Microsoft AD CS: Operations, Cost & Compliance Reality
Active Directory Certificate Services has been the default private CA for Windows-centric enterprises since Windows 2000. It ships with Windows Server, integrates with Group Policy, and — critically — supports GPO-based autoenrollment that no other platform fully replicates.
That integration is both AD CS's greatest strength and the reason organisations struggle to move away from it. This assessment covers what AD CS actually costs to run, where its security model breaks, and when the operational burden justifies migration.
For the cross-platform evaluation, see the Private CA Platform Comparison.
What AD CS does well
GPO autoenrollment remains AD CS's irreplaceable capability. Domain-joined Windows machines receive and renew certificates automatically — 802.1X network authentication, smart card logon, EFS encryption, and S/MIME email signing all flow from this mechanism. No competing CA replicates this end-to-end without workarounds.
Zero per-certificate cost. AD CS is included with Windows Server licensing. For organisations already paying for Windows Server and CALs, the CA functionality carries no incremental software cost.
Mature template system. Certificate templates with enrollment permissions, key usage constraints, and automatic issuance/renewal provide granular control within the Windows ecosystem.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Operational complexity
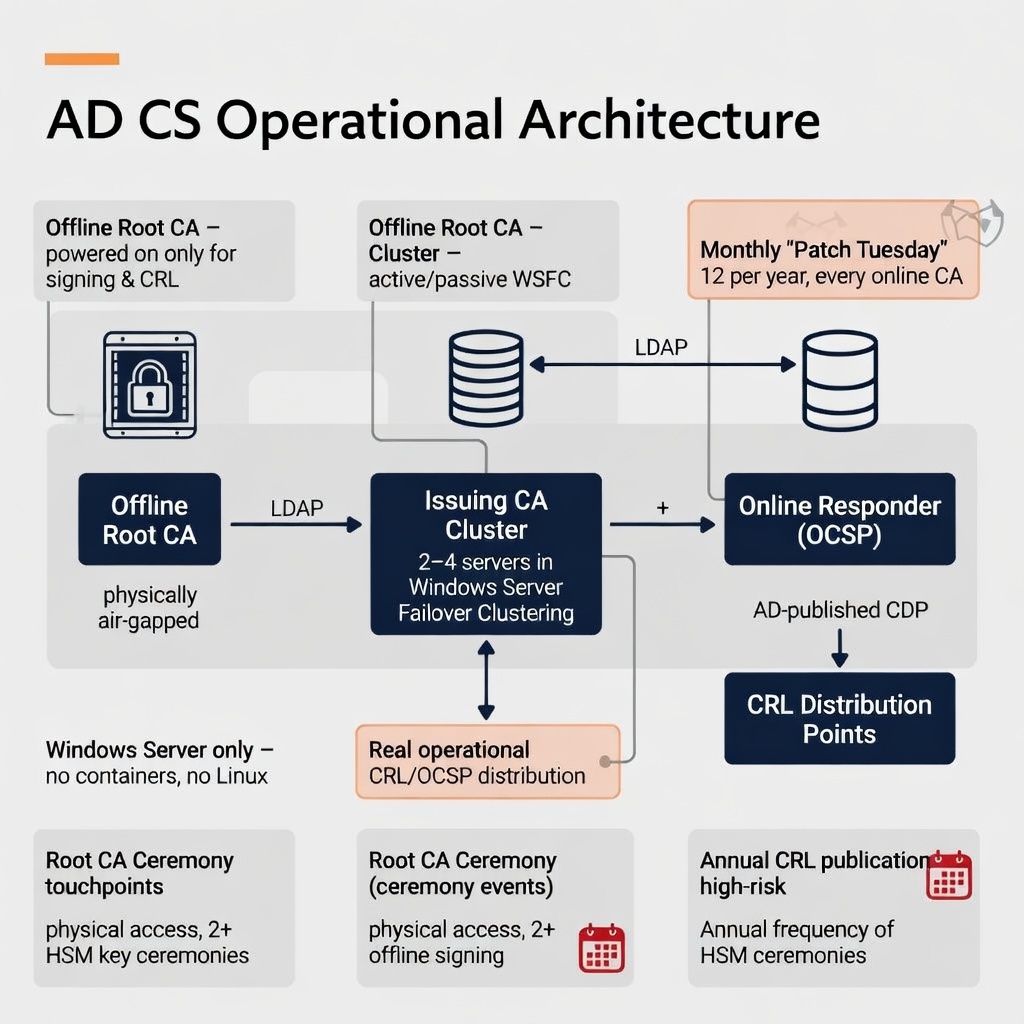
AD CS requires dedicated Windows Server infrastructure: an offline root CA (physically secured, powered on only for certificate signing and CRL signing), one or more online issuing CAs, high availability through Windows Server Failover Clustering (active/passive only, complex shared storage), and CRL/OCSP distribution through AD-published CDPs and/or separate Online Responder infrastructure.
