What Is the Matter Standard, Why It Mandates PKI, and What Matter Compliance Requires
By Dan Cvrcek, Founder, Axelspire · Updated March 2026
Part of the IoT Certificate Management pillar. This page explains what Matter really is, why it mandates per-device X.509 certificates through Matter PKI, what the Matter certification process involves, and how it aligns with the EU Cyber Resilience Act to make Matter compliance a baseline for connected products.
Matter Isn't Just Another Smart Home Protocol
Every few years, the smart home industry announces a new standard that will "finally unify everything." Most quietly disappear. Matter is different — not because it's technically perfect, but because of who is behind it, the interoperability it delivers, and what it mandates.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
The Connectivity Standards Alliance launched Matter with founding members Apple, Google, Amazon, and Samsung. These are the platform owners for HomeKit, Google Home, Alexa, and SmartThings. When all four agree on a smart home standard, manufacturers who want market access no longer have much choice.
Matter 1.0 shipped in October 2022, with an open specification and an open-source SDK. It runs over IP (WiFi, Ethernet, and Thread) and the specification has evolved rapidly: Matter 1.2 expanded device categories to include refrigerators, robot vacuums, and air quality sensors; Matter 1.3 (May 2024) added energy management devices and — critically for PKI teams — mandated CRL publication for PAIs; Matter 1.4 (November 2024) extended to batteries, solar systems, heat pumps, and home routers. Each version expands the range of devices requiring Matter-compliant PKI infrastructure.
The core commercial promise is interoperability: a Matter-certified device works with any Matter-compatible controller or ecosystem. The Matter logo signals to consumers that the product will "just work" across platforms. But the critical point for infrastructure planning is not the on-wire protocol; it is that Matter makes strong, PKI-based device identity mandatory.

The Matter PKI Mandate
Every Matter-certified device must carry a unique cryptographic identity in the form of an X.509 Device Attestation Certificate (DAC). Not a shared key, password, or opaque token — a per-device certificate chaining into a CSA-controlled trust hierarchy. This is the core of Matter PKI: a mandatory public key infrastructure that every device must participate in.
During commissioning, the Matter commissioner (phone app or hub) verifies the DAC against the CSA's Distributed Compliance Ledger (DCL), cross-checking the Vendor ID and Product ID embedded in the certificate against the registered, certified product entries. If the chain does not validate — because the PAA is untrusted, the Vendor ID / Product ID combination is uncertified, or revocation applies — the device does not join the network.
The Matter Certificate Policy (CP) governs how all CAs in the Matter PKI must operate. Every PAA operator must submit a Certificate Practice Statement (CPS) detailing how they meet the CP requirements, and must pass compliance audits before their PAA certificate is listed on the DCL. This is not a self-declaration — it's a formal PKI governance framework comparable to the WebTrust or ETSI audit programs that govern public TLS certificate authorities.
This means achieving Matter compliance from a PKI perspective requires:
- A certificate authority hierarchy compliant with the Matter Certificate Policy: either operate your own PAA under CSA oversight or use an approved PAA provider.
- Per-device certificate provisioning during manufacturing, at factory-line speeds, with each DAC containing the correct Vendor ID and Product ID.
- Manufacturing-integrated PKI with secure key generation, signing, and storage rooted in HSMs.
- A Certificate Practice Statement approved by the CSA's PKI Policy Authority, with ongoing audit compliance.
- CRL-based revocation support for PAIs, published into the DCL from Matter v1.3 onward.
For a deeper look at the hierarchy itself — PAAs, PAIs, and DACs — see Matter Device Attestation Certificates: PAA, PAI, and DAC Hierarchy Explained.
The EU Cyber Resilience Act Adds Legal Force
If Matter creates the commercial obligation for device PKI, the EU Cyber Resilience Act (CRA) creates the legal one.
CRA requires products with digital elements placed on the EU market to implement security-by-design throughout their lifecycle, including strong authentication, unique device identification, and vulnerability management.
- 11 September 2026: vulnerability and incident reporting obligations begin.
- 11 December 2027: full compliance required; non-compliant products cannot be sold in the EU.
