Workload Identity and Microsegmentation: Enforcing East-West Trust with Certificates
Part of the Machine Identity Management guide.
Microsegmentation promises granular control over which workloads can communicate with which other workloads. In practice, most implementations fall short because they enforce policies based on network attributes — IP addresses, VLAN tags, port numbers — rather than cryptographic identity.
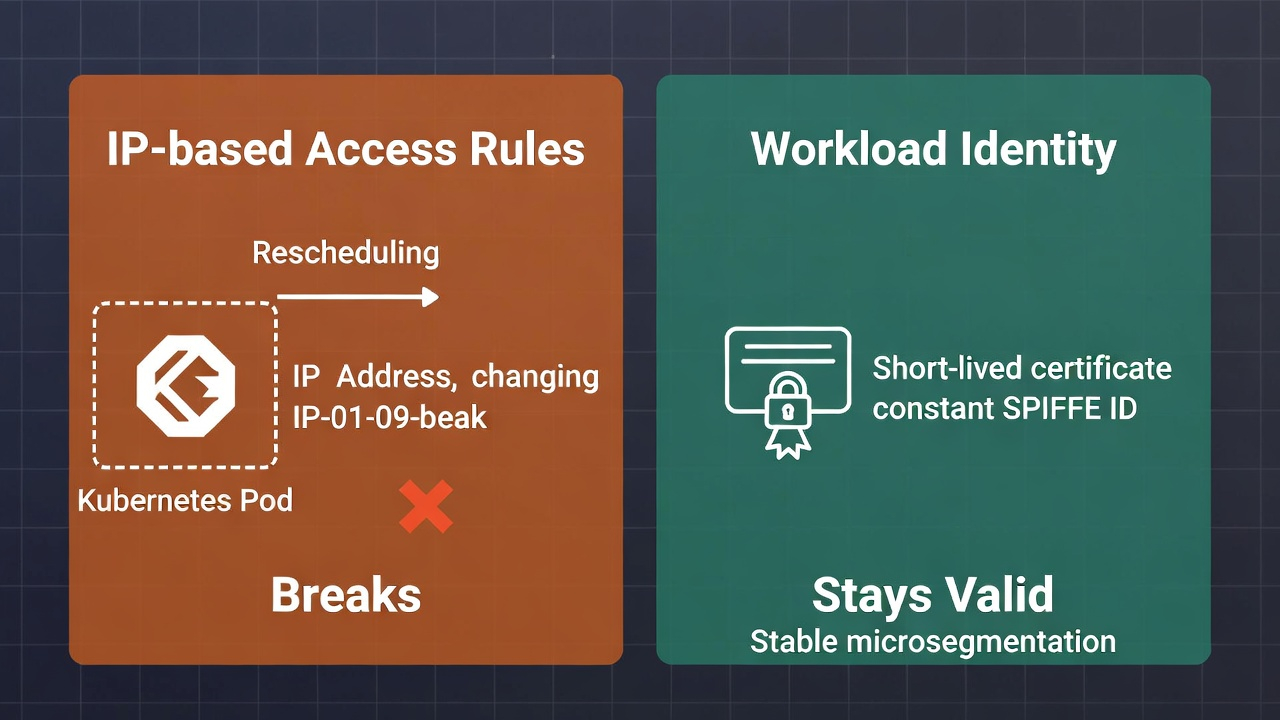
The problem with network-based segmentation is that network attributes are not identity. IP addresses change when containers reschedule. VLAN assignments are shared across unrelated workloads. Port numbers indicate protocol, not authorization. A firewall rule that permits traffic from 10.0.3.0/24 to port 5432 is not verifying which workload is making the request — it is verifying where the request originates, which is a weaker guarantee that evaporates entirely when workloads are ephemeral, mobile, or compromised.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Workload identity solves this by binding a cryptographic certificate to each workload instance. The certificate is the identity. It travels with the workload regardless of what IP it receives, which node it runs on, or which network segment it occupies. When a workload presents its certificate to another workload via mutual TLS, both sides know exactly who they are talking to — and both sides can enforce policies based on that identity rather than network topology.
This is where machine identity management and microsegmentation converge. Without reliable, automated, scalable workload identity issuance, microsegmentation policies cannot be enforced at the identity level. The result is network segmentation with more rules, not the identity-aware zero trust enforcement that the architecture promises.