Every component is Windows Server. No Linux option, no container deployment, no cloud-native variant.
| Operational area | AD CS requirement | Risk / burden level |
|---|---|---|
| OS patching | Monthly Patch Tuesday — 12 disruption windows/year per CA | Moderate — recurring |
| Root CA ceremonies | Physical access, documented procedures, 2+ authorised participants | High — skipped ceremonies break trust chains |
| High availability | WSFC active/passive, shared storage dependencies | Moderate — complex setup |
| API / automation | No REST API, no ACME — PowerShell COM or certreq.exe only | High — blocks cloud/CI-CD |
| Staffing | 0.5–1 FTE Windows PKI expertise | Moderate — specialist skill |
True cost of ownership
AD CS appears free. The actual five-year cost for a production deployment tells a different story:
| Cost component | 5-year range | Notes |
|---|---|---|
| Infrastructure (servers, clustering) | $30K–$80K | Windows Server instances |
| HSM (hardware + support) | $80K–$225K | Many orgs skip — accepting key exposure risk |
| Staffing (0.5–1 FTE PKI) | $375K–$750K | Largest cost component |
| Compliance evidence (manual) | $40K–$150K | $8K–$30K per audit cycle |
| 5-year TCO | $450K–$1M+ | The "free" CA is often the most expensive option |
Security assessment: ESC vulnerabilities
SpecterOps' "Certified Pre-Owned" research documented privilege escalation paths (ESC1 through ESC13) specific to AD CS. Several are enabled by default — ESC1 (overly permissive SAN specification in templates), ESC8 (NTLM relay against web enrollment), ESC11 (NTLM relay against ICertPassage RPC). These are not theoretical; penetration testing firms routinely exploit them.
