Machine Identity and Zero Trust: Why Certificates Are the Foundation, Not an Afterthought
Part of the Machine Identity Management guide.
Most zero trust implementations focus on the human side: multi-factor authentication, conditional access, identity-aware proxies. These are necessary. They are also the minority of your authentication surface.
In a typical enterprise environment, machine-to-machine traffic accounts for over 80% of all network communications. Service calling service. Container calling database. API gateway routing to backend. Load balancer terminating and re-establishing TLS. IoT device reporting to cloud hub. Every one of these connections requires authentication — and in a zero trust architecture, that authentication must happen at every boundary, every time, with no implicit trust based on network location.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
The authentication mechanism for all of this is the certificate. Specifically, X.509 certificates issued by your internal PKI, validated through a chain of trust, and presented through mutual TLS or equivalent protocol-level verification. Your zero trust maturity is, in practice, limited by your machine identity management maturity.
The Authentication Gap in Zero Trust
Zero trust frameworks — NIST SP 800-207, CISA's Zero Trust Maturity Model, Forrester's ZTX — all describe the same architectural principle: verify explicitly, use least-privilege access, assume breach. For human identities, the tooling ecosystem is mature. Identity providers, MFA tokens, device posture checks, and conditional access policies are well-understood procurement categories.
For machine identities, the gap is structural. Consider what happens when an organization deploys a service mesh to enforce zero trust between microservices:
Every service instance needs a unique identity. That identity must be cryptographically verifiable. It must be short-lived to limit the blast radius of compromise. It must be automatically rotated without service disruption. And it must be revocable in real time if the workload is compromised.
This is certificate lifecycle management operating at machine speed. If your PKI cannot issue certificates in milliseconds, your service mesh creates a bottleneck. If your rotation automation fails, your services lose their identity and cannot communicate. If your revocation infrastructure lags, a compromised workload retains trusted access to every service it can reach.
The organizations that struggle most with zero trust are not the ones lacking network segmentation tooling. They are the ones whose certificate infrastructure was designed for a world where humans requested certificates through a web portal and waited hours for approval.
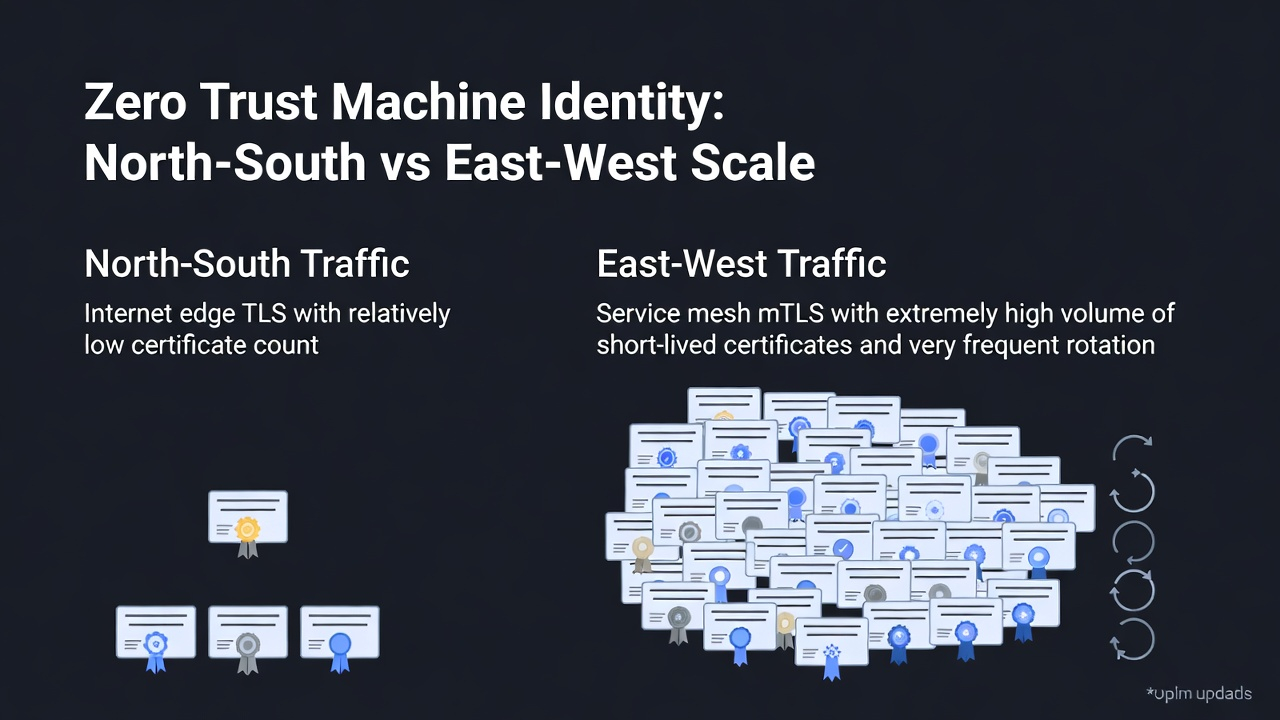
North-South vs. East-West: Two Different Machine Identity Problems
Zero trust creates two distinct machine identity challenges that require different operational approaches:
North-south traffic — connections entering or leaving the network boundary — is the traditional TLS domain. Externally-facing services present certificates to browsers and API clients. This is the machine identity problem that most organizations have partially solved, because public CAs and ACME-based automation have made external certificate management increasingly routine.
