Hardware-Backed Device Identity: Implementation Guide
Every device identity architecture starts with the same question: where does the private key live? The answer determines the security ceiling of the entire system. Software keys in flash storage can be extracted by anyone with JTAG access or a firmware dump. Hardware-backed keys in a secure element or TPM cannot be extracted — period. The key is generated inside the silicon, used inside the silicon, and never leaves.
This guide covers the practical implementation of hardware-backed device identity: secure element and TPM selection for different device classes, Matter PKI and xPKI certificate hierarchies, secure boot chain integration, fleet-scale certificate lifecycle operations, and PKI throughput benchmarks for manufacturing line rates.
Related: CTO Strategy & Business Case · Factory Provisioning · SPIFFE & Workload Identity · Private CA Platform Comparison
Secure element and TPM selection
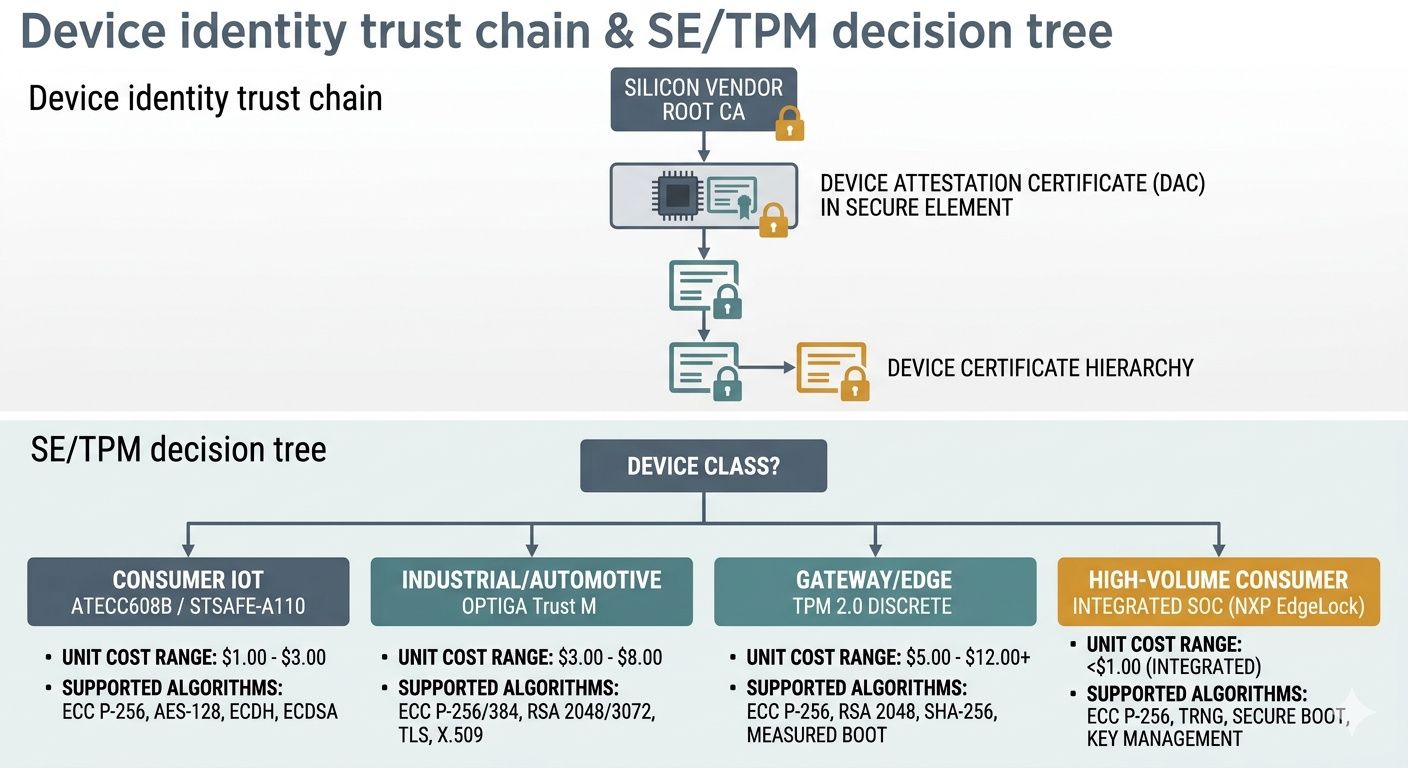
The choice between a discrete secure element, a TPM, or an integrated security subsystem depends on the device class, the protocol ecosystem (Matter, OPC UA, custom), cost sensitivity, and supply chain constraints.