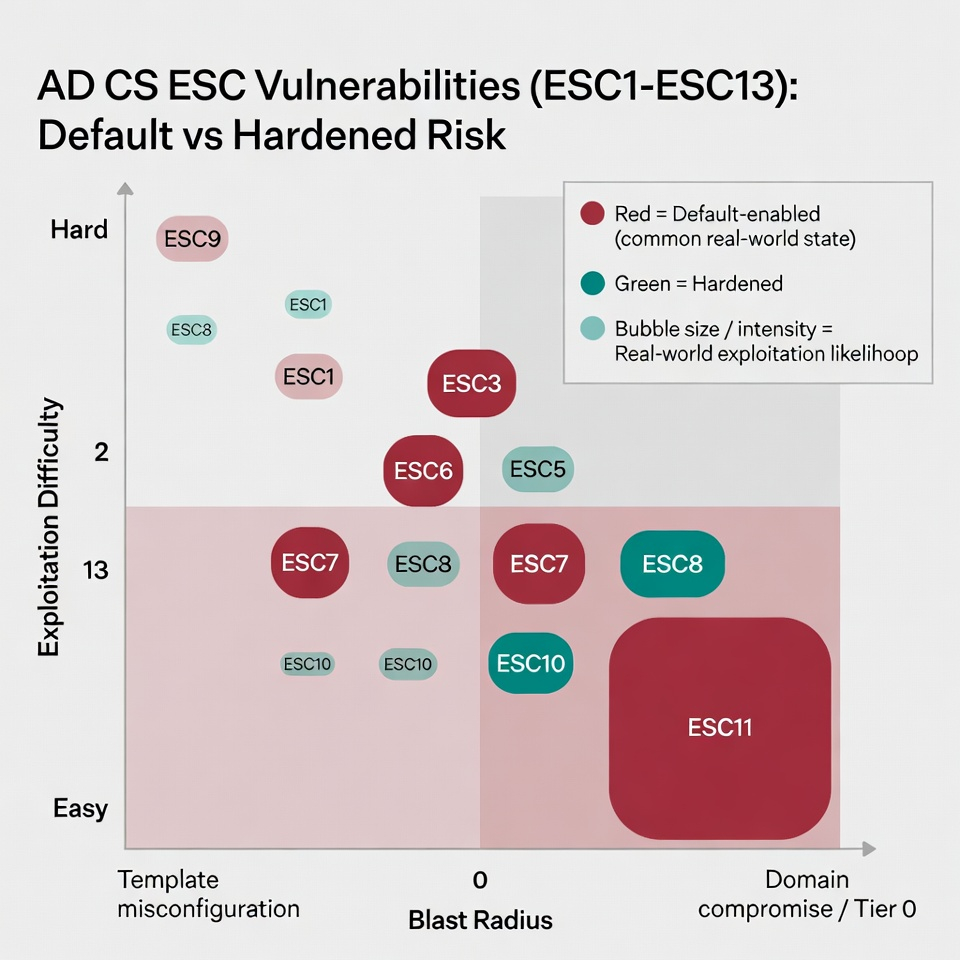
Without HSM integration, CA private keys sit in Windows CNG key store — any OS compromise exposes them. An AD CS compromise is a Tier 0 event equivalent to domain controller compromise, providing persistent access across the entire AD forest.
Compliance and audit reality
Audit evidence requires manual assembly from multiple sources: Windows Event Logs, AD group membership exports, template permission documentation, offline root ceremony records (typically paper), and CRL/OCSP functioning evidence. None is automated. Each audit cycle costs dedicated staff time.
AD CS has no CA-specific security certification. Windows Server has OS-level Common Criteria; CNG HSM providers may have FIPS 140-2. The CA application layer — templates, permissions, enrollment logic — has no independent certification.
When AD CS fits — and when to migrate
Keep AD CS when 90%+ of certificate consumers are domain-joined Windows, GPO autoenrollment is the required mechanism, Windows admin depth exists in-house, and there is no Kubernetes/container/cloud-native demand.
Migrate away when cloud and container workloads need certificates, ACME is required, ESC hardening hasn't been completed, the Windows PKI specialist leaves, or multi-cloud environments make Windows-only CA untenable.
Full replacement: EJBCA Enterprise is the closest functional replacement — its CEP/CES-compatible enrollment preserves GPO autoenrollment while adding ACME, SCEP, EST, and REST alongside a Common Criteria-certified compliance posture.
Containment + extension: Contain AD CS for Windows-only GPO use; deploy 3AM Mint for all cloud, container, and cross-platform issuance — with 3AM providing unified visibility and policy across both CAs. For pure cloud-native workloads, step-ca or AWS Private CA can cover ACME issuance without displacing AD CS for Windows endpoints.
Private CA Platform Comparison — EJBCA (AD CS replacement) — 3AM Mint (cloud + container issuance) — step-ca (lightweight ACME) — AWS Private CA (managed alternative). Contact Axelspire or Ask Axel to discuss AD CS migration options.