East-west traffic — internal service-to-service communication — is where zero trust exposes the machine identity gap. Internal services historically operated on the assumption that anything inside the network perimeter was implicitly trusted. Zero trust eliminates that assumption, which means every internal service now needs its own certificate, its own identity, and its own authentication handshake with every other service it communicates with.
The operational difference is scale. A typical enterprise might manage 1,000 to 5,000 external TLS certificates. The same enterprise, after adopting zero trust and microservices, might need 50,000 to 500,000 internal mTLS certificates — many of them short-lived, automatically rotated, and ephemeral. The PKI infrastructure, issuance automation, and governance framework must scale accordingly.
This is also where microsegmentation becomes operationally dependent on machine identity. You cannot enforce segment-level access policies if you cannot reliably identify which workload is requesting access. The identity must come before the policy.
What Certificate Infrastructure Needs to Support Zero Trust
Zero trust does not require replacing your existing PKI. It requires extending it to meet operational demands that traditional certificate management was not designed for.
Automated issuance at sub-second latency. When a container spins up and needs a certificate before it can accept traffic, the issuance path must complete in milliseconds, not minutes. This means API-driven enrollment — ACME, EST, or native Kubernetes CSR signing — with policy enforcement that does not introduce human approval bottlenecks.
Short-lived certificates as the default. Long-lived certificates are a liability in zero trust environments. If a workload certificate is valid for a year, a compromised workload has a year of trusted access. Short-lived certificates (hours, not days) reduce this window, but they require rotation automation that works without exception. Every rotation failure is a potential service outage.
Certificate revocation that actually works. Traditional CRL-based revocation is too slow for zero trust. By the time a CRL is published and distributed, the compromised credential has already been used. OCSP stapling improves latency but adds complexity. Short-lived certificates reduce revocation dependence by ensuring credentials expire before revocation becomes necessary — but only if your issuance infrastructure can sustain the rotation volume.
Multi-environment issuance. Zero trust spans cloud, on-premises, edge, and IoT. Your certificate infrastructure must issue and manage identities across all of these environments through a consistent policy framework. An IoT device authenticating to a cloud hub must be governed by the same trust hierarchy as a Kubernetes pod authenticating to an internal API, even though the issuance mechanisms, lifespans, and rotation constraints are completely different.
Cryptographic policy enforcement. Zero trust assumes breach. That assumption extends to cryptographic algorithms. If a weakness is discovered in a cipher suite or signing algorithm, you need the ability to identify every certificate in your environment that uses it and rotate those certificates to compliant alternatives. This is the crypto agility requirement that zero trust implicitly creates — and it depends on having a complete inventory of your machine identities.
The SPIFFE/SPIRE Model
The SPIFFE (Secure Production Identity Framework for Everyone) specification and its reference implementation, SPIRE, represent the most explicit architectural answer to the zero trust machine identity problem. SPIFFE provides a standardized identity framework for workloads — a URI-based identity (spiffe://trust-domain/workload-identifier) backed by short-lived X.509 certificates or JWT tokens, automatically issued and rotated by the SPIRE agent.
For enterprise leaders evaluating zero trust identity architecture, SPIFFE/SPIRE is significant because it separates the identity standard from the PKI implementation. Your existing certificate authority infrastructure can issue SPIFFE-compatible certificates. Your service mesh can consume them. Your policy engine can authorize based on them. The identity becomes portable across environments rather than locked to a specific vendor's issuance mechanism.
The limitation is that SPIFFE/SPIRE addresses workload identity in cloud-native environments. It does not address the full scope of machine identity management — IoT devices, SSH keys, code signing certificates, and legacy infrastructure all require separate but coordinated identity management.
