3AM Mint: Serverless Private CA with KMS-Backed Key Operations
3AM Mint is the lightweight CA issuance engine in the Axelspire 3AM suite. It uses AWS KMS as its cryptographic engine — rather than running CA server software, it executes certificate signing operations directly against KMS, with the CA private key never leaving AWS KMS hardware. The result is the lowest AWS infrastructure cost of any CA option: near-zero per-certificate cloud spend regardless of volume, no per-CA monthly fee, no servers to operate.
Mint is deliberately focused: serverless issuance with KMS-backed key protection, ACME and REST protocol support via CertBridge, and structured CloudTrail audit logging. It is not a full PKI lifecycle platform — that is the role of the broader 3AM platform, which adds cross-CA integration across AD CS, AWS PCA, EJBCA and others, unified policy enforcement, enterprise workflow integration (ServiceNow, Jira, SIEM), and framework-ready compliance evidence generation. Mint is the issuance engine; 3AM is the management layer around it.
For the cross-platform evaluation, see the Private CA Platform Comparison.
Architecture: KMS as the cryptographic engine
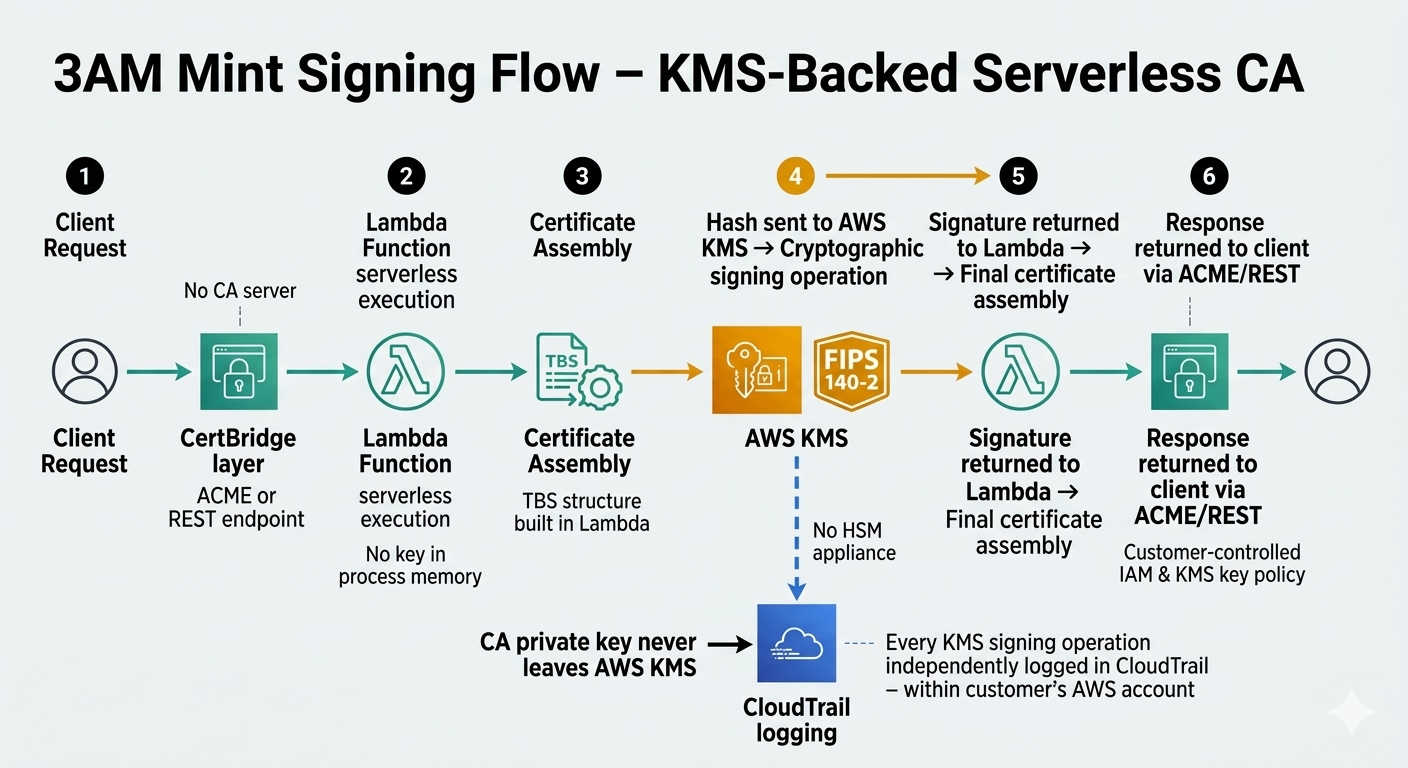
Every CA platform faces the same fundamental problem: protecting the CA private key. 3AM Mint takes the most direct approach available in AWS: the CA key is an asymmetric KMS key. It is created in KMS, used in KMS, and cannot be exported from KMS. There is no CA server holding key material in process memory, no HSM appliance to network-connect and maintain, no key ceremony to conduct.