Why IP-Based Microsegmentation Breaks Down
Traditional microsegmentation tools create fine-grained firewall rules between network segments. This works in static environments where workloads have predictable, long-lived IP addresses. It fails in the environments where microsegmentation matters most:
Container orchestration. In a Kubernetes cluster, pod IP addresses are ephemeral. A pod is created, assigned an IP from a CIDR range, runs for minutes or hours, terminates, and its IP is reassigned to a different workload. Writing firewall rules against these IPs requires constant rule updates that lag behind the orchestrator's scheduling decisions. By the time the rule is applied, the workload it was intended for may no longer exist at that address.
Multi-cloud and hybrid. Workloads running across AWS, Azure, and on-premises infrastructure occupy different IP spaces with different network abstractions. A microsegmentation policy that references AWS security group IDs is meaningless in Azure. A policy that references on-premises VLANs is meaningless in either cloud. Without a common identity layer, cross-environment segmentation policies cannot be expressed consistently.
Lateral movement after compromise. The entire point of microsegmentation is to limit lateral movement. But if an attacker compromises a workload and the segmentation policy is based on the workload's IP address, the attacker inherits the workload's network access. IP-based policies cannot distinguish between a legitimate workload and an attacker operating from the same network position. Certificate-based identity can, because the attacker would need to possess the workload's private key to pass an mTLS handshake — and if key storage is properly implemented, that key is bound to the workload's runtime and not extractable.
Certificate-Based Workload Identity in Practice
The operational model for certificate-based microsegmentation follows a consistent pattern across service mesh and platform-native implementations:
Identity issuance. When a workload starts, it requests a certificate from an identity provider — either a sidecar proxy (Envoy in Istio/Linkerd), a node agent (SPIRE), or the platform's native CSR signing (Kubernetes CertificateSigningRequest API). The certificate encodes the workload's identity as a SPIFFE ID, a Kubernetes service account reference, or a custom SAN. The certificate is short-lived, typically hours, and automatically rotated.
Mutual TLS enforcement. All workload-to-workload communication is encrypted and authenticated via mTLS. Both the client and server present certificates. The receiving workload validates the client's certificate against the trust anchor and extracts the identity from the certificate's SAN or SPIFFE ID. This identity is what the authorization policy evaluates — not the source IP.
Policy evaluation. The authorization layer (the service mesh control plane, the CNI plugin, or a policy engine like OPA) evaluates whether the authenticated identity is permitted to access the requested resource. The policy is expressed in terms of identity: "workload A in namespace production may call workload B on path /api/v2." Not in terms of network: "10.0.3.15 may connect to 10.0.4.22 on port 8080."
Certificate rotation. Because workload certificates are short-lived, rotation is continuous. The identity provider reissues certificates before they expire, with no service disruption. If a workload is decommissioned, its certificate simply expires and is never reissued. There is no revocation latency — the credential's short lifespan is itself the revocation mechanism.
This model depends entirely on the underlying machine identity infrastructure being fast enough to issue certificates on demand, reliable enough to never miss a rotation, and governed enough to enforce consistent policies across all workload types.
Scaling Workload Identity Across Environments
The architectural challenge for enterprise teams is extending workload identity beyond a single cluster or service mesh into a coherent cross-environment identity fabric. This is where organizational complexity maps directly to technical complexity:
Kubernetes-native environments are the easiest starting point. Service meshes like Istio and Linkerd handle mTLS transparently. SPIRE integrates with Kubernetes attestation to bind workload identity to verifiable platform attributes (namespace, service account, node). The certificate lifecycle is fully automated within the cluster boundary.
VM-based and legacy workloads require a different approach. These workloads cannot run sidecar proxies and do not have a container orchestrator managing their lifecycle. Workload identity for VMs typically relies on agent-based certificate enrollment — an agent running on the VM that requests and rotates certificates through ACME, EST, or a vendor-specific protocol. The identity model is the same; the issuance mechanism is different.
