IoT Certificate Management: Why Your Enterprise PKI Strategy Doesn't Scale to 100,000 Devices
By Dan Cvrcek, Founder, Axelspire · Updated March 2026
This page is the pillar for the IoT Certificate Management cluster. If you are new to the topic, start here, then continue to the detailed guides on Matter and PKI, Matter Device Attestation Certificates, the IoT certificate lifecycle, hardware vs software key storage, and device identity ownership and vendor lock-in. For hardware-backed implementation details — SE/TPM selection, factory provisioning, and CTO-level strategy — see the Device Identity Implementation Guide. For how IoT fits into the broader non-human credential estate, see machine identity management.
PKI for IoT doesn't work like PKI for servers. The protocols are similar, the cryptographic primitives are the same, but the operational constraints are different enough that enterprise approaches to IoT device certificate management fail predictably — and expensively — when applied to device fleets at manufacturing scale. If you've heard the term IoT PKI and assumed it's just enterprise PKI applied to smaller endpoints, this guide explains why that assumption breaks down.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
This guide covers the full IoT device certificate lifecycle: from manufacturing-stage provisioning through renewal, revocation, and monitoring across heterogeneous device fleets. Whether you're shipping consumer Matter devices, industrial sensors, or building management controllers, the architectural decisions are the same — and most organisations make them too late.
Two regulatory forces are converging in 2026–2027 that will force every IoT device manufacturer and every enterprise deploying connected devices to fundamentally rethink their certificate infrastructure.
Network operators and enterprise teams running their own Matter fabrics face an equally significant challenge: they inherit full responsibility for ongoing operational PKI—renewal, revocation, and monitoring—once devices are deployed in their environments.
The Certificate Obligation Nobody Budgeted For
The Matter standard, developed by the Connectivity Standards Alliance (CSA) and backed by Apple, Google, Amazon, and Samsung, now mandates X.509 Device Attestation Certificates for every device carrying the Matter badge. Not optional. Not recommended. Required. Every thermostat, door lock, light bulb, and sensor that wants Matter certification needs a unique cryptographic identity provisioned during manufacturing.
The EU Cyber Resilience Act, Regulation 2024/2847, which entered into force on 10 December 2024, requires products with digital elements to implement security-by-design—including unique device identification and vulnerability management throughout the product lifecycle. Reporting obligations kick in 11 September 2026, with full compliance required by 11 December 2027. Fines reach up to €15 million or 2.5% of global turnover.
Together, these two forces mean that organisations shipping connected products into consumer and enterprise environments are now legally and commercially obligated to operate certificate infrastructure at device scale. And most of them haven't started planning. The same obligations are converging on industrial IoT (IIoT) and operational technology (OT) environments through IEC 62443 and NIS2, where certificate-based device identity is increasingly a compliance requirement rather than a best practice.
Why Enterprise PKI Doesn't Transfer to IoT PKI
If you've spent the last decade managing certificates for servers, applications, and web infrastructure, you understand X.509, chain of trust, and lifecycle management. That's necessary but insufficient for IoT. The gap between enterprise PKI and IoT PKI isn't in the cryptography — it's in the operational model.
Your servers have reliable network connectivity. IoT devices have intermittent WiFi, cellular connections that drop during firmware updates, and factory environments where network provisioning happens offline. The ACME protocol that works brilliantly for server certificate automation assumes the endpoint can reach a CA server on demand. Most IoT devices can't guarantee that.
Your servers have abundant compute and storage. A typical web server has gigabytes of RAM and terabytes of storage. An IoT sensor might have 512KB of RAM and 2MB of flash. Running a full TLS stack with OCSP checking and CRL caching is architecturally impossible on constrained devices. The revocation mechanisms that enterprise PKI relies on simply don't work at device scale.
Your certificate estate is measured in thousands. Enterprise certificate management—even at large organisations—typically involves 10,000–100,000 certificates. IoT deployments routinely involve millions. The CA/Browser Forum's reduction of public certificate lifetimes already strains enterprise operations. Multiply that renewal frequency by 100x device count on endpoints that may not be online when renewal is needed, and the model collapses.
