Device Identity for CTOs: Strategy, TCO, and Regulatory Compliance
Hardware-backed device identity is a capital investment. Secure elements add $0.50–5.00 per device to the BOM. PKI infrastructure requires licensing, operations, or both. The engineering effort is non-trivial. None of this is optional when regulation mandates it — the EU Cyber Resilience Act and US Cyber Trust Mark are converting device identity from competitive advantage to market access requirement.
This guide frames the decision for CTOs and technical executives: what it costs, what it prevents, when regulation forces the timeline, who owns what, and how to measure whether the programme is working.
Related: Implementation Guide (technical details) · Factory Provisioning · SPIFFE & Workload Identity
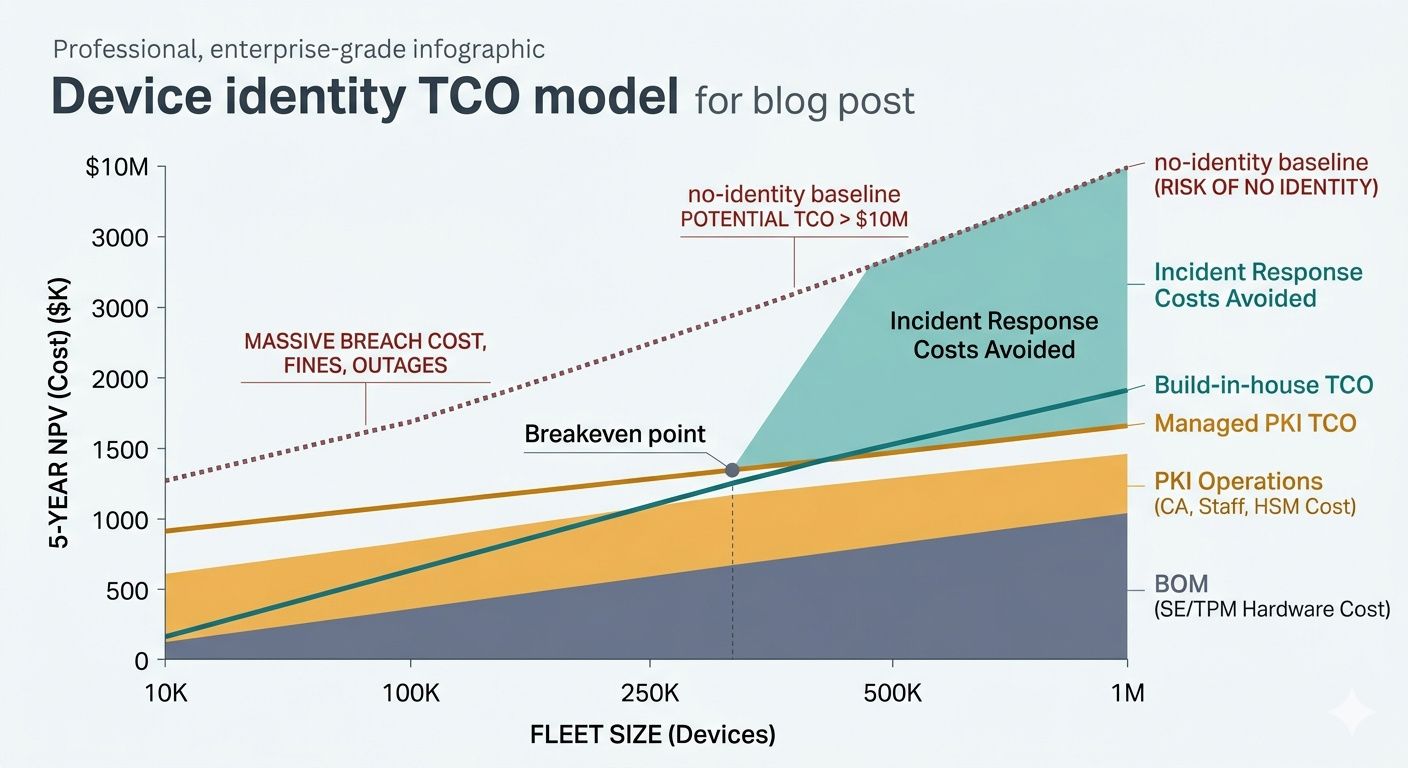
Total cost of ownership
Per-device hardware cost
Secure element or TPM: $0.50–5.00 per unit depending on part selection (see the implementation guide for specific parts and pricing). PCB area: 2–6mm² for an SE in QFN or WLCSP package. Additional passives (decoupling capacitors, pull-up resistors): $0.02–0.05. At 100K units/year, the BOM impact is $50K–500K — amortised across the product's revenue, this is typically 0.1–1% of unit cost.
