AWS Private CA: Operations, Cost & Compliance for Enterprise PKI
AWS Private Certificate Authority (formerly ACM Private CA) is a managed CA service that eliminates server, HSM, and clustering operations entirely. AWS manages the CA infrastructure; you manage IAM policies, certificate templates, and issuance workflows.
For AWS-native organisations, this is the fastest path to a production private CA. The trade-offs are real though: per-certificate pricing that compounds at scale, single-region CA instances, limited protocol support (no ACME, no SCEP, no EST natively), and full dependency on AWS's service availability and feature roadmap.
For the cross-platform evaluation, see the Private CA Platform Comparison.
What AWS Private CA does well
Zero infrastructure operations. No servers to patch, no HSMs to contract, no clustering to configure, no database to manage. AWS operates the CA on FIPS 140-2 Level 3 HSMs. Your operational surface is IAM policy management — which you already do for every other AWS service.
Native AWS integration. Direct integration with ACM for ALB/NLB/CloudFront TLS termination, IoT Core device certificates, and API Gateway mutual TLS. Certificate issuance through the AWS API or SDK — no separate CA client software needed.
Compliance inheritance. AWS PCA inherits AWS's SOC 2, ISO 27001, FedRAMP, HIPAA, and PCI-DSS compliance posture at the infrastructure layer. CloudTrail logs every API call. Evidence generation for auditors is largely automatable through AWS-native tooling.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Where AWS PCA breaks
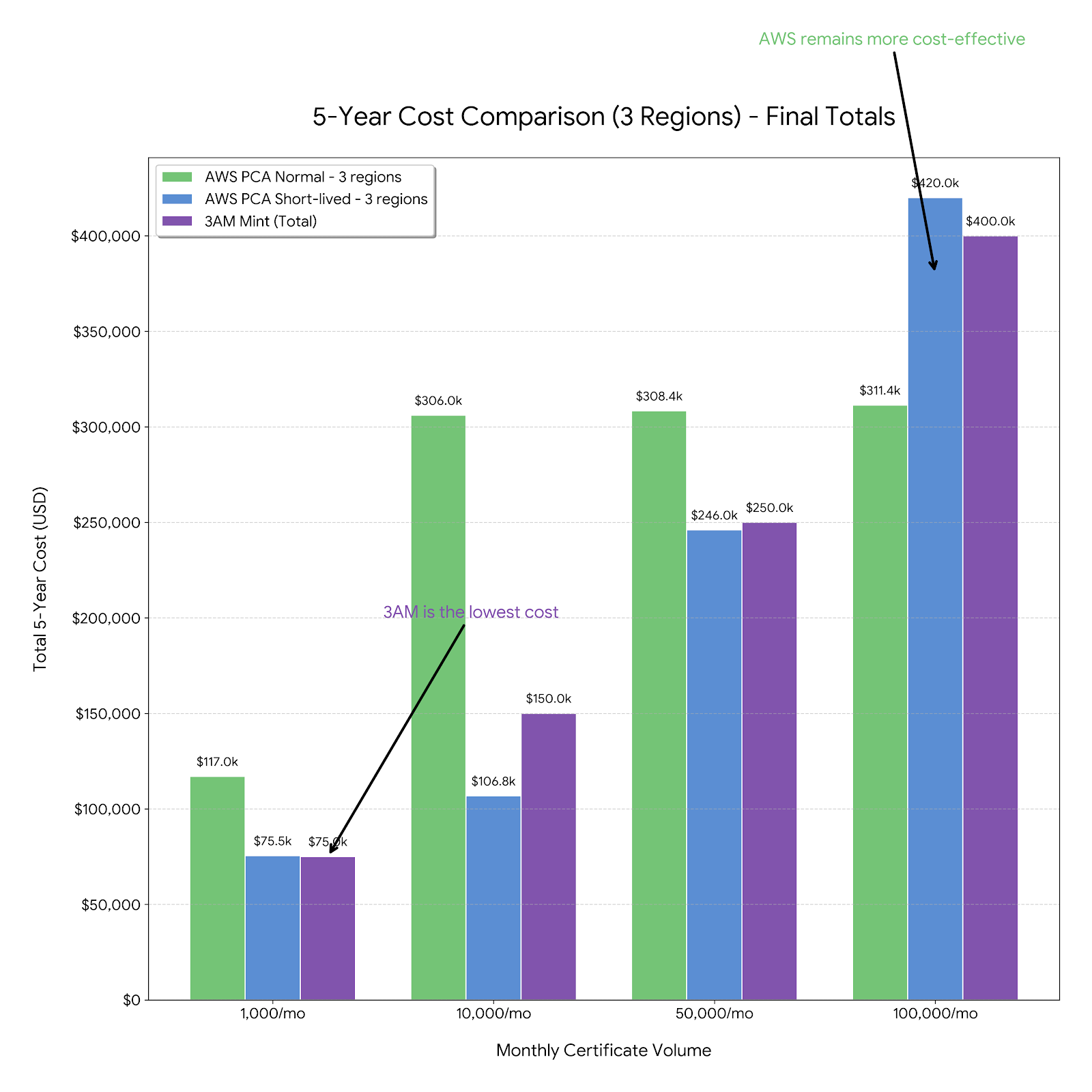
Five-year total cost: AWS PCA vs 3AM Mint
| Monthly volume | AWS PCA — 1 region 5-yr cloud spend | AWS PCA — 3 regions 5-yr cloud spend | 3AM Mint — AWS infra 5-yr cloud spend | AWS savings vs PCA 1-region |
|---|---|---|---|---|
| 1,000 certs/mo | ~$30,000 $24K CA + $6K certs | ~$90,000 $72K CA fees alone | <$300 + Axelspire licensing | ~$29,700 AWS infra saved |
| 10,000 certs/mo | ~$84,000 $24K CA + $60K certs | ~$252,000 $72K CA + $180K certs | <$1,200 + Axelspire licensing | ~$82,800 AWS infra saved |