Your renewal process assumes human intervention is available. When a server certificate fails to renew, an engineer SSH's into the box and fixes it. When a smart lock's certificate expires, the customer's front door stops working. The failure mode isn't a ticket in ServiceNow—it's a product recall.
The Diverse Fleet Problem: Protocols, Chipsets, and Multi-Vendor Reality
The challenges above assume a uniform device fleet. Reality is worse. Most organisations managing IoT device certificate infrastructure are dealing with heterogeneous environments: different chipsets with different cryptographic capabilities, different operating systems (RTOS, Linux, bare-metal), different enrollment protocols (EST, SCEP, ACME, CMPv2), and different connectivity profiles ranging from always-on WiFi to battery-powered devices that wake once per day.
Enforcing consistent certificate policy across this diversity is the operational problem that scales worst. A certificate rotation that works over EST on a Linux-based gateway doesn't work on a constrained Zigbee sensor behind a Thread border router. A renewal workflow designed for devices with reliable cloud connectivity fails for equipment deployed in shielded industrial environments or on vessels at sea. Each device class effectively needs its own enrollment and renewal pathway, multiplying the engineering surface that must be built, tested, and maintained. The goal of centralized IoT certificate management — a single pane of glass across every device type and deployment environment — is architecturally sound but operationally difficult without protocol abstraction layers that handle device heterogeneity.
This is why IoT device certificate management is fundamentally a fleet orchestration problem, not a PKI problem. The cryptography is the easy part. The hard part is ensuring that every device type in your fleet — across every contract manufacturer, every firmware variant, every deployment environment — has a viable path through the full certificate lifecycle without human intervention at device level.
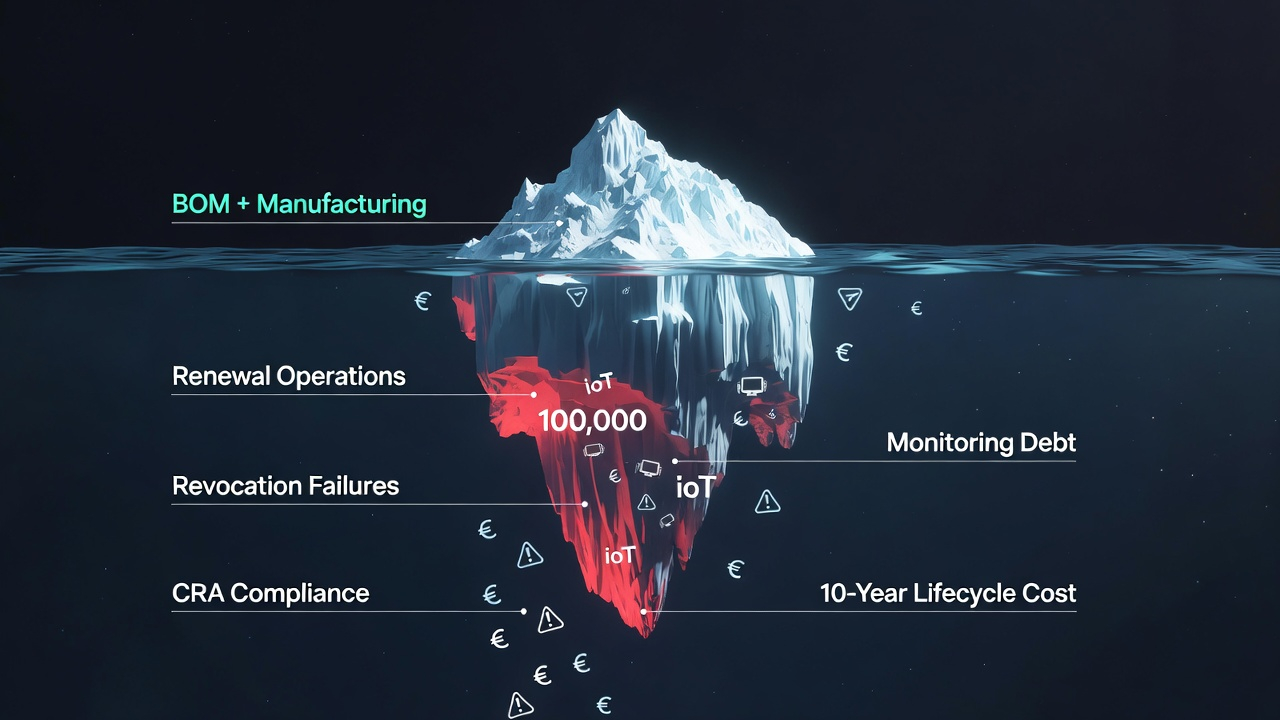
The Cost Nobody's Counting
We've written extensively about the invisible infrastructure tax—the $4–11M that mid-to-large enterprises spend annually on manual certificate management through fragmented labour that appears nowhere in budgets. IoT amplifies this tax in three ways.