Practical Sequencing for Enterprise Teams
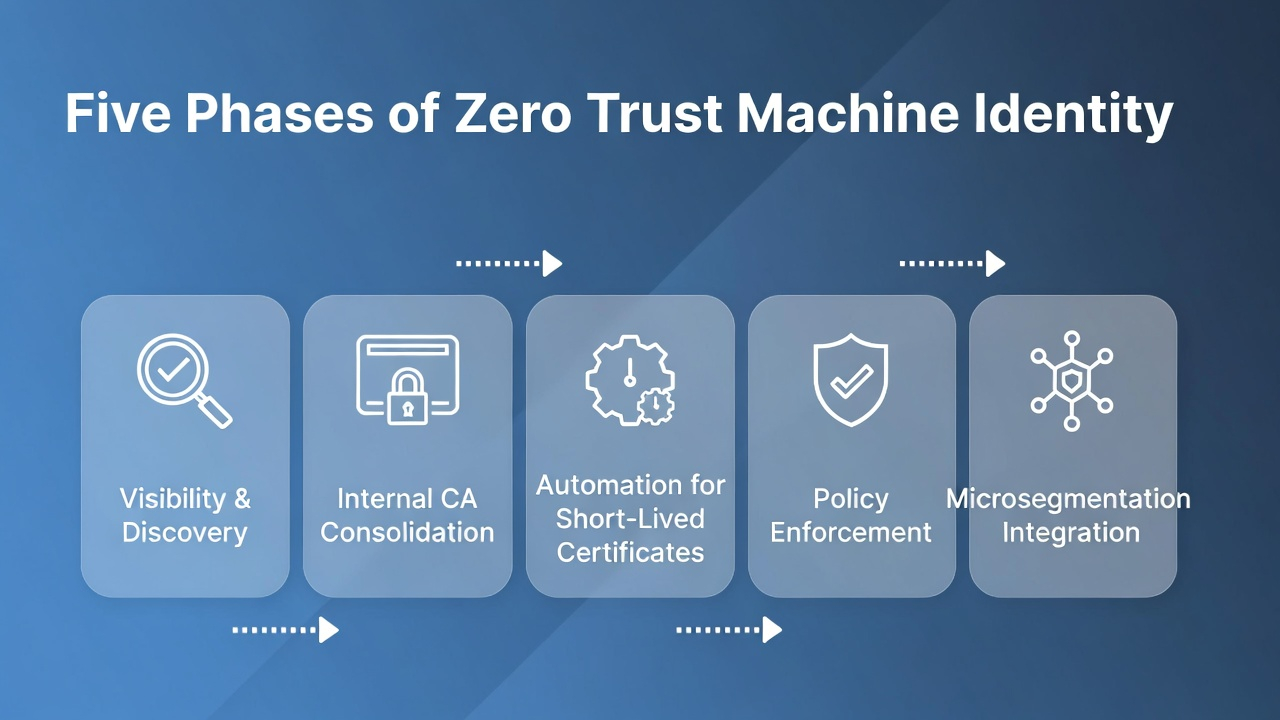
For organizations building toward zero trust, the machine identity work sequence matters:
Phase 1: Visibility. Before you can enforce zero trust authentication policies on machine-to-machine traffic, you need to know what machines exist and what identities they hold. Run a discovery exercise. Quantify the gap between managed and unmanaged certificates. This is the baseline that every subsequent decision depends on.
Phase 2: Internal CA consolidation. Most enterprises have multiple internal CAs — some managed, some forgotten, some self-signed. Consolidate to a governed CA hierarchy that can support the issuance volume zero trust requires. This does not mean a single CA; it means a single trust framework with delegated issuance authority.
Phase 3: Automation. Deploy ACME or EST-based enrollment for server and workload certificates. Integrate with your container orchestrator's native CSR signing. Automate rotation for every certificate with a lifespan under 90 days. This is where the operational investment pays off — manual processes do not survive at zero trust scale.
Phase 4: Policy enforcement. With visibility and automation in place, layer on policy: minimum key lengths, approved algorithms, maximum lifespans, required SAN attributes, and geographic constraints on issuance. This is the governance layer that makes your machine identity program auditable.
Phase 5: Microsegmentation integration. With workload identities reliably issued and rotated, you can now enforce segment-level policies based on cryptographic identity rather than network address. This is where machine identity enables microsegmentation — and where zero trust delivers its full value.
FAQ
Can we implement zero trust without managing machine identities? Not meaningfully. Zero trust requires authentication at every boundary. For machine-to-machine traffic — which represents the majority of enterprise communications — that authentication depends on certificates and workload identities. Without machine identity management, zero trust policies cannot be enforced on east-west traffic.
What is the difference between mTLS and standard TLS in a zero trust context? Standard TLS authenticates the server to the client. Mutual TLS (mTLS) authenticates both sides. Zero trust requires mTLS for internal service-to-service communication because both the requesting and receiving service must prove their identity. This doubles the certificate management burden compared to server-only TLS.
How do short-lived certificates reduce zero trust risk? Short-lived certificates (hours instead of months) limit the window during which a compromised credential can be used. If a certificate expires in 4 hours, a stolen certificate is useless after 4 hours — without requiring revocation infrastructure to act. The tradeoff is that issuance and rotation must be fully automated to sustain the volume.
How does machine identity relate to IoT devices in a zero trust architecture? IoT devices are machine identities with unique constraints. They must authenticate to gateways and cloud services, often over constrained networks with limited compute resources. Zero trust principles apply — no device should be implicitly trusted — but the certificate management approach must account for long device lifespans, intermittent connectivity, and hardware-bound key storage. SPIFFE/SPIRE brings zero-trust workload identity to device fleets — edge SPIRE agents attest devices using TPM quotes and issue short-lived SVIDs, applying the same "never trust, always verify" model used in cloud-native environments. See SPIFFE & Workload Identity for Device Fleets for the architecture. For the hardware root of trust that makes device attestation possible, see Hardware-Backed Device Identity.
Machine Identity Management — Workload Microsegmentation — SPIFFE & Workload Identity — Hardware-Backed Device Identity — mTLS Architecture. Contact Axelspire or Ask Axel.