| 50,000 certs/mo | ~$324,000 $24K CA + $300K certs | ~$972,000 $72K CA + $900K certs | <$3,000 + Axelspire licensing | ~$321,000 AWS infra saved |
| 100,000 certs/mo | ~$624,000 $24K CA + $600K certs | ~$1,872,000 $72K CA + $1.8M certs | <$6,000 + Axelspire licensing | ~$618,000 AWS infra saved |
AWS PCA figures are indicative (60 months × monthly rate) — verify current pricing at aws.amazon.com/private-ca/pricing. Per-CA fee ~$400/mo per active CA; short-lived certificate tier (≤7 days) carries lower per-issuance rates not reflected above. 3AM Mint AWS infrastructure (KMS signing calls ~$0.03/10K operations, Lambda invocations, CloudWatch) is near-zero at any certificate volume — the total cost comparison is Axelspire licensing vs AWS per-certificate fees. Contact Axelspire for a TCO model against your specific volume and region count.
Protocol limitations
AWS PCA is API-only. No native ACME server, no SCEP endpoint, no EST responder. Clients must use the AWS SDK or API to request certificates. This creates friction for non-AWS workloads, on-premises systems, or standard automation tooling that expects ACME or SCEP. Serving ACME clients from AWS PCA requires a protocol translation layer — exactly what 3AM Mint's CertBridge provides.
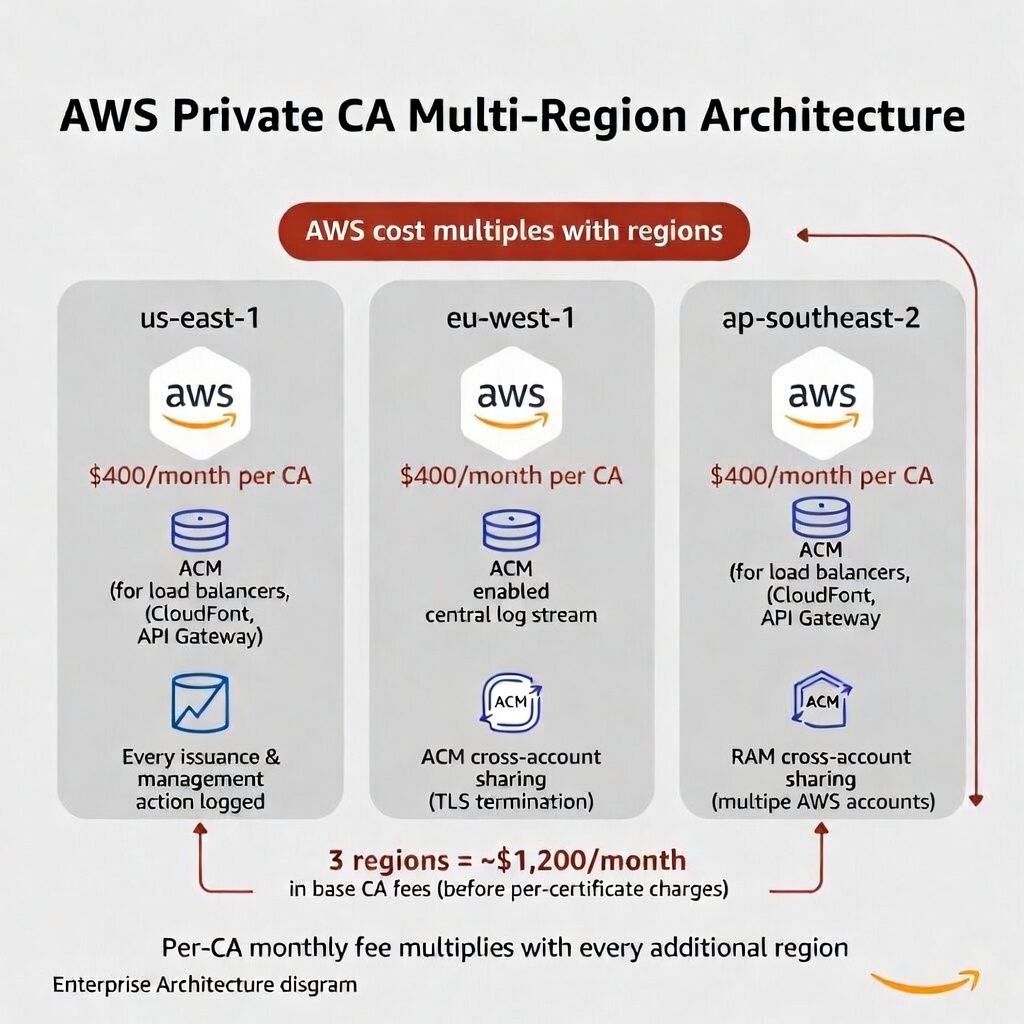
Single-region CA instances and lock-in
Each AWS PCA instance exists in a single AWS region. Multi-region architectures require separate CA instances, separate pipelines, and cross-region trust management — multiplying per-CA monthly costs. CA private keys are non-exportable; the hierarchy cannot be migrated to another platform. Commitment to AWS for the lifetime of that root CA.
Security posture
Key protection: AWS-managed FIPS 140-2 Level 3 HSMs. Non-extractable keys — the strongest key protection guarantee on this list, because you never have access to the key and therefore cannot accidentally expose it.
Attack surface: IAM policy misconfiguration and API credential theft. Both are auditable (CloudTrail, IAM Access Analyzer) and preventable with standard AWS security practices. No application-layer vulnerabilities to track.
Compliance and audit
CloudTrail records every certificate issuance, revocation, and CA management API call. AWS Config rules enforce CA compliance policies. SOC 2 Type II, ISO 27001, FedRAMP High, HIPAA, PCI-DSS at the AWS infrastructure layer.