PKI infrastructure cost
Certificate issuance at manufacturing scale requires a CA platform that can keep pace with the production line. Options range from self-managed (EJBCA + HSM: $50K–200K setup plus 0.5–1 FTE ongoing) through managed cloud (AWS PCA: $400/mo per CA plus per-certificate fees) to serverless (3AM Mint: near-zero AWS infrastructure cost plus licensing). See Private CA Platform Comparison for the full cross-platform TCO analysis.
Incident response cost avoided
The cost of not having device identity is measured in incident response: cloned devices, firmware tampering, fleet-wide credential resets, regulatory fines, and brand damage. A single device compromise incident in a connected medical device or industrial control system routinely exceeds $1M in direct costs. Hardware-backed identity doesn't eliminate all incidents — it eliminates the class of attacks that depend on extracting or cloning device credentials.
PKI Health Radar
Drag the sliders to assess your current posture — scores update instantly.
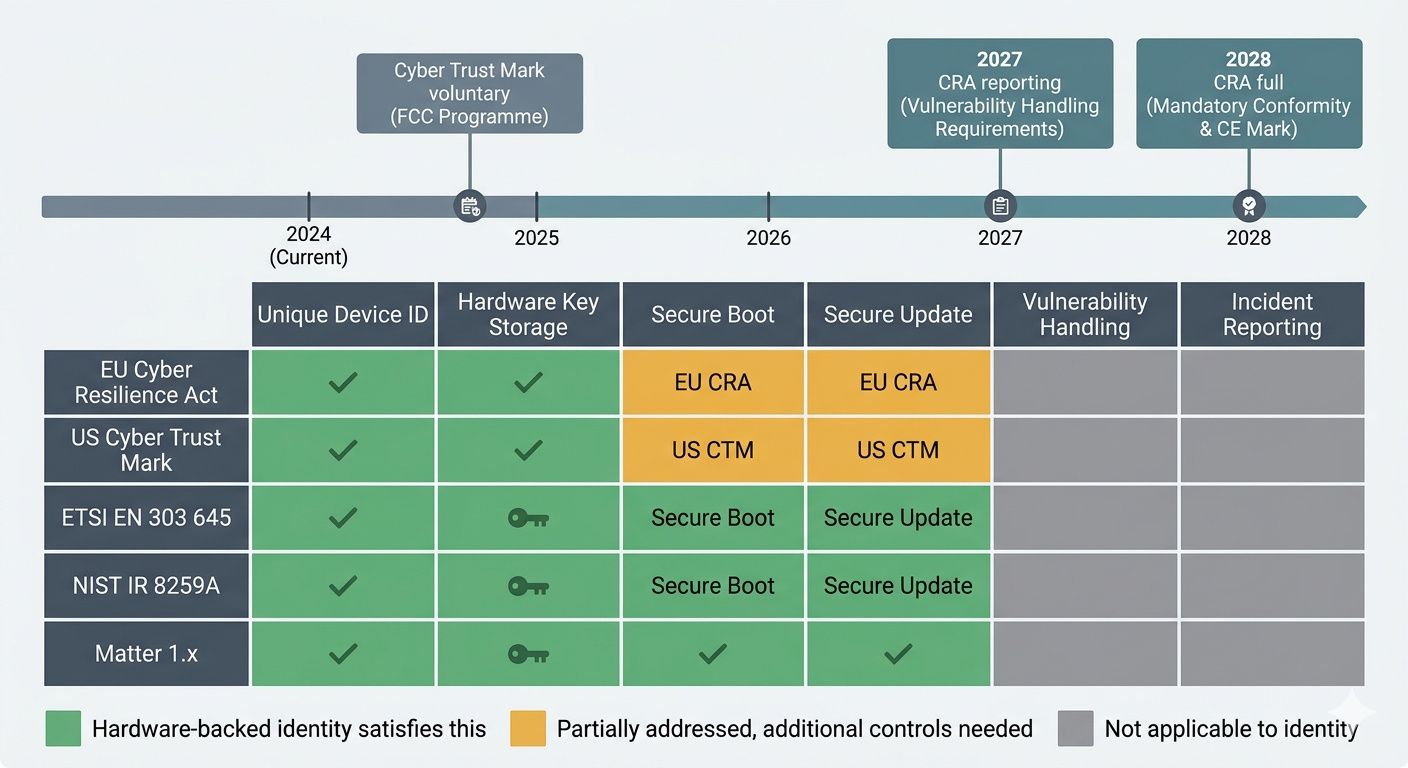
Regulatory landscape
| Regulation | Scope | Device identity requirement | Enforcement timeline |
|---|---|---|---|
| EU Cyber Resilience Act | All products with digital elements sold in EU | Unique identification, secure update mechanisms, vulnerability handling | 2027 (reporting) / 2028 (full) |
| US Cyber Trust Mark | Consumer IoT sold in US | Unique device identification, secure communication | Voluntary (market pressure) |
| ETSI EN 303 645 | Consumer IoT (EU baseline) | Unique per-device credentials, no default passwords | Referenced by CRA |
| NIST IR 8259A | US federal IoT procurement | Device identification, logical access controls | Federal procurement requirement |
| Matter 1.x | Smart home ecosystem | DAC in SE/TPM, PAA→PAI→DAC chain | Required for certification |
For Matter-specific PKI requirements, see Matter Device Attestation Certificates and Matter Standard PKI.
Organisational ownership: RACI