When 3AM Mint needs to sign a certificate, it constructs the TBS (to-be-signed) certificate structure, sends the hash to KMS for signing, receives the signature, and assembles the final certificate. The key never leaves KMS. Every signing operation is an independent KMS API call, independently logged in CloudTrail.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Serverless execution: what gets eliminated
| Traditional CA burden | 3AM Mint | Why |
|---|---|---|
| Server patching | Eliminated | Lambda runtime updates are AWS-managed |
| HSM contracts & ceremonies | Eliminated | KMS key protection included in KMS pricing |
| Capacity planning | Eliminated | Serverless scales to demand automatically |
| HA engineering | Eliminated | AWS Lambda availability model applies |
| Process monitoring | Eliminated | No CA daemon, no JVM heap, no process to restart |
| What remains | IAM policies, KMS key policies, CloudWatch monitoring — standard AWS account operations already in place | |
Cost model: near-zero AWS infrastructure spend
Mint's defining commercial characteristic is that AWS infrastructure cost does not scale with certificate volume. The only cloud charges are KMS API calls (~$0.03 per 10,000 signing operations) and Lambda invocations (~$0.20 per 1M requests). At any realistic certificate volume this is negligible. Compare this to AWS PCA, which charges ~$400/month per CA instance plus per-certificate fees:
| Monthly volume | AWS PCA — 3 regions 5-yr cloud spend | 3AM Mint — AWS infra 5-yr cloud spend | AWS infra saved |
|---|---|---|---|
| 1,000/mo | ~$117,000 $72K CA fees + $45K certs | <$300 + Axelspire licensing | ~$116,700 |
| 10,000/mo | ~$306,000 $72K CA fees + $234K certs | <$1,200 + Axelspire licensing | ~$304,800 |
| 50,000/mo | ~$308,000 $72K CA fees + $236K certs | <$3,000 + Axelspire licensing | ~$305,000 |
| 100,000/mo | ~$311,000 $72K CA fees + $239K certs | <$6,000 + Axelspire licensing | ~$305,000 |
AWS PCA at 3 regions: $400/mo per CA × 3 = $1,200/mo CA fees, plus per-certificate charges (first 1,000 at $0.75, next 9,000 at $0.35, over 10,000 at $0.001). 3AM Mint AWS infrastructure is KMS + Lambda only. Total cost comparison is Axelspire licensing vs AWS per-certificate fees — contact Axelspire for a volume-specific TCO model.
CertBridge: protocol abstraction
CertBridge is the protocol layer that comes with 3AM Mint. It presents standard enrollment interfaces to certificate consumers while routing signing through Mint's KMS-backed CA — so clients see ACME or REST, not AWS API calls.
- Multi-region ACME from a single CA: ACME endpoints in multiple AWS regions backed by one CA instance — same policies, same audit trail, no per-region CA monthly fees.
- Protocol translation: Client automation choices (ACME, REST, custom) decouple completely from CA platform selection.