Limitation: CloudTrail logs what AWS PCA did, but not business-context audit trails — which team requested a certificate, what approval workflow was followed, what policy authorised it. This enterprise context layer must come from external tooling or from a platform like 3AM Mint that wraps AWS PCA with enterprise issuance controls.
Extending AWS PCA with 3AM Mint
AWS PCA is strong infrastructure. Its limitations are at the protocol and enterprise integration layers — exactly where 3AM Mint and CertBridge operate:
- Multi-region from a single CA: CertBridge provides ACME endpoints across multiple regions backed by a single AWS PCA instance, eliminating per-region CA instances and their monthly costs.
- Protocol translation: ACME, REST, and enterprise enrollment interfaces to clients while the CA backend remains AWS PCA's HSM-protected infrastructure.
- Enterprise issuance controls: Policy-based approval workflows, team/project attribution, and business-context audit trails on top of AWS PCA's infrastructure-level logging.
When AWS PCA fits
Choose AWS PCA when the environment is AWS-native, operational simplicity is the priority, certificate volume is moderate, and native ACM integration is the primary consumption pattern.
Pair AWS PCA with 3AM Mint when you need ACME protocol support, multi-region coverage without per-region CA costs, enterprise issuance controls, or business-context audit trails on top of AWS PCA's infrastructure-level logging.
GCP-native? Google Cloud CA Service is the equivalent managed CA within GCP — same operational simplicity model, same per-certificate pricing dynamic.
Skip AWS PCA when per-certificate costs at high volume are prohibitive (evaluate 3AM Mint instead), multi-cloud CA portability is required, or self-managed CA control is preferred (Vault PKI or step-ca for Kubernetes workloads).
Private CA Platform Comparison — 3AM Mint (protocol + multi-region extension) — Google CA Service (GCP equivalent) — step-ca (self-managed ACME CA) — Vault PKI (Vault-native alternative). Contact Axelspire or Ask Axel for AWS PCA architecture guidance.