IoT and edge devices are the most constrained environment. These devices need machine identities to authenticate to gateways and cloud services, but they operate with limited compute, intermittent connectivity, and long lifespans that make short-lived certificate rotation impractical. The microsegmentation model for IoT is typically gateway-mediated: the device authenticates to a gateway with a longer-lived device certificate, and the gateway enforces segmentation policies on behalf of the device fleet.
Cross-environment trust. The common thread is a shared trust hierarchy. Every workload certificate, regardless of where it was issued or what mechanism delivered it, must chain to a common root or set of cross-certified roots. Without this, workloads in different environments cannot mutually authenticate. Establishing and governing this trust hierarchy is the architectural decision that determines whether your microsegmentation strategy can span your full infrastructure or remains confined to individual environment silos.
What Microsegmentation Requires from Your PKI
If your organization is planning or expanding microsegmentation, the following PKI capabilities are prerequisites:
Sub-second issuance latency. Kubernetes pods can start in under a second. If your CA takes 5 seconds to issue a certificate, you have created a startup bottleneck that defeats the purpose of container orchestration. The CA must support high-throughput, low-latency issuance through API-driven enrollment.
Volume capacity. A single Kubernetes cluster with 500 services, each with 10 replicas, each requiring a certificate rotated every 4 hours, generates approximately 30,000 certificate operations per day. Across multiple clusters and environments, this scales to hundreds of thousands of operations. Your issuance infrastructure must sustain this without degradation.
Consistent policy enforcement across issuance points. If workload certificates in Kubernetes are issued with 4-hour lifespans using ECDSA P-256, but VM workload certificates are issued with 1-year lifespans using RSA-2048, your microsegmentation policies operate on inconsistent trust assumptions. Policy enforcement must be centralized even when issuance is distributed.
Auditability. Every certificate issued is a trust decision. For compliance and incident response, you need a complete record of which identities were issued, when, by which CA, with what parameters, and to which workload. This is the operational audit trail that regulators and incident responders require.
Trust hierarchy that spans environments. Workloads in AWS, Azure, on-premises Kubernetes, and IoT edge deployments must all trust each other's certificates for cross-environment microsegmentation to work. This requires a CA hierarchy designed for multi-environment trust, not a collection of isolated per-environment CAs.
The Relationship Between Identity Maturity and Segmentation Maturity
Organizations often approach microsegmentation as a network project. Buy a microsegmentation platform, deploy agents, write policies, enforce. The machine identity dependency only becomes visible when enforcement fails — when policies cannot be applied because workloads lack verifiable identities, or when certificate rotation failures cause service disruptions that force teams to relax enforcement.
