Machine Identity Governance: Ownership, Policy, and Lifecycle at Enterprise Scale
Part of the Machine Identity Management guide.
Automating certificate issuance without governance is just producing sprawl faster.
This is the mistake organizations make when they approach machine identity management as a tooling problem rather than an organizational one. They invest in certificate lifecycle automation, deploy ACME enrollment across their infrastructure, and reduce their mean time to issuance from days to seconds. Then they discover that they have 10 times more certificates than before, issued by more teams, to more services, with no ownership records, no policy enforcement, and no audit trail that satisfies anyone.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Machine identity governance is the discipline that sits between visibility (knowing what exists) and automation (managing it at scale). It answers the questions that tools alone cannot: Who is authorized to issue certificates? What cryptographic parameters are permitted? How long can a certificate live before it must be rotated? Who owns each certificate, and what happens when that person leaves? How do you prove compliance to an auditor who asks to see your certificate management controls?
Without governance, you have certificates. With governance, you have a machine identity program.
Why Governance Is Harder Than It Looks
Machine identity governance is structurally more difficult than human identity governance because the entities being governed are diverse, distributed, and managed by teams with different operational priorities.
Human identity governance has a natural center of gravity: the identity provider. Active Directory, Okta, or Entra ID is the system of record. User accounts are created through HR-initiated workflows, managed through IAM policies, and decommissioned through offboarding procedures. One system, one lifecycle, one governance model.
Machine identities — the non-human identities (NHIs) that authenticate workloads, devices, and services — have no single system of record. Certificates are issued by internal CAs, public CAs, cloud-managed CAs, and developer-provisioned CAs. SSH keys are generated on individual machines. Workload identities are issued by service mesh control planes and SPIRE agents. API tokens are created in SaaS admin consoles. Each of these identity types has its own issuance mechanism, its own lifecycle characteristics, and its own team of origin.
The governance challenge is not technical standardization — forcing all non-human identities through a single issuance pipeline would be impractical and would break the operational workflows that depend on distributed issuance. The governance challenge is policy consistency across distributed issuance. Different teams can issue certificates through different mechanisms, but all certificates must conform to the same policy framework.
The Four Pillars of Machine Identity Governance
A functional governance framework rests on four pillars. Remove any one of them and the framework does not hold under audit scrutiny or operational stress.
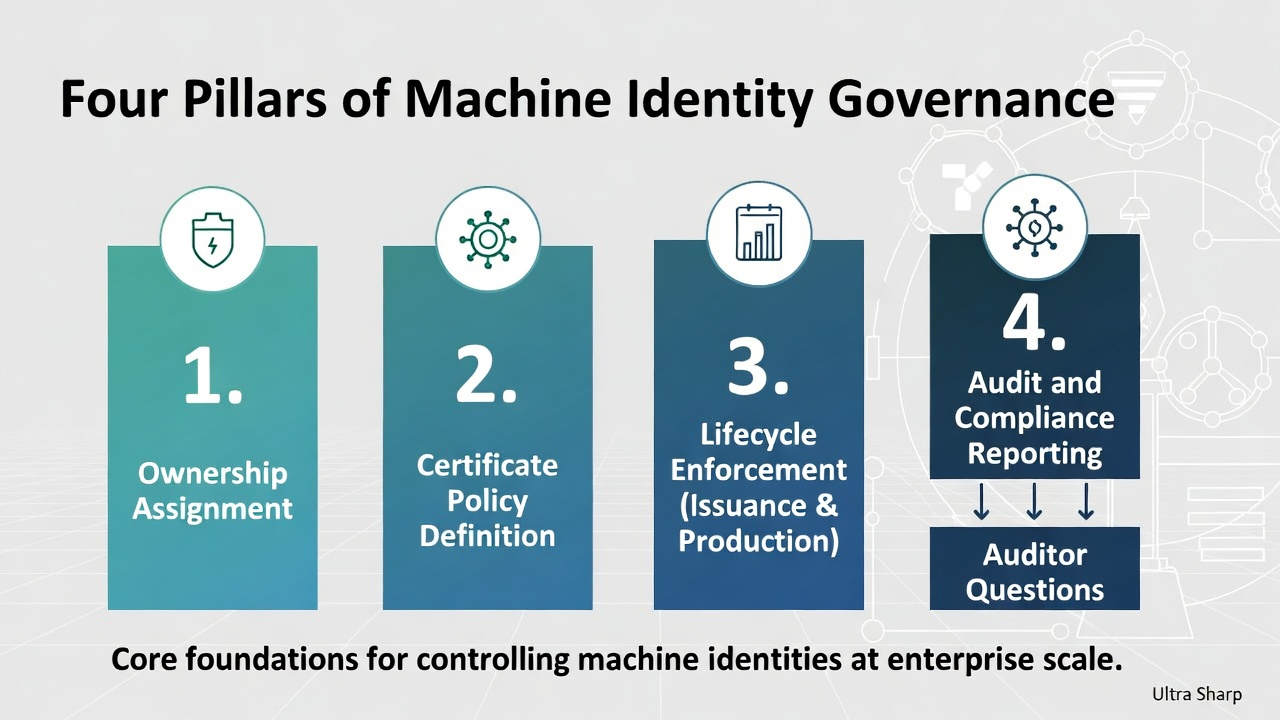
1. Ownership Assignment
Every machine identity must have an identifiable owner — a team or individual accountable for its lifecycle. This is the governance requirement that organizations resist most and benefit from most.