| Part | Type | Best for | Unit cost (10K qty) | Key algorithms |
|---|---|---|---|---|
| ATECC608B | SE (Microchip) | Matter, cost-sensitive IoT | ~$0.50–0.80 | ECC P-256 |
| OPTIGA Trust M | SE (Infineon) | Industrial, automotive | ~$1.00–2.50 | ECC P-256/384, RSA 2048 |
| STSAFE-A110 | SE (ST) | Consumer, Matter | ~$0.60–1.20 | ECC P-256/384 |
| TPM 2.0 (discrete) | TPM (various) | Gateway, edge, enterprise | ~$2.00–5.00 | ECC, RSA, SHA-256/384 |
| Integrated (e.g., NXP EdgeLock) | SoC subsystem | High-volume consumer | Included in SoC | Varies by SoC |
For detailed hardware vs software key storage trade-offs, see Hardware vs Software Key Storage.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
Certificate hierarchies: Matter DAC and xPKI
Matter PKI uses a three-tier hierarchy: Product Attestation Authority (PAA) → Product Attestation Intermediate (PAI) → Device Attestation Certificate (DAC). The DAC is stored in the device's SE during manufacturing and proves the device is a genuine product from a certified manufacturer. For Matter-specific details, see Matter Device Attestation Certificates and Matter Standard PKI.
xPKI (extended PKI) refers to custom device certificate hierarchies outside Matter — proprietary product ecosystems, OPC UA industrial identity, fleet management certificates. The hierarchy design follows the same principles: offline root CA → online issuing CA → device certificate, with the issuing CA sized for manufacturing throughput.
Regardless of the hierarchy, the factory provisioning process determines whether the private key is genuinely hardware-bound. See Factory Provisioning for the three provisioning models and their security implications.
Secure boot chain integration
Device identity certificates are one half of the trust story. The other half is ensuring the software running on the device is the software the manufacturer intended. Secure boot ties the two together: the device's SE/TPM verifies the firmware signature at boot, establishing a chain of trust from silicon to application. Without secure boot, a valid device certificate on compromised firmware is a signed lie.
The implementation pattern: the bootloader verifies the kernel image signature using a public key stored in SE/TPM OTP fuse, the kernel verifies application image signatures, and the application uses the device certificate for network authentication. Each layer attests the next. Breaking any link in the chain prevents the device from obtaining network credentials.
Fleet-scale certificate lifecycle
Manufacturing provisions the initial certificate. Field operations must handle rotation, revocation, and monitoring across the entire fleet. The IoT Certificate Lifecycle guide covers the full provisioning → renewal → revocation workflow. Key operational considerations:
- Rotation at scale: OTA certificate renewal for 100K+ devices requires rate limiting, regional staggering, and retry logic. A CA that can sign 50 certificates/second handles 180K/hour — sufficient for most fleet sizes with proper scheduling.
- Revocation: CRL distribution to constrained devices is problematic (CRLs grow with every revocation). OCSP stapling or short-lived certificates (≤24 hours) with no revocation infrastructure are the modern alternatives.
- Monitoring: Certificate expiration across the fleet must be tracked centrally. The Certificate Sprawl & Visibility patterns apply to device fleets as much as to enterprise TLS.