| Activity | Hardware Eng | Firmware Eng | Security / PKI | Manufacturing | Product / CTO |
|---|---|---|---|---|---|
| SE/TPM part selection | R | C | A | I | I |
| Certificate hierarchy design | I | C | R | I | A |
| Factory provisioning | C | R | C | A | I |
| CA platform selection | I | C | R | C | A |
| Fleet certificate lifecycle | I | C | R | I | A |
| Regulatory compliance | C | C | C | C | R/A |
PKI operations engineers who can set up and operate a CA, manage certificate lifecycle, and handle incident response. The implementation guide covers why general-purpose enterprise PKI does not work for device issuance — device PKI has different scale and performance characteristics.
Programme KPIs
- Provisioning success rate: % of devices leaving factory with valid certificate > 99.9%
- Provisioning throughput: devices/hour vs production line takt time — CA must not be the bottleneck
- Certificate coverage: % of active fleet with valid, non-expired certificates
- Rotation compliance: % of fleet with certificates rotated within policy window
- Incident detection time: time from certificate anomaly to alert — target <15 minutes
- Regulatory readiness: compliance gap closure against CRA/Cyber Trust Mark requirements
Build vs buy
Build in-house when the organisation has PKI expertise, hardware security engineering depth, and the device fleet justifies dedicated infrastructure. Expect 6–12 months to production-ready, 0.5–1 FTE ongoing.
Buy / managed when time-to-market matters, PKI is not a core competency, or regulatory timelines force faster deployment. 3AM Mint eliminates CA operations; silicon vendors' pre-provisioned secure elements (Microchip Trust Platform, Infineon OPTIGA Trust) reduce factory-floor integration. The trade-off is vendor dependency — see Vendor Lock-in & Device Identity.
Implementation Guide — Factory Provisioning — SPIFFE & Workload Identity — Matter DAC — Vendor Lock-in — Private CA Comparison — Machine Identity Governance. Contact Axelspire or Ask Axel.