Ownership is not the same as creation. The developer who ran certbot certonly to get a certificate is not necessarily the owner. The owner is the team responsible for the service that certificate protects. When the certificate approaches expiration, the owner receives the alert. When the certificate needs to be rotated due to a policy change, the owner executes the rotation. When an auditor asks who is responsible for a certificate issued to a deprecated service, the owner answers.
Implementing ownership at scale requires integration with your certificate inventory. Every discovered certificate must be attributed to a team. Certificates that cannot be attributed — the 15-25% of orphan certificates that most discovery exercises reveal — must be triaged: determine the service, find the team, assign ownership, or decommission.
Ownership also needs to survive personnel changes. Machine identity ownership should be assigned to teams or roles, not individuals. When a team lead leaves, their machine identity ownership should transfer automatically through the same mechanisms that handle other role-based handoffs.
2. Certificate Policy Definition
Certificate policy is the set of rules that govern what can be issued, by whom, with what parameters, and for how long. In traditional PKI, certificate policy is documented in a Certificate Policy (CP) and Certification Practice Statement (CPS). For internal enterprise PKI, the formal CP/CPS model is often more rigorous than necessary, but the underlying policy decisions are still essential.
The policies that matter most for enterprise governance:
Algorithm and key length requirements. Which algorithms are approved for which use cases? RSA-2048 minimum for server certificates? ECDSA P-256 for workload identities? What is the migration timeline for post-quantum algorithms? These decisions must be explicit, documented, and enforced at the CA level — not left to individual teams to interpret.
Maximum certificate lifespans. Different certificate types require different lifespans. External TLS certificates are constrained by CA/Browser Forum rules (currently moving toward 47 days). Internal server certificates might be 90 days. Workload certificates in a service mesh might be 4 hours. IoT device certificates might be 2 years due to operational constraints. Each lifespan represents a risk/operations tradeoff that governance must make explicit.
SAN and naming conventions. What DNS names and IP SANs can appear on certificates issued by which CAs? Can a team request a wildcard certificate? Can a certificate contain SANs across multiple business units? Naming policy prevents the scope creep where a single certificate accumulates SANs until it becomes a cross-domain trust dependency that nobody can safely rotate.
Issuance authorization. Who can request certificates from which CAs for which domains? Self-service enrollment is operationally necessary for automation, but self-service without authorization boundaries means any team can issue certificates for any service. Role-based issuance controls — this team can issue certificates for *.api.internal.company.com, that team for *.data.internal.company.com — prevent cross-team issuance that creates ownership confusion.
Approved certificate authorities. Which CAs are authorized for which purposes? Your external TLS certificates come from DigiCert. Your internal server certificates come from your enterprise EJBCA instance. Your workload certificates come from SPIRE. Your IoT device certificates come from a dedicated manufacturing CA. Any certificate issued by a CA outside this approved list is a policy violation that should trigger an alert.
3. Lifecycle Enforcement
Policy without enforcement is documentation. Enforcement without automation is aspiration.
Lifecycle enforcement means that the policies defined above are technically enforced at the point of issuance and monitored throughout the certificate's lifespan:
Pre-issuance enforcement. The CA (or an enrollment gateway in front of it) validates every certificate request against the policy before issuance. Request has a 5-year lifespan but policy mandates 90-day maximum? Rejected. Request uses RSA-1024 but policy requires 2048 minimum? Rejected. Request includes SANs outside the requesting team's authorized scope? Rejected. This enforcement must happen automatically — human review does not scale when issuance volume exceeds thousands per day.
Post-issuance monitoring. Certificates in production are continuously compared against current policy. A certificate that was compliant when issued may become non-compliant if policy changes — for example, a new minimum key length requirement makes previously-issued RSA-2048 certificates non-compliant if policy moves to RSA-3072. Monitoring detects this drift and flags certificates for rotation.