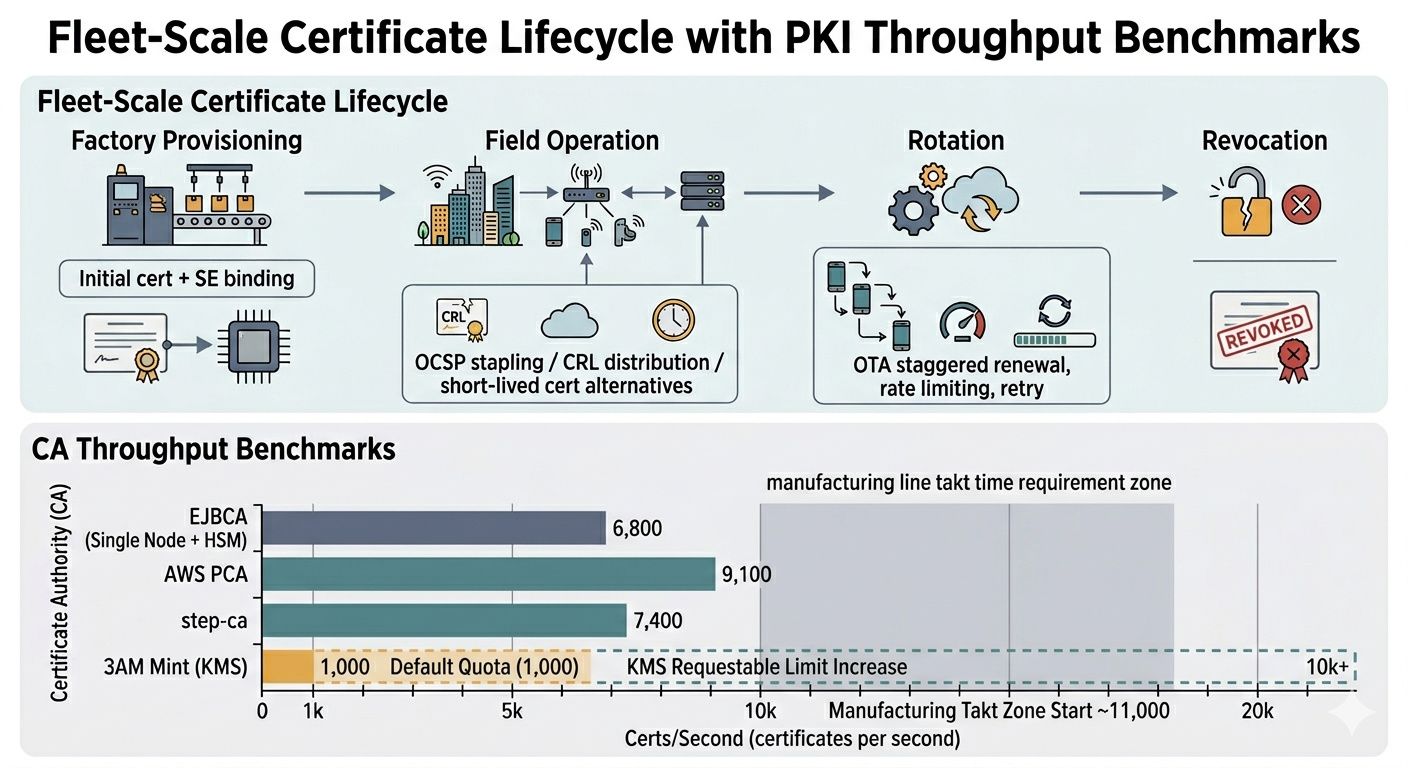
PKI performance for manufacturing
Manufacturing lines run at fixed takt times. If certificate issuance cannot keep pace, it becomes the bottleneck. The CA platform choice matters here — see Private CA Platform Comparison for throughput benchmarks across platforms. For device-specific CA requirements, 3AM Mint provides KMS-backed signing at effectively unlimited throughput (KMS scales horizontally), while EJBCA is the traditional choice for on-premises manufacturing PKI with HSM integration.
Vendor lock-in and portability
The SE/TPM silicon vendor is a 10+ year commitment — the device's hardware identity is bound to that part for the product's lifetime. Certificate hierarchy portability is equally important: can you move from one CA platform to another without re-provisioning the fleet? See Vendor Lock-in & Device Identity for the portability analysis.
CTO Strategy & Business Case — Factory Provisioning — SPIFFE & Workload Identity — Matter DAC — Hardware vs Software Keys — IoT Certificate Lifecycle — Private CA Comparison — Machine Identity & Zero Trust. Contact Axelspire or Ask Axel.