Linear scaling with device count. Every certificate management process that requires human attention—provisioning, monitoring, renewal troubleshooting, revocation—scales linearly with the number of devices. Ship 100,000 units and you've created 100,000 certificate lifecycle obligations that persist for the product's entire supported lifetime.
Manufacturing integration complexity. Certificate provisioning must happen during manufacturing, which means your PKI infrastructure needs to integrate with factory floor systems, potentially across multiple contract manufacturers in different countries. This isn't a one-time integration—it's an ongoing operational relationship that requires secure key distribution to manufacturing partners.
Post-deployment monitoring at scale. With software-based key storage, device certificates can be extracted and cloned. Monitoring for compromised or counterfeit devices requires certificate telemetry infrastructure that most organisations haven't built. The vendor lock-in implications of choosing a cloud platform for this monitoring are significant and often irreversible.
Post-Quantum Cryptography: The Compounding Factor Most Teams Aren't Planning For
Every architectural decision you make today about IoT certificate infrastructure will be tested by the migration to post-quantum cryptography. PQC doesn't create a separate problem — it compounds every existing IoT certificate challenge.
Larger keys and certificates on constrained hardware. ML-DSA (the NIST-standardised post-quantum signature algorithm) produces certificates roughly 10–15x larger than their ECDSA equivalents. For a device with 2MB of flash that already stores firmware, configuration, and a certificate chain, this isn't a trivial increase — it may require hardware redesign. Hybrid certificates that bundle both classical and PQC algorithms are even larger.
Slower handshakes on low-bandwidth connections. PQC key exchange and signature verification take more compute cycles and transmit more data. On devices communicating over constrained radio links (Thread, LoRaWAN, NB-IoT), the increased handshake size can push TLS session establishment into timeout territory. Protocol-level changes to TLS 1.3 are still being standardised, and many IoT TLS stacks won't receive updates.
Devices shipped today may become stranded assets. This is the critical planning implication: if a device's hardware cannot support PQC key sizes, and its firmware update mechanism doesn't allow algorithm replacement, that device will be unable to migrate to quantum-safe certificates when the transition becomes mandatory. The crypto library you choose, the key storage architecture you design, and the firmware update pathway you build now determine whether your fleet can make that transition in 5–10 years — or whether those devices need to be physically replaced.
For organisations designing PKI for IoT today, the practical implication is clear: build for crypto-agility. Select hardware with headroom for larger keys. Use certificate enrollment protocols that support algorithm negotiation. Design firmware update mechanisms that can deliver new crypto libraries. The cost of retrofitting PQC onto devices that weren't designed for it is 10–50x the cost of building the flexibility in at design stage.
What This Guide Covers: Five Decisions That Determine Whether Your IoT Certificate Infrastructure Scales
If you're building PKI for IoT from scratch, inheriting a device fleet through acquisition, or retrofitting certificate infrastructure onto products that shipped without it, these are the five architectural decisions you'll face — roughly in this order. Each decision constrains the ones that follow, and getting the sequence wrong creates compounding lifecycle debt that becomes visible only after devices are in the field. If you're looking to implement enterprise PKI for IoT, this sequence is the implementation framework.
1. What Is the Matter Standard and Why It Mandates PKI
The entry point. What Matter actually requires, why PKI is non-negotiable, and what the CRA adds to the picture. If you're a product manager or CTO who's heard "we need Matter certification" but hasn't yet understood the PKI implications, start here. Also relevant for IIoT teams evaluating IEC 62443 requirements, where the certificate-based identity mandates follow a similar pattern.