Expiration management. Automated alerting at defined intervals before expiration (90 days, 30 days, 7 days, 1 day). Escalation paths when alerts are not acknowledged. Automatic renewal where automation is in place. Incident procedures when a certificate expires without renewal — because despite best efforts, this will happen, and the response plan must be defined before the 2 AM outage call.
Revocation procedures. Under what circumstances is a certificate revoked? Key compromise, employee departure, service decommissioning, CA compromise, algorithm deprecation. Each scenario has a different urgency and different operational impact. Governance defines the trigger conditions and the response procedures.
4. Audit and Compliance Reporting
Every governance framework must produce evidence. Auditors — internal and external — ask predictable questions, and the governance framework must answer them with data, not assertions:
How many certificates are active in your environment? The certificate inventory provides this.
What percentage have identified owners? Ownership assignment records answer this.
What is your certificate rotation cadence? Issuance and renewal logs provide this.
How quickly can you rotate all certificates using a specific algorithm? Your cryptographic inventory, cross-referenced with rotation automation coverage, determines this.
What is your process for responding to a CA compromise? Your revocation procedures and incident response plan document this.
Are there any certificates issued by unauthorized CAs? Your continuous monitoring against the approved CA list detects this.
For regulated industries, these questions are not theoretical. PCI DSS 4.0 requires documented certificate management procedures. NIS2 requires cryptographic risk management. SOX requires controls over systems that process financial data, which includes the certificates protecting those systems. Compliance with machine identity regulations increasingly means demonstrating not just that controls exist, but that they are continuously enforced and auditable. The governance framework is the mechanism that converts machine identity management into auditable, demonstrable compliance.
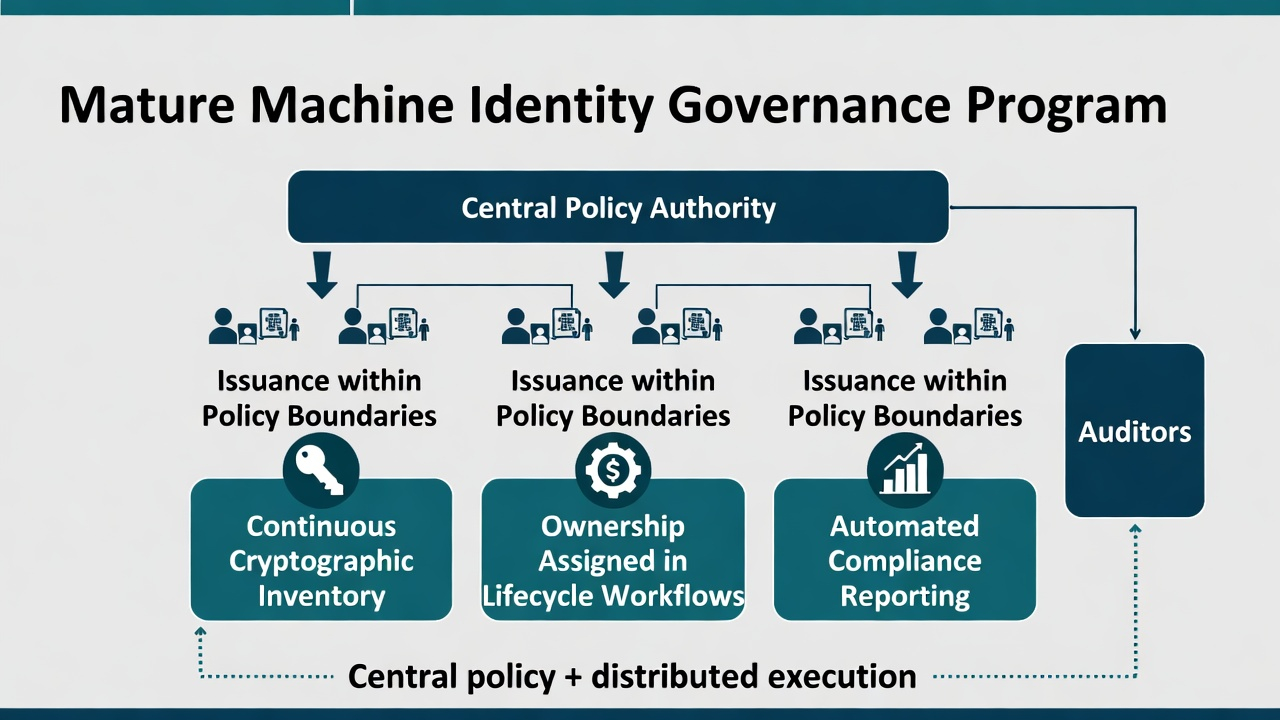
Governance in Practice: What a Mature Program Looks Like
An enterprise with mature machine identity governance operates with the following characteristics:
A central policy authority defines cryptographic standards, approved CAs, lifespan limits, and algorithm requirements. This authority does not necessarily issue certificates — it defines the rules that distributed issuance points enforce.