- Penalties: up to €15 million or 2.5% of global turnover.
CRA does not name X.509 certificates explicitly, but the requirements effectively push you toward PKI-backed device identity if you want to demonstrate that you know which devices are impacted by a vulnerability and can address them over their supported lifetimes.
For organisations already pursuing Matter certification, the CRA's obligations largely align with the Matter-compliant device identity infrastructure you must build anyway. The reverse is not guaranteed: you can be CRA-compliant without Matter, but you cannot achieve Matter compliance without building something that looks very much like an enterprise-grade PKI for devices.
The Matter Certification Process
Matter certification is the formal process through which a product is validated for interoperability, security, and reliability within the Matter ecosystem. Only Matter-certified devices can carry the Matter logo — the consumer-facing mark that signals cross-platform compatibility.
The Matter certification process involves:
- CSA membership. Manufacturers must join the Connectivity Standards Alliance at the appropriate membership tier (Associate, Adopter, or Participant).
- Vendor ID and Product ID registration. Each manufacturer receives a unique Vendor ID; each product line gets a Product ID. These are embedded in every DAC and validated during commissioning.
- Matter PKI setup. Establish your PAA (own or third-party), provision PAIs per product family, and integrate per-device DAC provisioning into manufacturing.
- Pre-certification testing. Use the CSA's Test Harness to validate interoperability and protocol compliance before submitting to an Authorized Test Lab.
- Formal certification testing. CSA-approved Authorized Test Labs (ATLs) conduct the official compliance tests covering interoperability, security, and specification adherence.
- DCL registration. Certified products are registered on the Distributed Compliance Ledger, making their attestation information available to commissioners.
Matter compliance is not a one-time event. Each firmware update, new product variant, or specification version upgrade may require recertification — though CSA's Rapid Recertification and Matter FastTrack programs streamline this for incremental changes.
What This Means for Your Budget
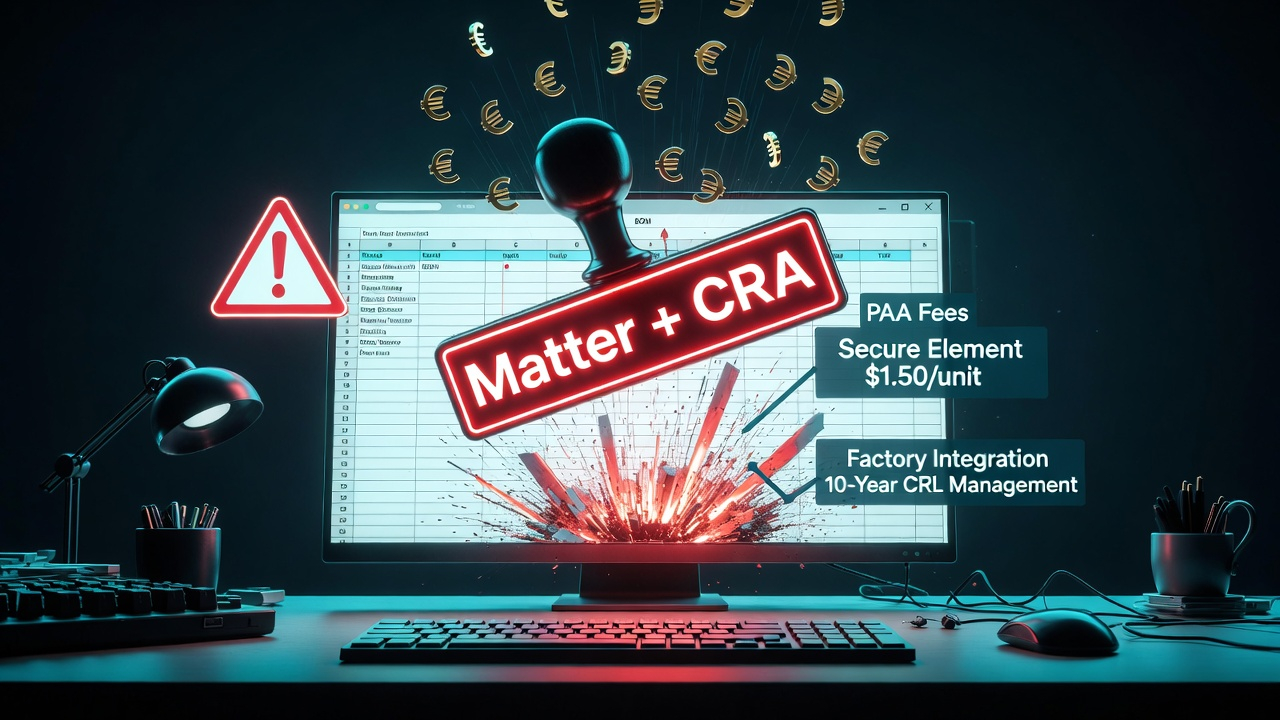
Matter and CRA together move certificate infrastructure from "nice to have" to a mandatory cost of doing business for connected smart home products — and increasingly for industrial IoT as well.