2. Matter Device Attestation Certificates: PAA, PAI, and DAC Hierarchy Explained
The Matter-specific PKI hierarchy—Product Attestation Authorities, Product Attestation Intermediates, and Device Attestation Certificates—explained for enterprise PKI teams who understand X.509 but haven't encountered device attestation. Bridges to our PKI trust models analysis.
3. The IoT Certificate Lifecycle Nightmare: Provisioning, Renewal, and Revocation at Scale
The operational heart of the cluster. Why SCEP works brilliantly for day-zero provisioning but creates compounding lifecycle debt. How renewal breaks when devices can't call home. Why CRLs and OCSP choke on constrained endpoints. Covers protocol selection (EST, SCEP, ACME, CMPv2) across diverse device types — the practical answer to enforcing certificate updates across heterogeneous IoT environments. Certificate lifecycle is the core component of broader IoT lifecycle management: without working certificate infrastructure, firmware updates, secure decommissioning, and compliance reporting all break.
4. Hardware vs Software Key Storage: The Decision That Shapes Your Monitoring Architecture
The architectural fork that determines everything downstream. Secure elements like Microchip's ATECC608C and Infineon's OPTIGA Trust create hardware-bound device identity where compromise means physical access. Software keystores are cheaper but create a fundamentally different threat model that requires more expensive monitoring. This isn't a BOM line item—it's an architectural commitment that also determines your PQC migration options.
5. IoT Device Identity Certificates: Who Owns Them and Why Platform Choice Matters
AWS IoT Core, Azure IoT Hub, and Google Cloud all offer managed device certificate services. They also all create structural dependencies where your device identities live inside a platform you don't control. The same vendor lock-in analysis we apply to CLM platforms, applied to IoT—plus why retrofitting device identity onto already-shipped units is 10–20x more expensive than manufacturing-stage integration.
Who This Is For
Product leaders and CTOs evaluating Matter certification or CRA compliance timelines. You need to understand the PKI infrastructure obligation before you commit to a product roadmap.
Enterprise security teams inheriting IoT device fleets through acquisition, partnership, or internal product development. Your existing PKI expertise is valuable but incomplete for device-scale operations — whether those devices are consumer Matter products, industrial sensors on a factory floor, or building management controllers in a commercial property portfolio.
Manufacturing and supply chain leaders who need to understand why certificate provisioning isn't just "another step in the factory process"—it's a security-critical operation that requires HSM infrastructure, key distribution protocols, and ongoing audit.
IIoT and OT security teams managing certificate infrastructure across industrial control systems, SCADA networks, and connected equipment where device lifetimes are measured in decades and firmware updates are operationally constrained. The IoT PKI challenges are structurally identical to consumer IoT but with longer time horizons, stricter availability requirements, and regulatory frameworks (IEC 62443, NIS2) that are converging with the consumer-side mandates.
The Axelspire Perspective
We're currently building integration infrastructure for a Fortune 50 IoT platform—a deployment involving millions of device certificates, HSM-backed key management, and manufacturing-integrated provisioning pipelines. We know what works at this scale because we're building it.
Our core thesis applies to IoT just as it applies to enterprise certificate management: you have an operational problem, not a tooling problem. Buying a platform doesn't solve IoT certificate management. Understanding your certificate flows, your key storage architecture, and your monitoring requirements—then automating based on that understanding—is what actually works.
Want to understand where your IoT certificate infrastructure stands? Talk to us about an assessment.
External References
- Connectivity Standards Alliance — Matter
- Matter SDK on GitHub
- EU Cyber Resilience Act — Official Summary
- IEC 62443 — Industrial Cybersecurity Standard
- Thread Group
- NIST Post-Quantum Cryptography
Related Axelspire Content
- Hardware-Backed Device Identity — SE/TPM selection, certificate hierarchies, fleet-scale lifecycle
- Device Identity CTO Strategy — TCO, regulatory compliance (CRA, Cyber Trust Mark), build vs buy
- Factory Provisioning — Three provisioning models, CM trust boundaries
- SPIFFE & Workload Identity for Device Fleets — Trust domains, edge agents, hybrid identity
- The Real Cost of Certificate Management
- PKI Trust Models Explained
- ACME vs Traditional Protocols
- Keyfactor vs Venafi
- HashiCorp Vault PKI Guide
- Post-Quantum TLS Impact
