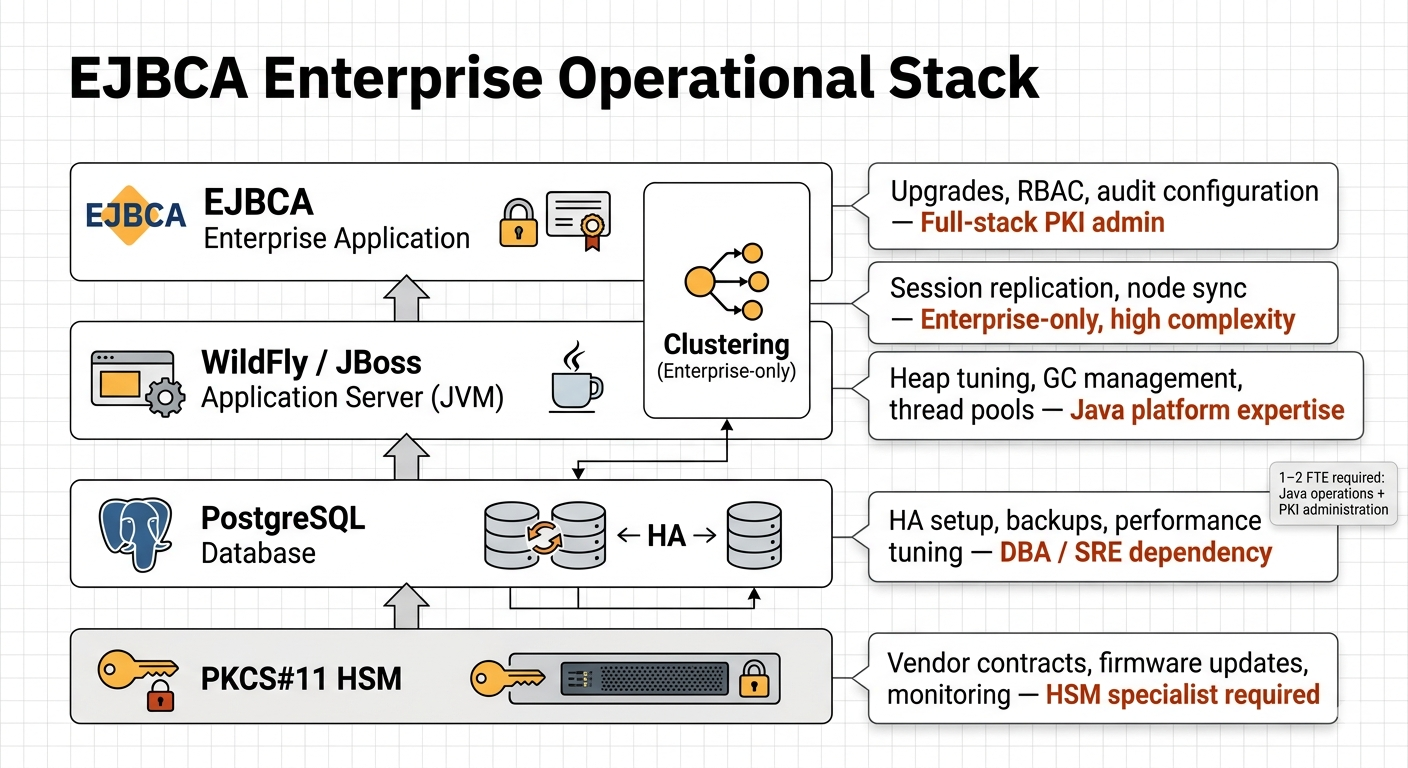
EJBCA is a Java application running on WildFly/JBoss with an external relational database and HSM connectivity for Enterprise deployments. Each layer adds operational demands:
| Layer | Operational demands | Skill requirement |
|---|---|---|
| JVM / WildFly | Heap tuning, GC configuration, thread pool sizing, app server management | Java platform expertise |
| Database | HA strategy, backups, performance monitoring, capacity planning | DBA or SRE skills |
| Clustering (Enterprise) | Session management, connection pooling, node synchronisation | Java EE clustering |
| HSM (Enterprise) | Vendor contracts, firmware updates, network HSM monitoring | HSM operations |
| Upgrades | DB migration, app server compatibility, HSM driver checks | Full stack coordination |
Typical staffing: 1–2 FTE split between Java platform operations and PKI administration.
Cost model
| Cost component | Community | Enterprise (5-yr) |
|---|---|---|
| Licensing | Free (LGPL) — lab/PoC only | $500K–$1.5M (quote-based) |
| Infrastructure | $50K–$150K | $50K–$150K |
| Staffing (1–2 FTE) | $750K–$1.5M | $750K–$1.5M |
| HSM contracts | — | $50K–$125K |
| 5-year TCO | Not suitable for production | $800K–$2.5M+ |
EJBCA Enterprise is the premium option — priced for organisations where protocol breadth, compliance certifications, and AD CS replacement justify the investment.
Security posture
EJBCA Enterprise supports the broadest HSM range (PKCS#11) — Thales Luna, Utimaco, AWS CloudHSM, Azure Managed HSM. Key protection is strong when HSM-backed. Attack surface includes the Java application, database credentials, web UI, and HSM network connectivity. Enterprise provides granular RBAC, command-level audit logging, and four-eyes approval workflows.
Compliance and certifications
EJBCA Enterprise's compliance position is its strongest commercial differentiator. Common Criteria (EAL4+) evaluated configurations for government and defence procurement. FIPS 140-2 appliance options for US federal and financial services. Structured audit logging with role attribution and tamper-evident log chains. Evidence extraction is more structured than AD CS but still requires SIEM/GRC integration for automated evidence packages.
When EJBCA fits — and doesn't
Choose EJBCA Enterprise for AD CS replacement with matching protocol breadth, Common Criteria or FIPS certification requirements, multi-tier regulated PKI, or government/national-scale programmes.
Skip EJBCA for lightweight DevOps/Kubernetes automation (step-ca or Vault PKI), AWS-native environments prioritising simplicity (AWS PCA or 3AM Mint), or when Java platform operations expertise is unavailable.
Hybrid pattern: EJBCA handles on-premises regulated PKI and Windows GPO enrollment; 3AM Mint provides the integration layer for cloud workloads — single enterprise view across EJBCA and cloud-issued certificates with unified policy and compliance logging.
Private CA Platform Comparison — AD CS (platform EJBCA commonly replaces) — step-ca (lighter DevOps alternative) — Vault PKI (Vault-native alternative) — AWS Private CA (managed cloud alternative) — 3AM Mint (cloud integration layer). Contact Axelspire or Ask Axel for architecture guidance.