Distributed issuance within policy boundaries. Teams issue their own certificates through automated enrollment protocols. The CAs they use enforce the central policy. Teams have self-service capability without unrestricted issuance authority.
Continuous inventory that updates as certificates are issued, rotated, and expired. The inventory is the operational source of truth that governance relies on for enforcement and reporting.
Ownership records that are maintained as part of the certificate lifecycle, not as a separate documentation exercise. When a certificate is issued, the requesting team is recorded as the owner. When the certificate is renewed, ownership is confirmed. When the team is reorganized, ownership transfers follow.
Automated compliance reporting that produces evidence for auditors on demand, not through a quarterly manual collection exercise. The governance framework should be able to answer any auditor question with a query against the inventory and policy logs, not a research project.
This is not a technology purchase. It is an organizational capability that requires executive sponsorship (because it crosses team boundaries), defined policy (because teams need rules to follow), and operational integration (because governance that exists only in documentation is governance that does not exist). The technology — the CAs, the enrollment protocols, the monitoring tools — enables the governance. It does not constitute it.
Starting Points for Organizations Without Formal Governance
If your organization has certificates but no governance, the sequence is:
1. Appoint a machine identity owner. Not a person who manages certificates — a person or team accountable for the governance framework. This is typically within the security organization, reporting to the CISO.
2. Conduct a discovery and inventory exercise. You cannot govern what you cannot see. The inventory reveals the scope, the owners (and the gaps in ownership), and the policy violations that already exist.
3. Define minimum viable policy. Start with: approved CAs, minimum key lengths, maximum lifespans, and required ownership for all new certificates. Do not try to retroactively bring all existing certificates into compliance on day one — start with new issuance and work backward.
4. Enforce at the CA level. Configure your CAs to reject requests that violate the minimum viable policy. This is the fastest path to enforcement because it does not require changes to requesting teams' workflows — it changes what the CA will accept.
5. Integrate governance into zero trust and microsegmentation planning. Governance is not a parallel initiative — it is the control layer that makes identity-based security architectures trustworthy.
Not sure where your governance gaps are?
Ask Axel can help you assess your current certificate policy coverage and ownership gaps, or talk to us about building a governance framework from scratch.
FAQ
Who should own machine identity governance in the organization? Typically the CISO's organization, because machine identity governance is fundamentally a security and risk management function. However, operational execution — actually issuing and rotating certificates — remains distributed across platform engineering, DevOps, and infrastructure teams. Governance sets the rules; operations follows them.
How does machine identity governance differ from PKI governance? PKI governance is a subset of machine identity governance. PKI governance covers the certificate authorities, certificate policies, and certificate lifecycle. Machine identity governance extends to SSH keys, workload identities, code signing credentials, API tokens, and IoT device credentials — all non-human identity (NHI) authentication material.
What compliance frameworks and regulations require machine identity governance? PCI DSS 4.0 (Requirement 4 on cryptographic controls), NIS2 (cryptographic risk management), DORA (ICT risk management including cryptographic controls), NIST CSF 2.0 (identity management and access control), and SOX (controls over IT systems processing financial data). The specific requirements vary, but all require documented, enforceable controls over cryptographic material. Organizations operating across jurisdictions face overlapping machine identity regulations that governance frameworks must satisfy simultaneously.
How do I handle certificates that were issued before governance was established? Prioritize by risk. Start with certificates protecting critical services, certificates with no identified owner, and certificates using deprecated algorithms. Bring these into the governance framework through ownership assignment, policy compliance review, and enrollment in automated rotation. Lower-risk certificates can be addressed systematically as they approach renewal.
Device identity governance extends these principles to hardware-bound credentials. The Device Identity CTO Strategy covers the RACI model for cross-functional ownership — hardware engineering, firmware, security/PKI, manufacturing, and product leadership. For the factory-floor audit trail that feeds governance — provisioning station logging, chain of custody, and CM trust boundaries — see Factory Provisioning.
Machine Identity Management — Certificate Sprawl & Visibility — Device Identity CTO Strategy — Factory Provisioning — IoT Certificate Lifecycle. Contact Axelspire or Ask Axel.