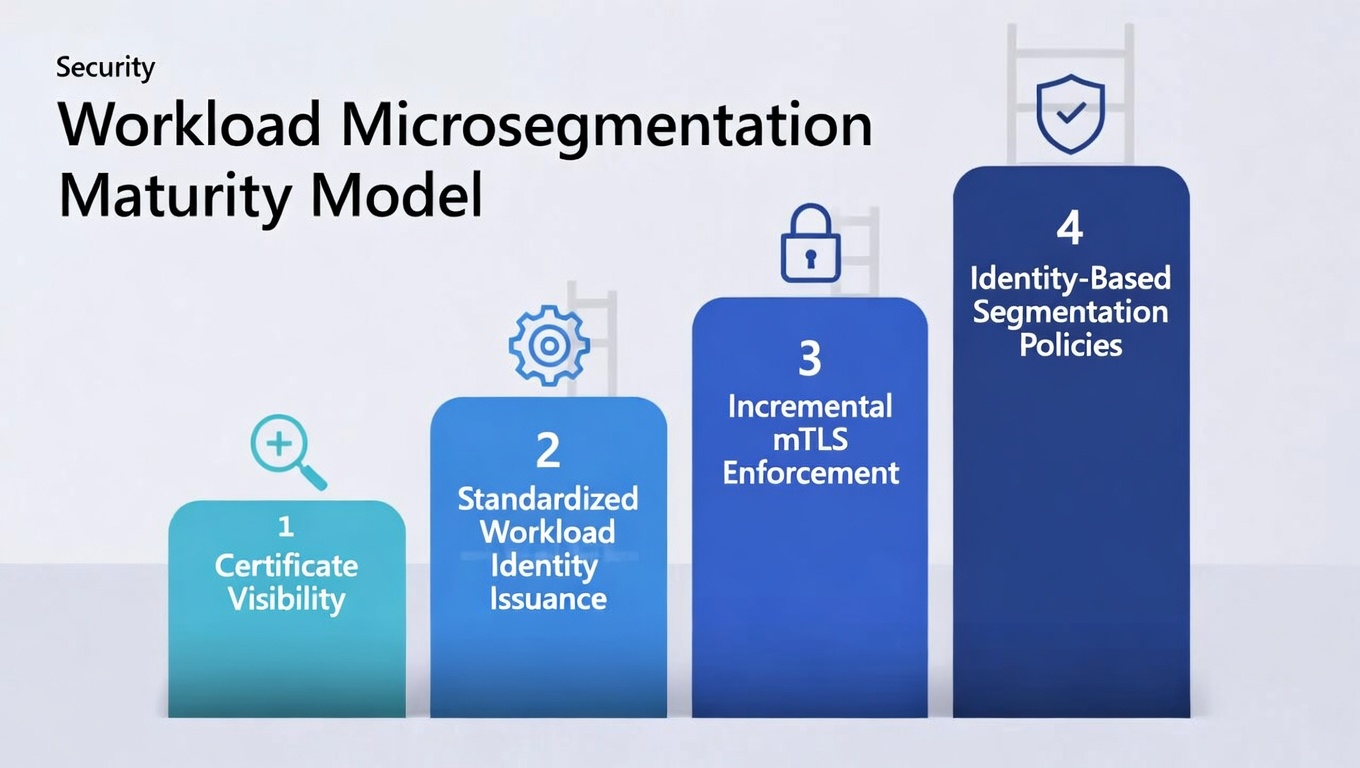
The pragmatic approach is to sequence the work explicitly:
First, achieve certificate visibility across your workload environments. Know which workloads have certificates, which do not, and which CAs are issuing them.
Second, standardize workload identity issuance. Converge on a common identity format (SPIFFE is the most portable) and ensure your issuance infrastructure can support the volume and latency requirements.
Third, deploy mTLS enforcement incrementally. Start in permissive mode (log but do not block unauthenticated traffic), identify workloads that lack certificates, remediate, then shift to strict enforcement.
Fourth, layer on identity-based microsegmentation policies. With mTLS enforced and workload identities reliable, policies based on cryptographic identity become enforceable.
This is not a fast process. But it is the only process that delivers microsegmentation that actually works in dynamic, multi-environment enterprise infrastructure.
FAQ
What is the difference between network segmentation and identity-based microsegmentation? Network segmentation enforces boundaries based on network attributes — IP addresses, VLANs, subnets. Identity-based microsegmentation enforces boundaries based on cryptographic workload identity, verified through mutual TLS. The latter is more resilient to workload mobility, IP reuse, and post-compromise lateral movement.
Do I need a service mesh for workload identity? No, but a service mesh simplifies it in Kubernetes environments. Service meshes like Istio and Linkerd handle mTLS certificate issuance, rotation, and enforcement transparently. For non-Kubernetes workloads, SPIRE agents or platform-native certificate enrollment can provide the same identity model without a service mesh.
How do short-lived workload certificates affect performance? The mTLS handshake adds latency to each connection — typically 1-3 milliseconds. Connection pooling and session resumption reduce the per-request impact. The certificate rotation process itself is background and non-disruptive when properly implemented. The measurable performance cost is small; the security benefit of eliminating long-lived credentials is significant.
Can IoT devices participate in identity-based microsegmentation? Not directly in the same way as cloud workloads. IoT devices typically authenticate to a gateway using device certificates with longer lifespans, and the gateway enforces microsegmentation policies on behalf of the device fleet. The device identity model differs from the workload identity model, but both derive from the same machine identity management framework. For how SPIFFE/SPIRE can bridge the gap between cloud workload identity and device fleets — with edge SPIRE agents on gateways attesting downstream devices — see SPIFFE & Workload Identity for Device Fleets. For the hardware-backed device credentials that anchor this attestation, see the Hardware-Backed Device Identity guide.
Machine Identity Management — Machine Identity & Zero Trust — SPIFFE & Workload Identity — Hardware-Backed Device Identity — mTLS Architecture. Contact Axelspire or Ask Axel.