The 3AM platform: cross-CA and enterprise integration
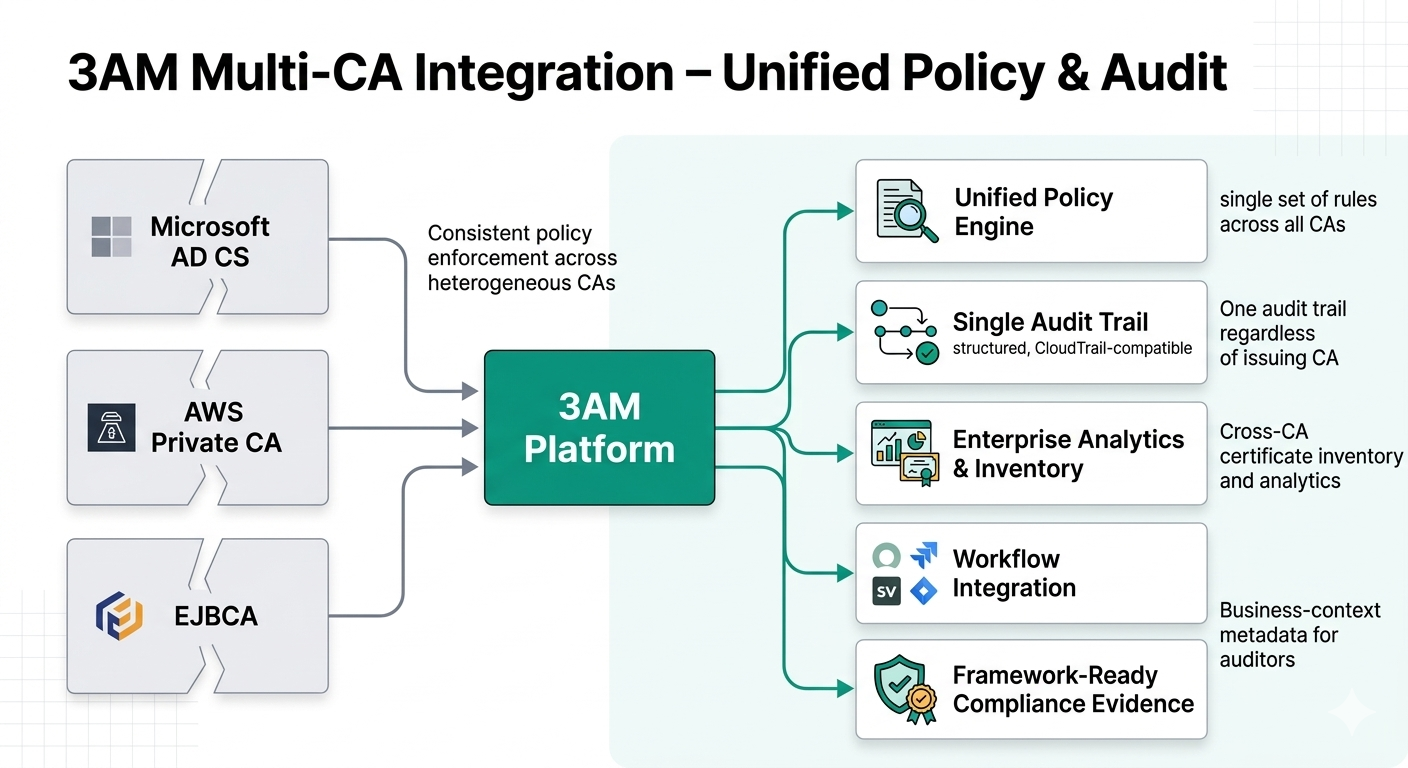
Mint handles issuance. The broader 3AM platform is the management layer organisations deploy when they need to govern a heterogeneous CA estate — not just the certificates Mint issues, but certificates from AD CS, AWS PCA, EJBCA, and other existing CAs, all under one policy and compliance framework.
- Cross-CA unified policy: One policy engine governing issuance across all CA backends simultaneously. Policy changes propagate to every integrated CA at once.
- Single audit trail across all CAs: Every certificate operation — Mint-issued, PCA-issued, EJBCA-issued — produces a consistent structured record in the customer's AWS account. One log format, one SIEM integration, one compliance evidence source regardless of how many CAs are in the estate.
- Enterprise workflow integration: ServiceNow, Jira, and SIEM connectors for certificate request approvals, incident alerting, and GRC correlation.