Key cost categories for building Matter-compliant infrastructure include:
- PAA/PAI infrastructure or services: HSMs, key ceremonies, CPS documentation, audits, or managed CA fees from providers like DigiCert, Kudelski IoT, or Nexus.
- Key storage: secure elements such as ATECC608C or software key storage plus the monitoring needed to compensate.
- Manufacturing integration: provisioning stations, factory connectivity, and processes with contract manufacturers — each DAC must contain the correct Vendor ID and Product ID.
- Lifecycle operations: CRLs, DCL integration, monitoring, incident response, and certificate rollover for long-lived Matter-compliant fleets.
- Matter certification costs: CSA membership fees, ATL testing, documentation, and recertification for firmware updates and specification version changes.
- CRA compliance and audit: documentation, vulnerability reporting processes, and periodic reviews.
None of these costs show up as a single line item in a BOM spreadsheet. They appear across security, engineering, manufacturing, and legal budgets, which is why they tend to be underestimated until very late in product development.
The Strategic Decisions You Need to Make Now
If you plan to ship Matter-certified products or sell connected devices into EU markets after 2027, you must make several interlocking decisions:
- Build or buy your PAA? Decide whether you will operate a PAA (with CPS, audits, and ongoing Matter Certificate Policy compliance) or rely on a CSA-approved provider.
- Hardware or software key storage? As covered in IoT Secure Element vs Software Key Storage, this choice sets your monitoring and incident response trajectory.
- Cloud platform or independent infrastructure? As explored in IoT Device Identity Certificates: Who Owns Them, cloud-native IoT services are convenient but can create deep lock-in around device identities.
- Provisioning protocol and lifecycle design? See The IoT Certificate Lifecycle Nightmare for why SCEP, EST, ACME, and traditional revocation look different on constrained devices.
These decisions are tightly coupled. Making them independently — hardware vs software keys, platform vs independent CA, provisioning protocol vs renewal design — creates architectural debt that compounds with every production run.
Next Steps
To move from awareness to architecture:
- Understand the Matter PKI hierarchy in detail via Matter Device Attestation Certificates: PAA, PAI, and DAC Hierarchy Explained.
- Map the full IoT device certificate lifecycle through The IoT Certificate Lifecycle Nightmare.
- Make the key storage decision early with IoT Secure Element vs Software Key Storage.
- Evaluate platform dependency in IoT Device Identity Certificates: Who Owns Them.
- Review the Hardware-Backed Device Identity Implementation Guide for SE/TPM part selection, certificate hierarchies, and secure boot chain integration.
- Understand factory-floor options in Factory Provisioning — which model keeps DAC private keys most secure.
If you want a concrete view of what your Matter-compliant certificate infrastructure needs to look like for your roadmap and markets, talk to Axelspire about an assessment.
Related Axelspire Content
- IoT Certificate Management — Pillar overview
- Hardware-Backed Device Identity — SE/TPM selection, Matter PKI hierarchies, secure boot
- Factory Provisioning — On-device keygen, pre-provisioned SE, key injection
- Device Identity CTO Strategy — CRA, Cyber Trust Mark, TCO, RACI
- PKI Trust Models Explained
- ACME Protocol Enterprise Guide
- Post-Quantum TLS Impact