- Estate analytics: Certificate inventory, expiration forecasting, issuance patterns, and policy compliance — across all CAs, not per-silo.
3AM platform compliance logging
The platform layer adds structured compliance evidence on top of Mint's native CloudTrail logging:
| Evidence layer | Source | What is captured |
|---|---|---|
| KMS CloudTrail | 3AM Mint | Every cryptographic signing call — independently of application logs, AWS-controlled and cross-verifiable |
| Structured issuance records | 3AM platform | Requesting identity, authorising policy, CA used, KMS key ID, serial, SANs, validity, business metadata |
| Framework-ready evidence packages | 3AM platform | Pre-structured for SOC 2, PCI-DSS, FedRAMP, HIPAA, NIST 800-171 — reduces audit-cycle evidence effort from weeks to hours |
Operations comparison
| Dimension | Traditional CA AD CS, EJBCA, Vault | Managed CA AWS PCA, Google CAS | 3AM Mint issuance engine | 3AM platform adds on top of Mint |
|---|---|---|---|---|
| CA operations | ||||
| Server operations | Full | None | None | — |
| HSM operations | Contracts, ceremonies | None (provider-managed) | None (KMS-managed) | — |
| Protocol support | Varies by platform | API only | ACME, REST (CertBridge) | — |
| 5-yr AWS cloud cost | $0 (on-prem infra instead) | $75K–$1.9M | <$6K AWS infra | — |
| Data location | Customer-managed | Cloud provider account | Customer's AWS account | — |
| Staffing requirement | 0.5–2 FTE | 0.1–0.25 FTE | 0.1–0.25 FTE | — |
| Enterprise management — 3AM platform layer | ||||
| Multi-CA visibility | Single-CA only | Single-CA only | Mint-issued certs only | Cross-CA unified |
| Compliance evidence | Manual assembly | Cloud logs only | CloudTrail (KMS level) | Structured, framework-ready |
| Enterprise integration | Custom build | None | None | ServiceNow, Jira, SIEM |
Security posture
Key protection: AWS KMS (FIPS 140-2 Level 3). Non-extractable keys. Every signing operation logged in CloudTrail independently of 3AM application logic. No process memory exposure, no key ceremony risk, no HSM network attack surface.
Customer account deployment: Axelspire does not hold key material. The customer controls all access through standard AWS IAM. Axelspire's support access is governed by customer-controlled IAM roles with CloudTrail visibility — addressing supply chain risk concerns that arise with SaaS CA management platforms.
When 3AM Mint fits — and when you need the full platform
3AM Mint alone is the right choice for teams that need a private CA with low operational overhead and minimal AWS cost, without cross-CA complexity:
- Greenfield cloud PKI — AWS-centric organisations standing up private CA infrastructure for the first time and wanting to avoid the per-certificate and per-region fees of AWS PCA
- Platform engineering — teams needing ACME and REST issuance without building and operating CA server infrastructure
- High certificate volume — organisations where AWS PCA's per-certificate pricing compounds significantly at scale
- Multi-region coverage — single CA instance serving multiple regions via CertBridge without per-region CA fees
Add the 3AM platform when the organisation needs to govern more than Mint-issued certificates:
- Existing CA estate — AD CS, EJBCA, or AWS PCA already in place; need unified visibility, policy, and compliance logging across all of them
- Compliance-driven — SOC 2, FedRAMP, PCI-DSS audit cycles where manual evidence assembly from multiple CA logs is a recurring cost centre
- Enterprise workflow — certificate requests need ServiceNow/Jira approval routing or SIEM correlation for incident response
Consider alternatives when the environment is not AWS-based (GCP-native: Google CA Service), when Common Criteria CA-specific certification is a hard procurement requirement (EJBCA Enterprise), or when the use case is pure Windows GPO autoenrollment with no cloud requirement (AD CS).
Private CA Platform Comparison — AD CS (Windows GPO CA, common integration target) — EJBCA (on-prem enterprise CA) — AWS Private CA (managed CA Mint extends) — step-ca (lightweight ACME complement) — Vault PKI (Vault-native complement) — Google CA Service (GCP-native alternative). Contact Axelspire or Ask Axel for architecture consultation and TCO modelling.
